SOC 2 is a security framework developed by AICPA that refers to controls at a service organization relevant to security, availability, integrity, confidentiality and privacy.
Hence, SOC 2 refers to both the security framework and the audit that checks whether a company is compliant with SOC 2 requirements.
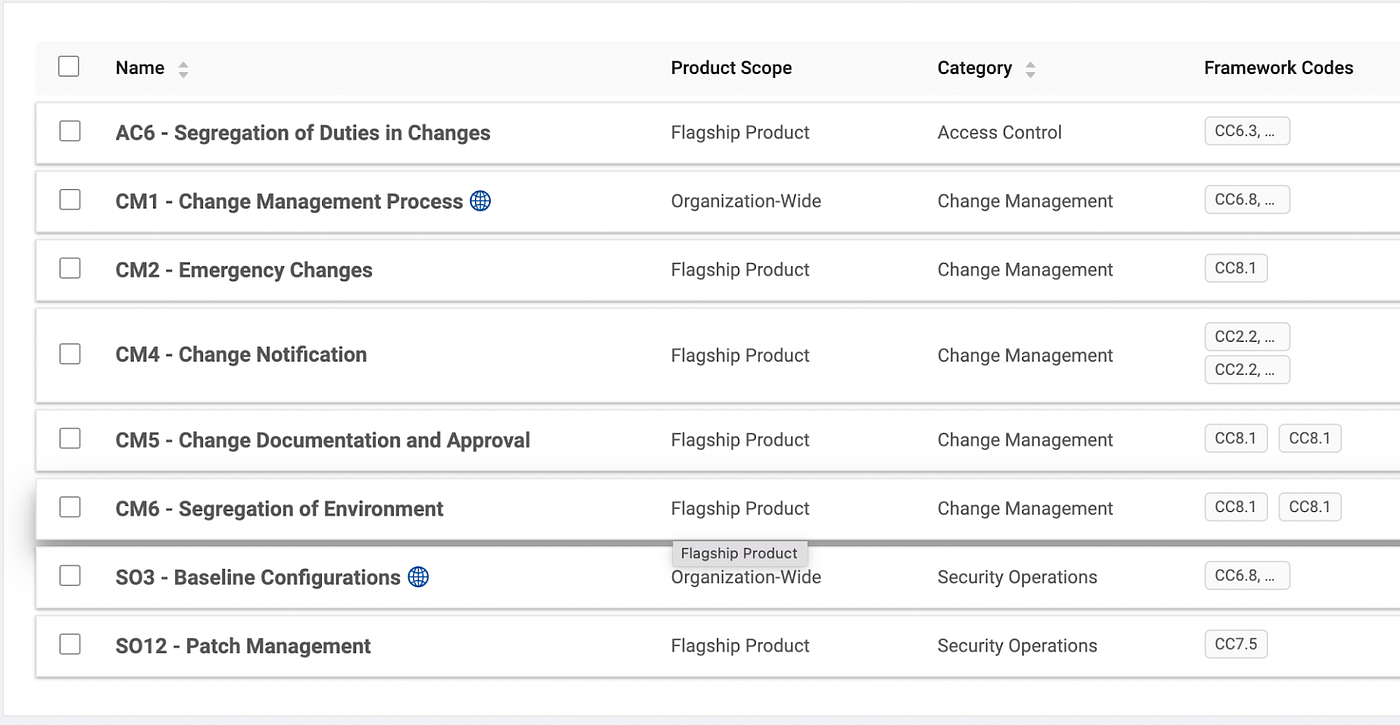
During a SOC 2 audit, the company needs to provide evidence for controls needed for each policy. For example, if the company has a policy for “Change Management” then it will need to provide evidence for controls like “Segregation of Environment”, “Change Notification”, “Change Documentation and Approval”.
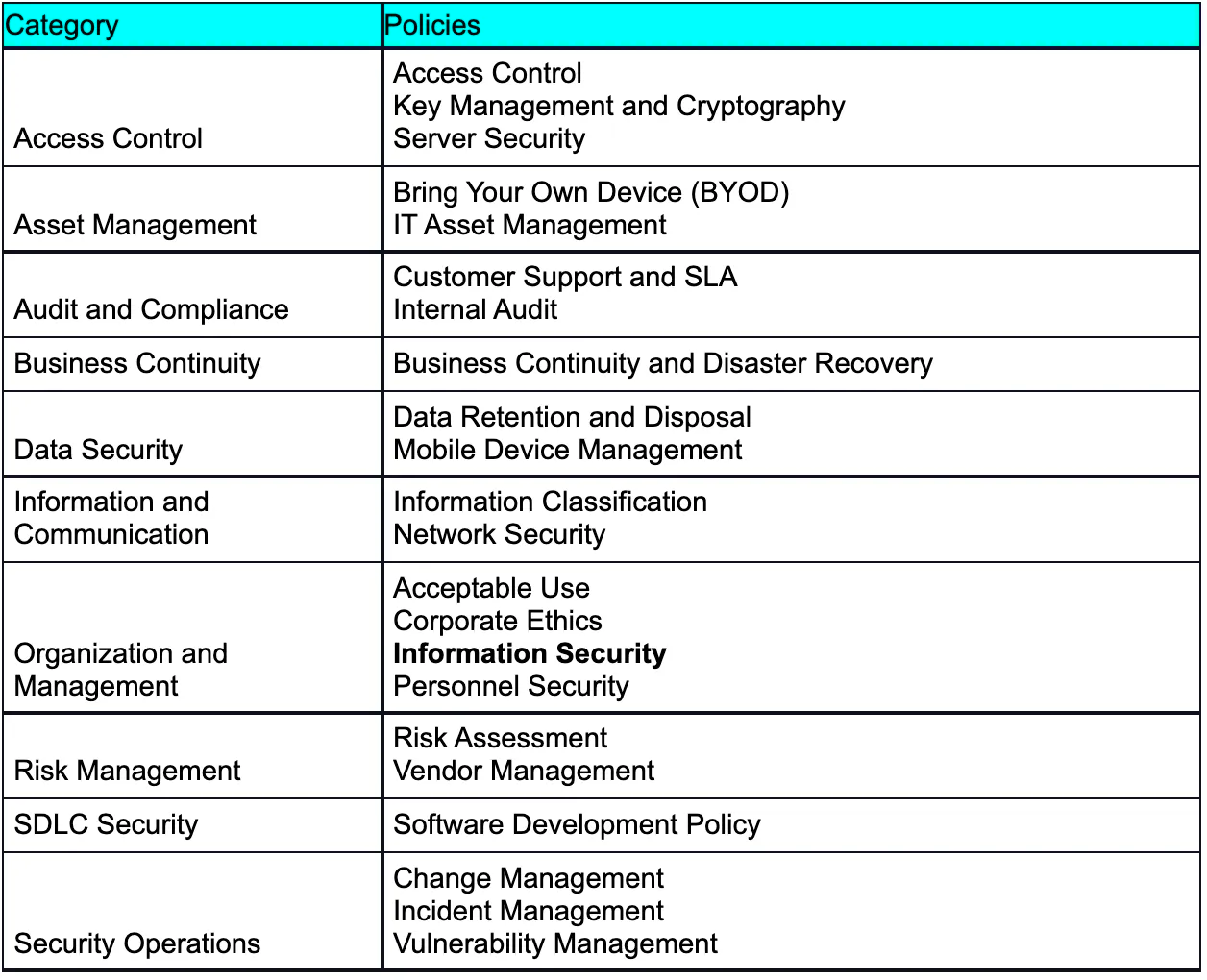
In general Security, Policies can be grouped into the following categories
For each policy, the company will need controls like the example shown below for “Change Management Policy”:
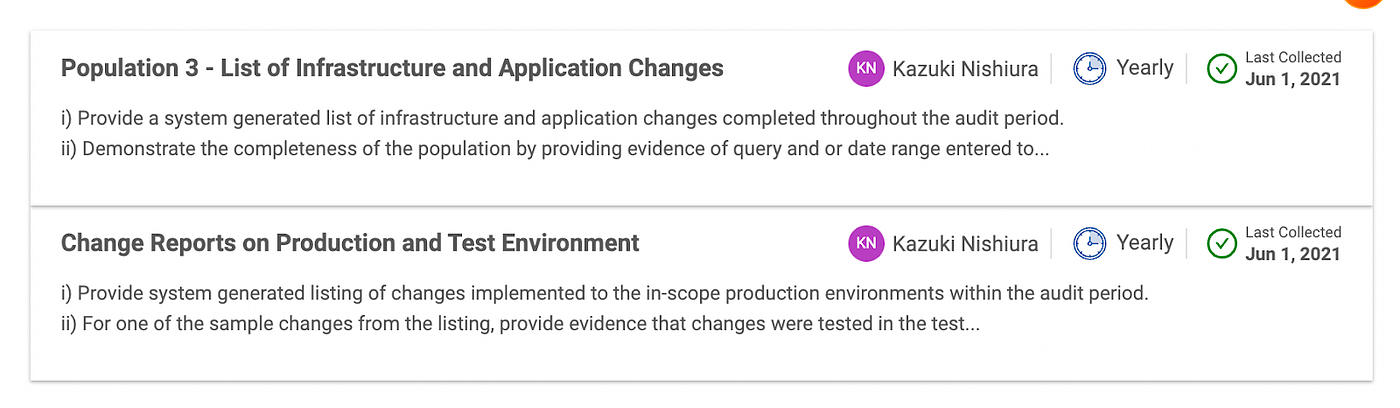
For each control like “Segregation of Environment” in “Change Management” the company can provide evidence like:
SOC 2 vs IS0 27001
The choice for selecting the type of security certification will depend on the client. If a company has international clients, then go with ISO 27001 else for US-based clients, choose SOC 2. A company may choose to go with both, but most customers should be OK with either. ISO 27001 Certification may take more time as it has more items in scope.
SOC2 Type 1 vs SOC2 Type 2
