Identity Fraud
Identity Fraud
Verify legitimate users and stop bad actors early
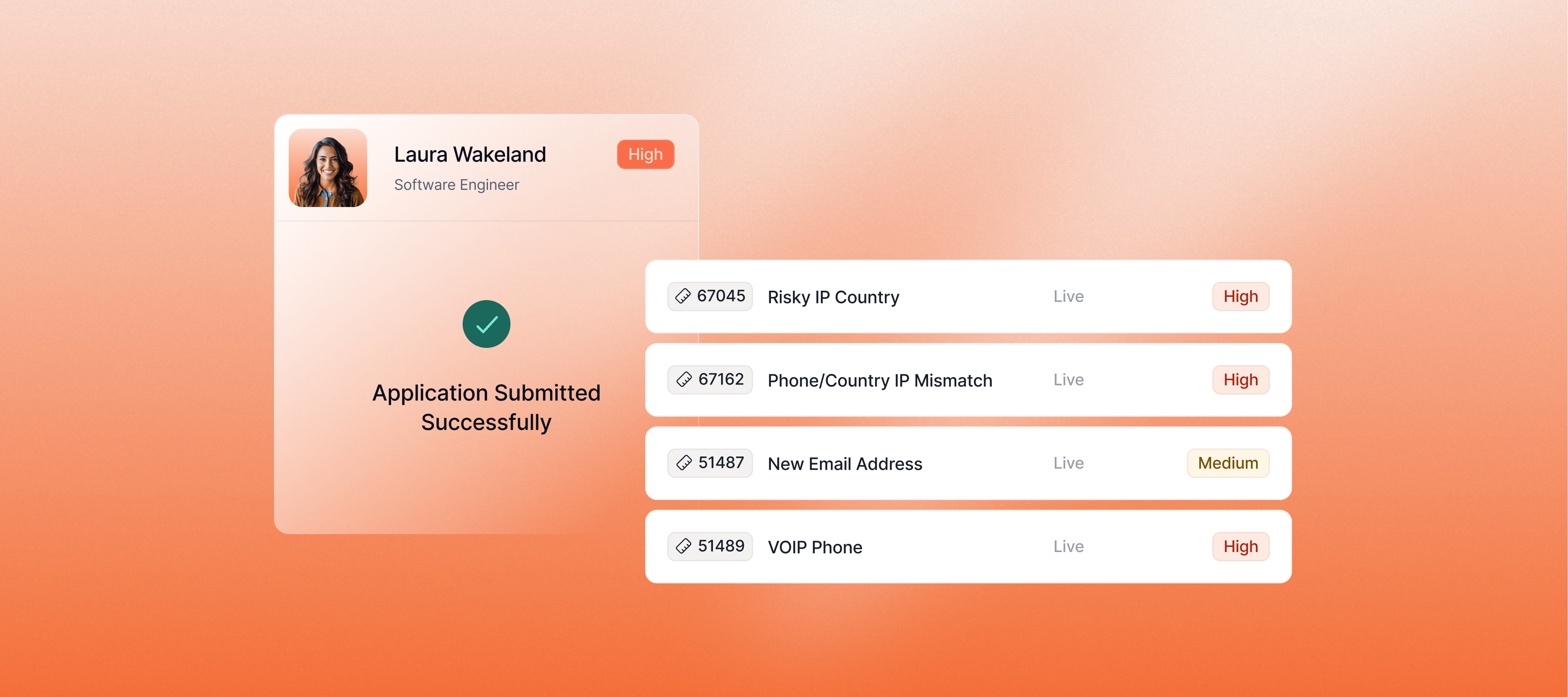
Catch synthetic and stolen identities without adding friction for legitimate users. Use Sardine's device, behavior, identity, and network signals to separate bad actors from good users.

Seamless identity verification wherever you need it
Approve more legitimate users
Reduce onboarding friction with passive risk signals and ML scoring instead of blanket document checks.
Escalate high-risk users
Resolve common identity mismatches automatically and reduce false positives and manual reviews.
Stop coordinated fraud
Detect synthetic and stolen identities, money mule networks, and deepfake impersonation before account creation.
Build trust across onboarding, verification, and ongoing account activity
Account Opening
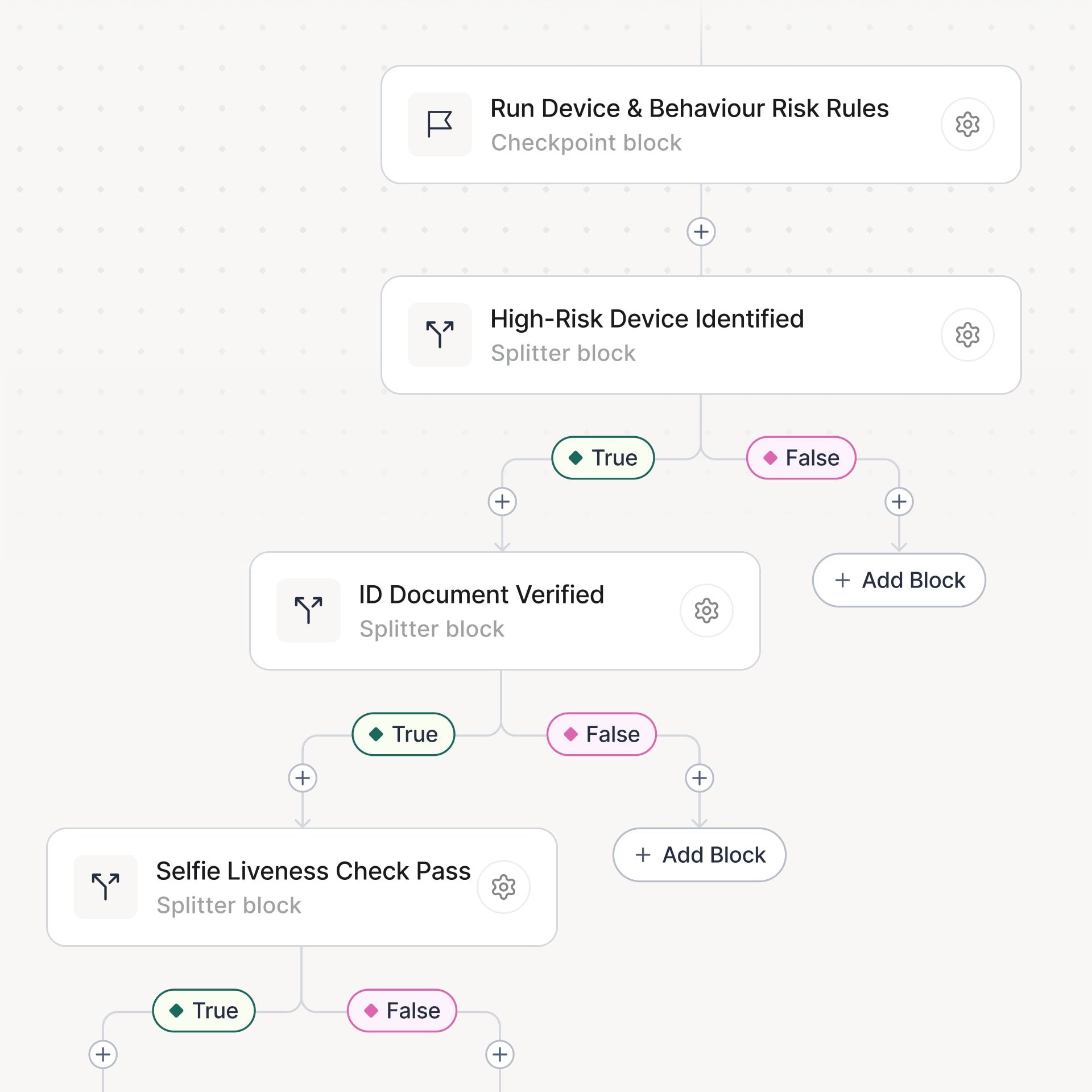
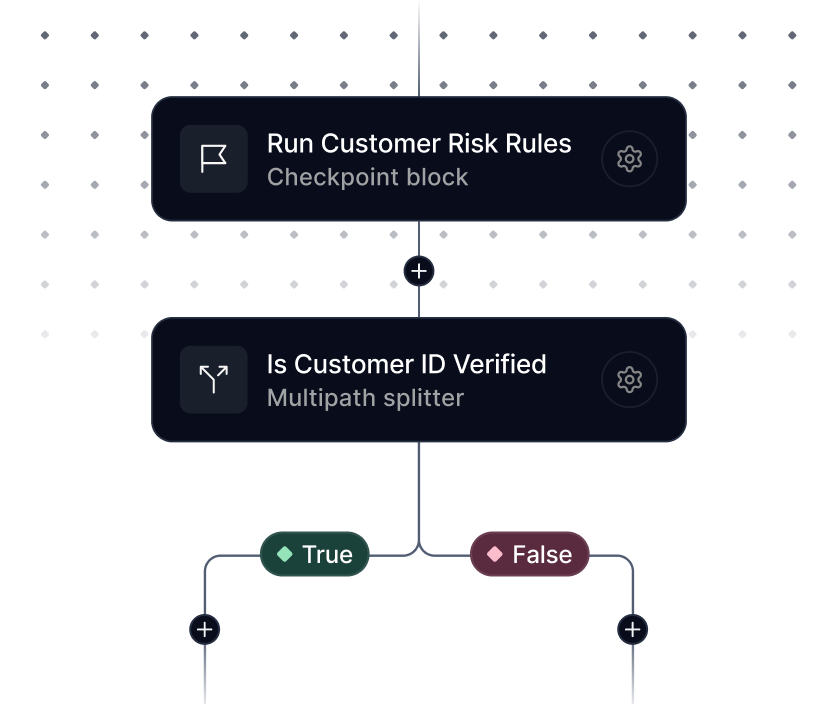