If a company is doing SOC 2 certification, then you have to choose between going with Type 1 first or going directly to Type 2.Type 1 is an audit done at a particular point, like a specific day. Hence there is less evidence requested for it. Type 2 is typically an audit done over 3 to 6 months and hence it is time-bound and a lot more evidence is needed for it. If you are a vendor, most of your customers will ask for Soc 2 Type 2. If you don’t have customers asking ASAP for security compliance like Soc 2 Type 1, then go directly with Type 2. You may also consult with your auditors for deciding this.
Preparation for SOC 2
1. Select Criteria for Audit in SOC 2
When pursuing SOC 2 compliance, you can select the pillars i.e. Trust Service Criteria, that you want to get audited.
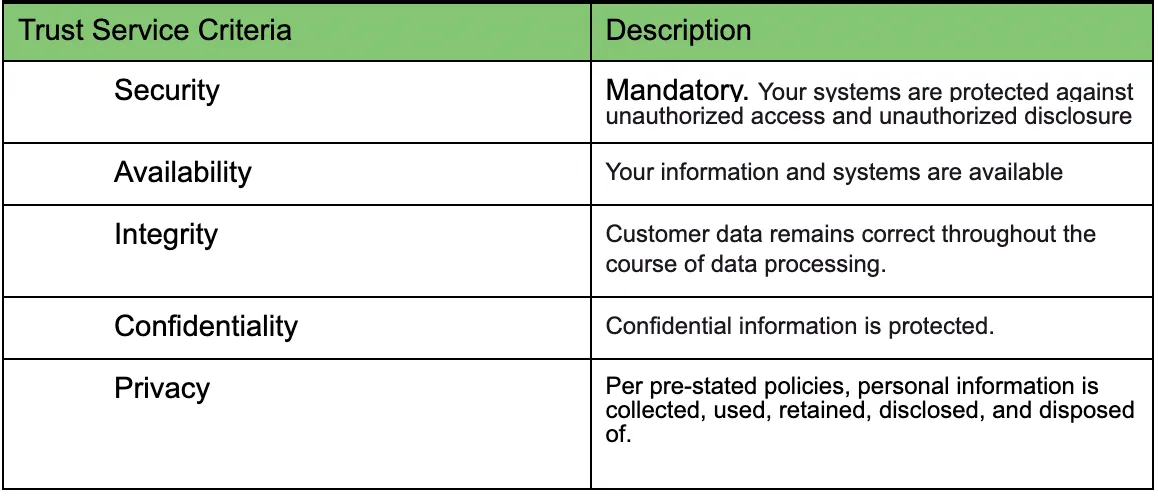
Many startups will select Security, Availability, and Confidentiality. But in specific industries, Privacy and Integrity may also be necessary.2. Select Policy/Audit Management tool
The most popular vendor for automated SOC 2 compliance is Tugobat Logic, Vanta and SecureFrame.
These automated SOC 2 vendors will provide a template of security policies that you are expected to customize for your company. They also offer templates to provide evidence for many of the controls for your policies e.g. Risk Assessment template. Many auditors have their own tools, but they tend to be primitive. The auditors may focus on catching issues instead of focusing on supporting you by providing proper templates for your controls. Hence if you are a startup, then ensure you use vendors like Tugboat or Vaanta.
3. Select auditor
Select Auditors like Align, ssflip, etc or choose an auditor recommended by Tugboat/Vaanta.