Risk-based onboarding orchestration
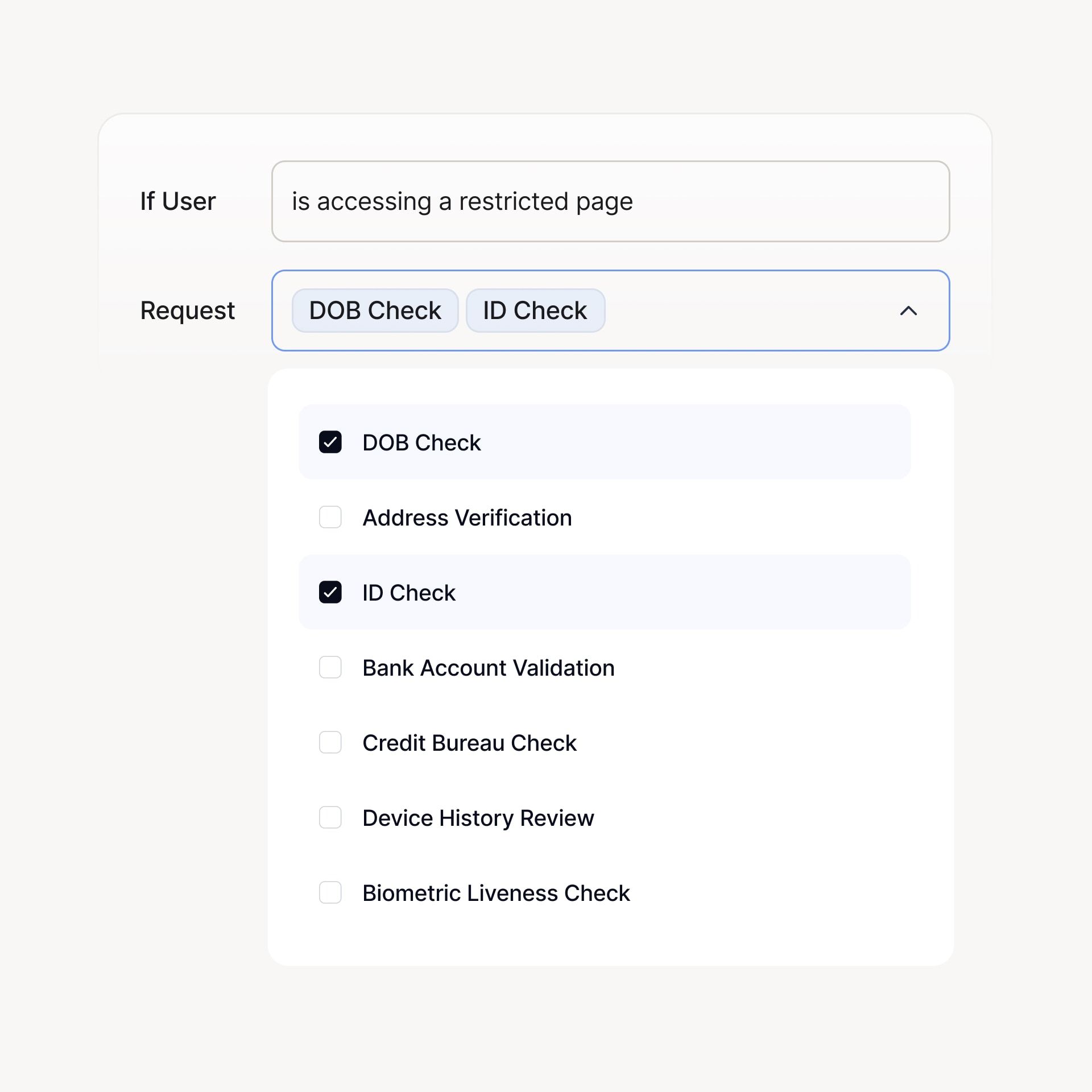
Support custom workflows that route users based on their risk level.
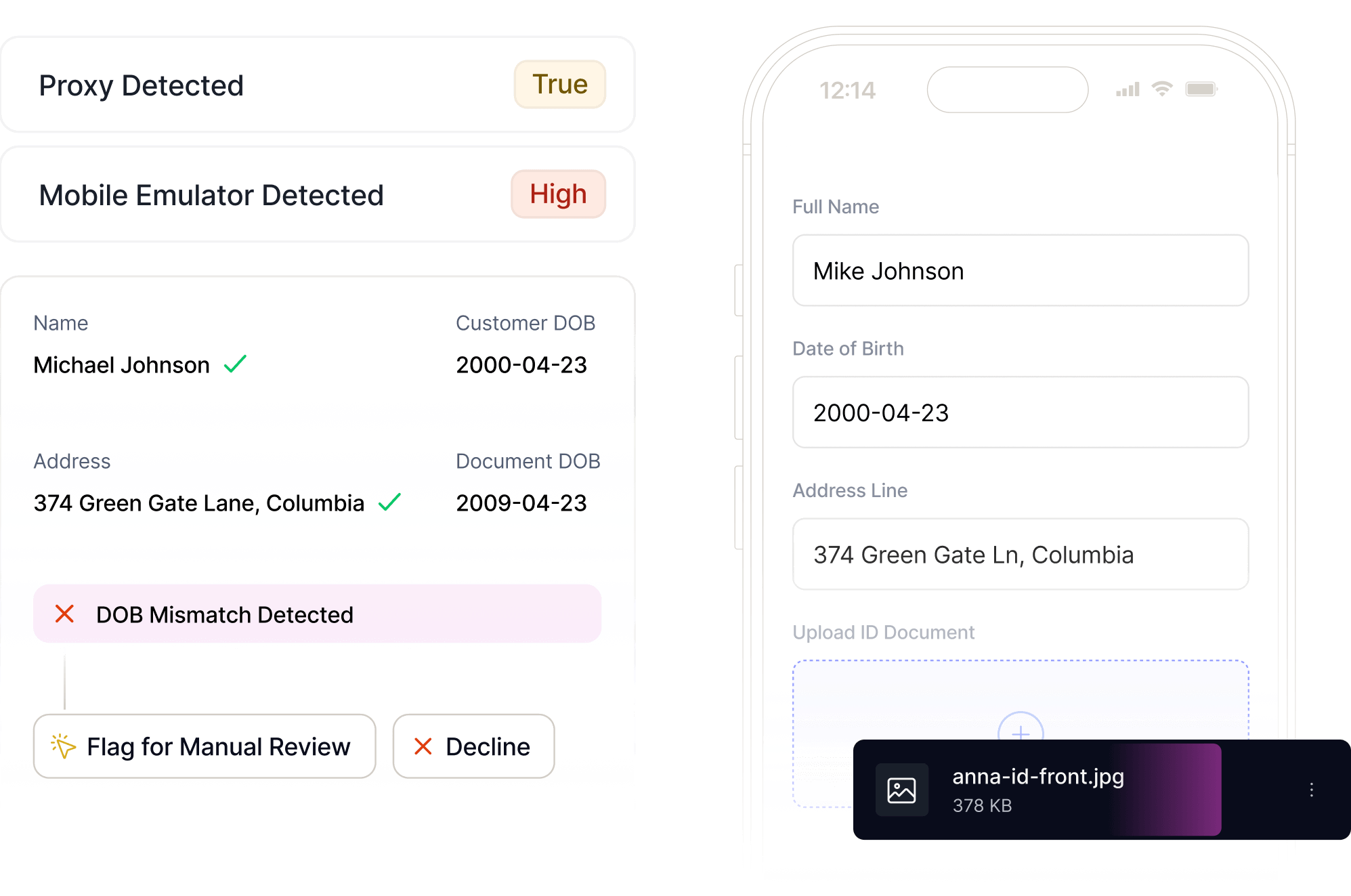
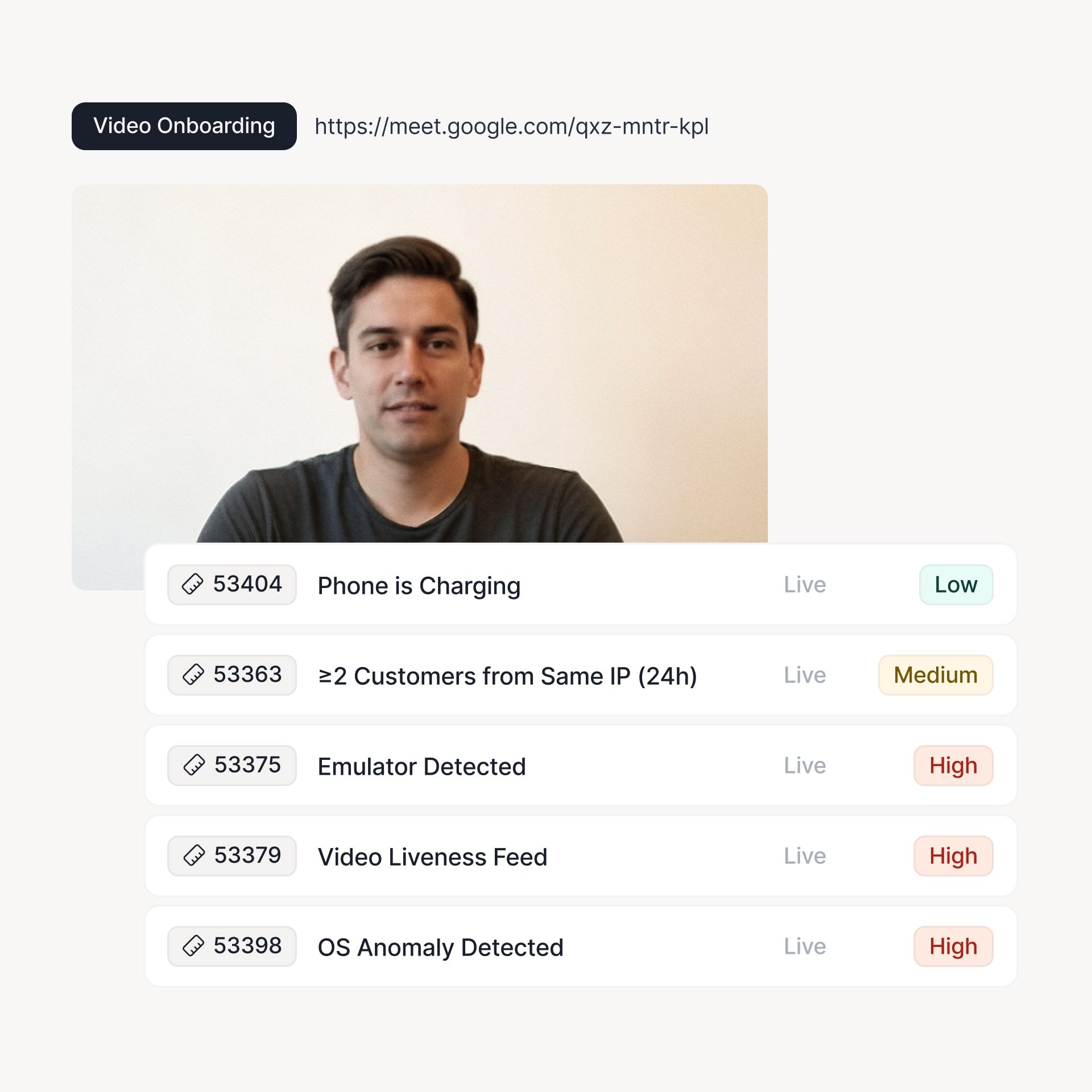
Assess device and behavior signals to identify VPNs, emulators, and remote tools.