Pro Tip: Ask the auditor on which controls or policies that they want you to focus on and any assistance they can provide before you start doing the preparation for the audit.
4. Audit Preparation
Start Preparing in advance of your start of Audit. These will be your biggest step. The auditors expect everything to be ready in advance before the Audit starts. You may also ask auditors for tips like which policies or controls they want your company to focus on. You can start putting evidence for your controls directly in Vanta/Tugboat Logic etc so that it is easy to manage it. For a typical startup, the effort to become SOC 2 compliant may roughly get divided into the below areas.
Pro Tip: For initial audit, check if your auditors will give report for a shorter audit period, so that the report can be done faster. Your all subsequent audits should be for next year.
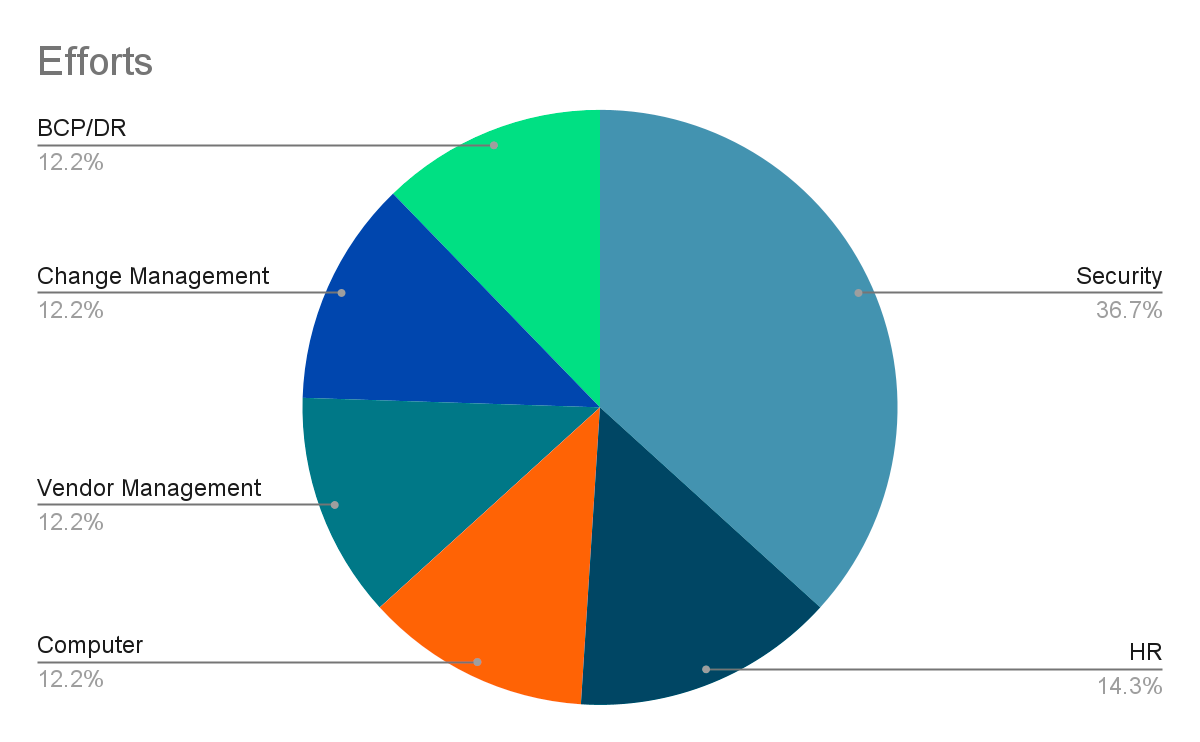
a) Security
- Get someone, preferably external, to do Penetration Testing and audit of your data center. e.g., For the GCP audit and pen testing, we used ThreatWatch. The external penetration report is likely to be requested by your customers.