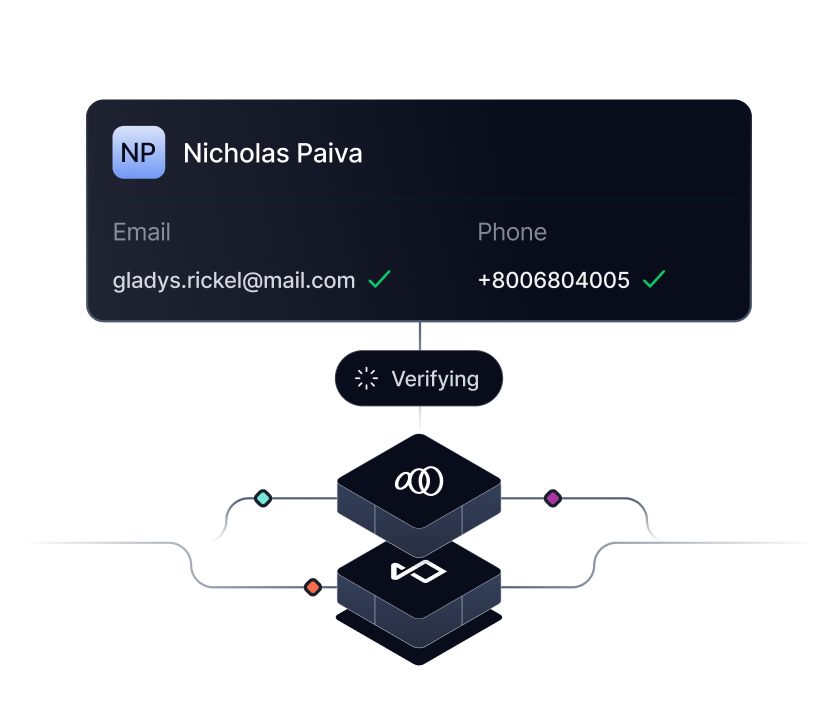
Corroborate name, phone, email, date of birth, and location signals instantly.
Trigger risk-based enhanced due diligence, document verification, or selfie liveness checks.
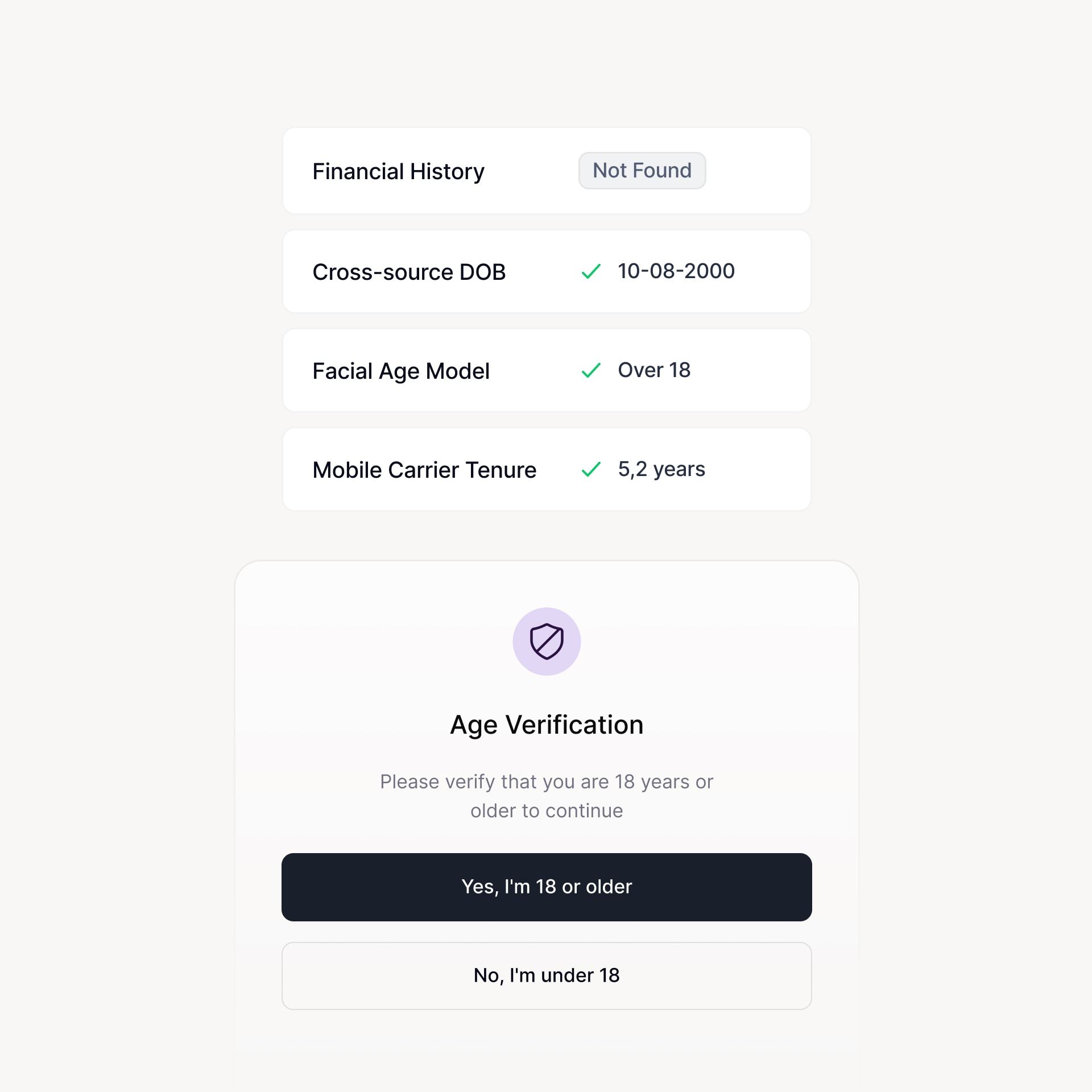
Age Assurance
Make age checks faster and more reliable
Support age-gated access for restricted products while protecting conversion and user experience.
Workforce IDV
Bring more confidence to workforce onboarding
Confirm worker identity to prevent payroll fraud, impersonation, and unauthorized access.
Cross-check phone, email, and device signals to flag inconsistencies and burner accounts.
Identify fake identities, reused attributes, location spoofing, deepfakes, and impersonation attempts.
Reduce manual reviews so teams can focus on real risk without slowing onboarding.
Trust and Safety
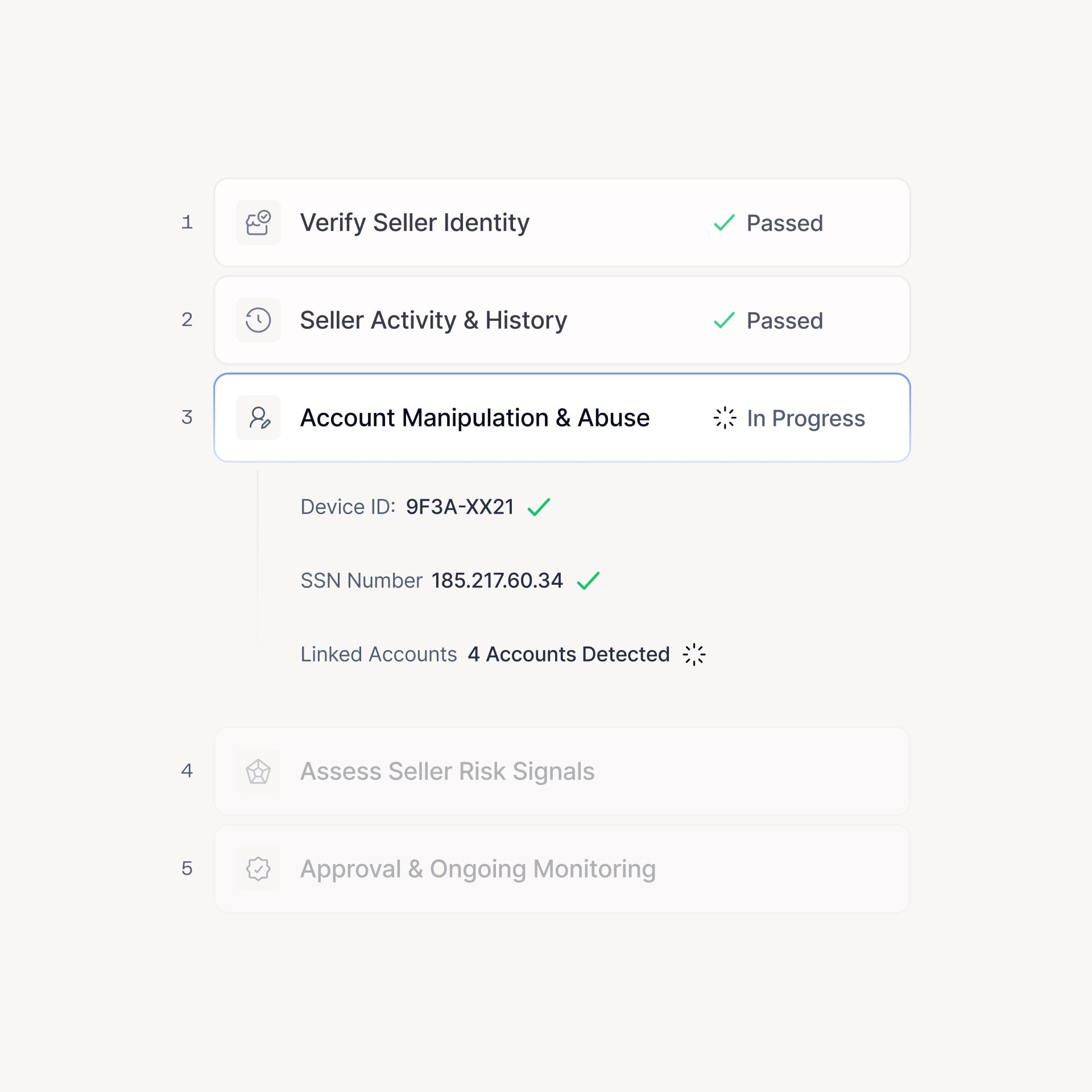
Protect trust across your marketplace or platform
Verify users, sellers, and service providers to reduce fraud, abuse, and fake accounts.