- Check if you have an IDS system. e.g., monitor network log, SQL queries, etc
- Make sure all data in transit and REST is encrypted.
- Additionally, encrypt data for sensitive items.
- Document Access Request Process in tools like JIRA
- Have an incident management plan
b) HR/IT
- During onboarding, ensure you have an offer letter signed for everyone with job responsibility

- Have a handbook signed for each employee
- Have a performance evaluation plan.
- Have Offboarding plan(remove access, return laptop) documented
- Document steps for onboarding.
- Document all job requirements and have them reviewed/approved by someone else
- Document minutes of your board meetings.
- Have your compliance do a Risk assessment for your entire company. This should cover risk due to SLA, Product, Leadership commitment, Patent etc
c) Computer Security
- Ensure you have an MDM solution like Airwatch that allows you to lock USB access, format machine, etc.

- Make sure each computer has Antivirus. If you are using a Mac or iPad they may allow an exception.
- Ensure that your email, google docs etc have DLP enabled. Having DLP will ensure that your employees are not inadvertently leaking sensitive information.
d) Vendor Management/General
- Do a risk assessment for each third-party vendor and calculate the impact of the vendor being unavailable.

- Ensure that you have a vendor management process e.g., ask your vendors for their SOC 2 reports and financial stability. You can use tools like https://panorays.com/ to collect this information.
e) Change Management
- Get approval before each deployment with systems like Jira.

- Document approval for any system or database access requests.
- Document all incidents and do a Root Cause Analysis to prevent them.
- Document your SDLC like Scrum and be prepared to show a screenshot of your Agile Board
f) Business Continuity/DR plan
- Have a Business Continuity and Disaster Recovery Plan

- Create a document on how you tested your disaster recovery.
- Appoint a manager for BCP who evaluates the main risk for BCP.