Streamline document review and identity verification
Use AI agents to investigate anomalies, clear false positives, perform online searches, and verify users faster.
Backed by the industry’s leading agentic risk platform
Device & Behavior
Add more context to identity verification
Device and behavioral intelligence establishes whether a real person is present, if the environment is trustworthy, and if identity claims are consistent across sessions.

Data Consortium
Add historical identity context
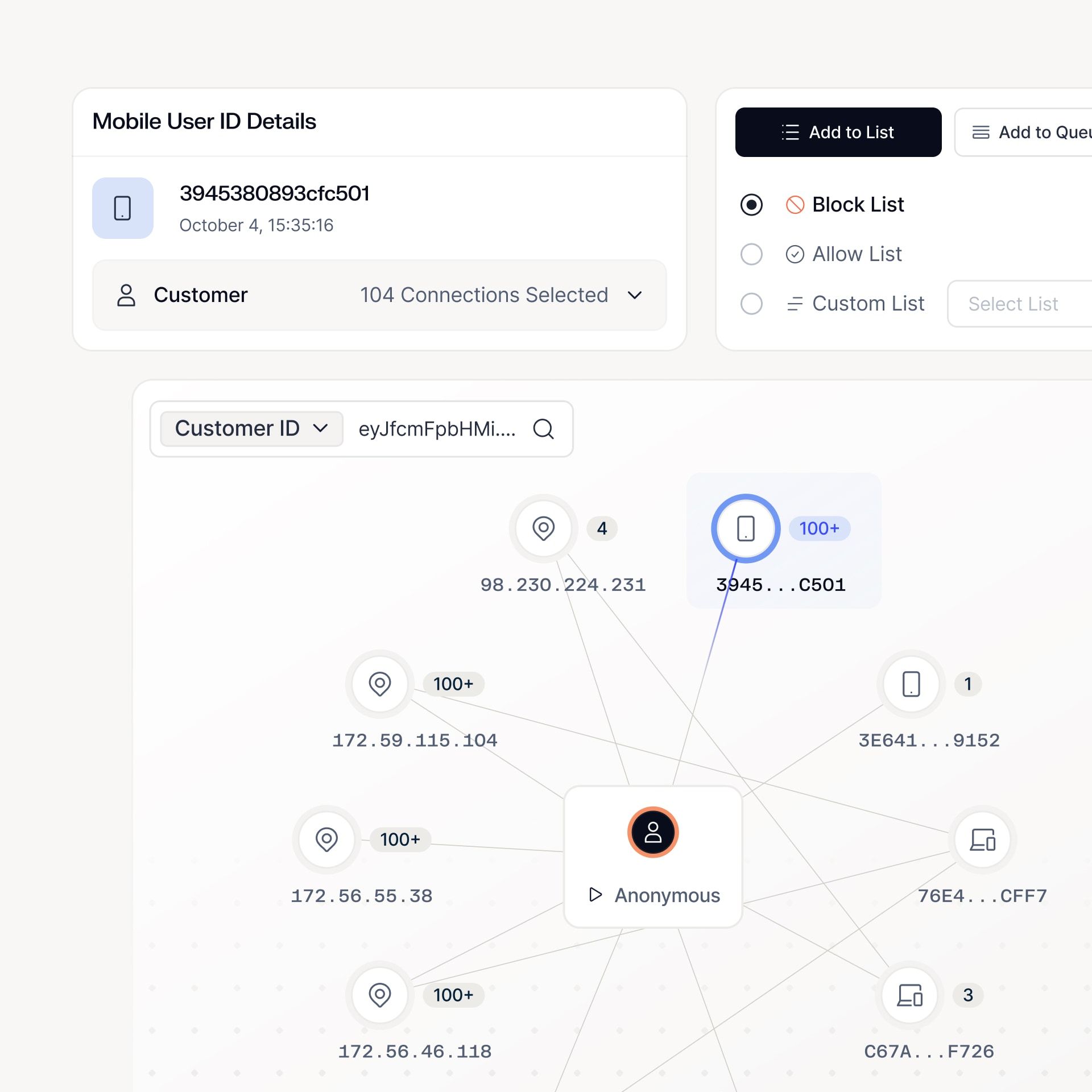
Network-level data links devices, identities, and behavioral patterns across institutions to surface repeat abuse, coordinated fraud, and emerging threats your team cannot see in isolation.
Rules & Workflows
Auditable no-code rules and workflows
Design progressive verification paths, set escalation thresholds, and route reviews without hardcoding logic, while maintaining consistent decisions, clear audit trails, and control.
Machine Learning
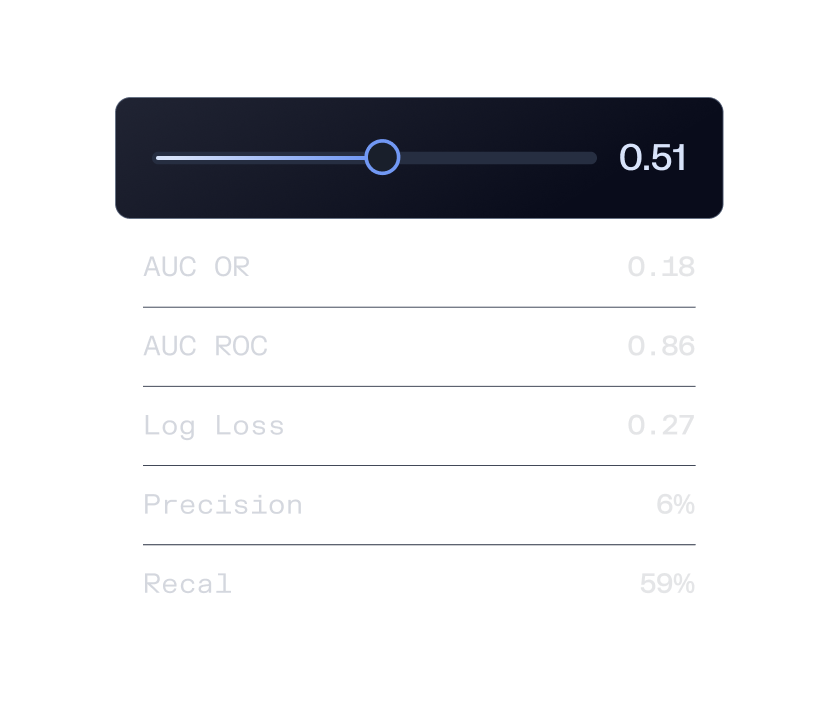
Let our models do the rest
Use our ML models to spot identity fraud more accurately and reduce noise from false positives. With full explainability, you know exactly what factored into a risk decision.
Spot identity fraud without blocking good users
Frequently
asked questions

How is Sardine different from traditional identity verification vendors?
Traditional identity verification providers rely heavily on static document checks and basic bureau matches. Sardine layers identity resolution with device intelligence, behavioral biometrics, and consortium-level context to detect sophisticated fraud before documents are even collected.
Sardine’s AI agents also resolve common onboarding issues automatically, such as OCR errors, name transliterations, and formatting mismatches, so more legitimate users are approved faster with fewer manual reviews.
Can Sardine reduce manual reviews and false positives in onboarding workflows?
Yes. Sardine is designed to clear routine identity mismatches and obvious false positives automatically, preventing review backlogs and reducing analyst workload.
AI agents continuously review queues, corroborate identity claims against authoritative sources, and escalate only high-confidence risk cases. Customers using Sardine have automated nearly 90% of fraud and compliance checks in real time.
How does Sardine detect synthetic identities and coordinated fraud networks?
Sardine combines identity consistency checks with persistent device fingerprinting, behavioral signals, velocity attributes, and network-level consortium intelligence.
In addition, Sardine’s Graph Analyst agent maps customer and merchant networks to uncover hidden relationships, suspicious clusters, and coordinated abuse patterns that point solutions miss.
Does Sardine support automated investigations beyond onboarding?
Yes. Sardine’s identity platform extends beyond onboarding into continuous monitoring and investigation workflows.
The OSINT Agent automatically gathers public risk context from news, social media, registries, and open-source databases, reducing manual research time by up to 90% and producing clear risk summaries for analysts.
How does Sardine help teams stay audit-ready and regulator-ready?
Sardine’s AI agents don’t just generate alerts, they produce consistent, defensible evaluations with built-in documentation.
Agents can automatically generate case summaries, investigation findings, and even regulator-ready SAR/UAR narratives in minutes instead of hours. Sardine also supports an Agentic Oversight Framework, where agent decisions can be sampled and calibrated with human governance.
How does Sardine help with disputes and chargebacks tied to identity fraud?
Sardine’s Disputes Agent automatically gathers transaction context, customer history, device intelligence, and delivery proof, then assembles dispute-ready evidence packages tailored to card-network reason codes. This helps teams resolve disputes faster and win more chargebacks with consistent documentation.