Detecting Apple Pay Fraud and Chargebacks
When you walk into a store or checkout online and pay with your iPhone or Apple Watch, you may use an Apple Pay service. This more convenient way to pay is preferred by younger consumers but many merchants in retail and e-commerce see increased fraud coming from Apple Pay.
Merchants are stuck between a rock and a hard place. To get purchase volume and attract the key younger demographic they must support Apple Pay, but it may increase fraud losses and create higher chargeback rates.
To get the best out of Apple Pay we need to break down.
- Apple Pay adoption and statistics
- Apple Pay economics
- The anatomy of a transaction
- Emerging fraud patterns.
1. Apple Pay Adoption in the West
Apple Pay popularized a new “Card Present” mechanism as an alternative to the card swipe called NFC (or “tap to pay”) in the US. For the first time, consumers could leave their cards and home and pay with their phone, watch, or checkout online without having to enter long card numbers and expiry dates. This convenience has exploded in popularity since its launch in 2014. Now one in every 5 US consumers uses Apple Pay every month.
Apple Pay users skew younger, with 73% of Gen-Z users preferring to use Apple Pay for e-commerce and in-store. To attract this key demographic merchants are increasingly pushed to upgrade their payment acceptance offering.

NFC (tap to pay) support forced many retailers to upgrade their terminals to support NFC in the United States. In Europe, NFC-like chip/pin was used with credit cards for a long time, so adopting Apple Pay in the EU was easier. Additionally, the prevalence of “contactless cards” (or tap to pay) meant Apple Pay wasn’t the step change for European consumers in quite the same way.
NFC is convenient for consumers, but unlike chip/pin is not as secure because the user is not entering a second factor of authentication. To counter this there are usually amount limits ($250 in the US) and higher declines in NFC flow compared to chip/pin.
2. Apple Pay Economics
When someone uses a card, the merchant may pay a “discount fee” of around 2% for that transaction in the US. The fees are lower in the EU due to regulations, so the service and loyalty points programs tend to be relatively bad in the EU.
The bulk of these fees in the US, say 1.7%, will go to the issuer, and the issuer may pay Apple around 0.15%
Hence Apple gets its cut from issuers which means merchants often lose out. Hence most retailers had disabled NFC and/or Apple Pay in their terminals during the early days. However, facing the rise in demand from consumers, especially in the younger demographic many are now enabling this payment type.
With compressed margins, higher risk of fraud and increasing consumer demand its more crucial than ever to understand Apple Pay to prevent fraud from eroding margins and consumer trust.
3. The Anatomy of an Apple Pay Transaction
Apple Pay uses a variety of security features at various points of the customer lifecycle to protect user data, including:
- Account Creation (Tokenization): When you add a credit or debit card to Apple Pay, the card number is encrypted and stored on your device in a secure chip called the Secure Element, and this tokenized number is called DAN. When you make a payment, Apple Pay generates a unique token that is used to process the transaction. This token cannot be used to track your spending or to make unauthorized purchases.
- At payment (Biometric authentication): You can use Touch ID or Face ID to authenticate payments made with Apple Pay. This helps to ensure that only you can make payments with your device.
- At rest (Encryption): All communication between your device and Apple Pay servers is encrypted. Any secure data like tokens or biometric markers never leave your device. This helps to protect your data from unauthorized access.
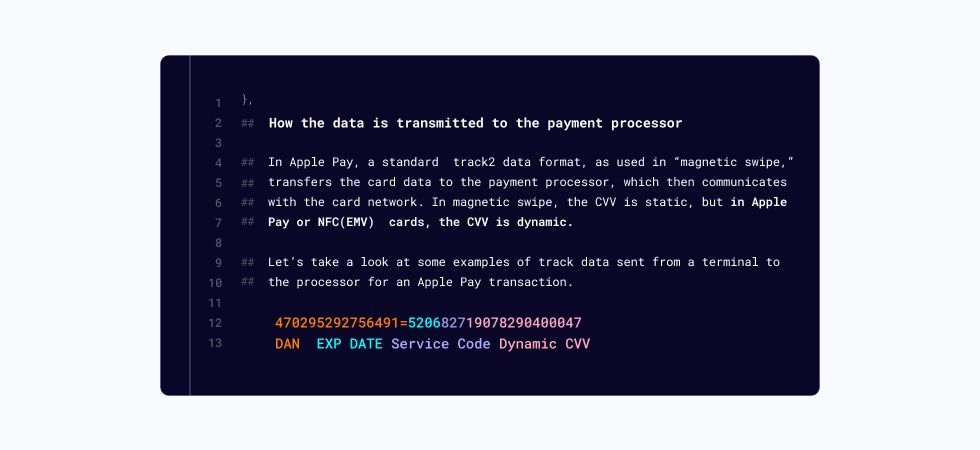
The CVV (3 or 4 digit security number) is also protected securely. Apple Pay generates a new CVV for every transaction, This transaction-specific dynamic security code (CVV) is more secure than magnetic swipes which helps avoid malware hacks.
3.1 Anatomy of a transaction: Apple Pay Dan Creation
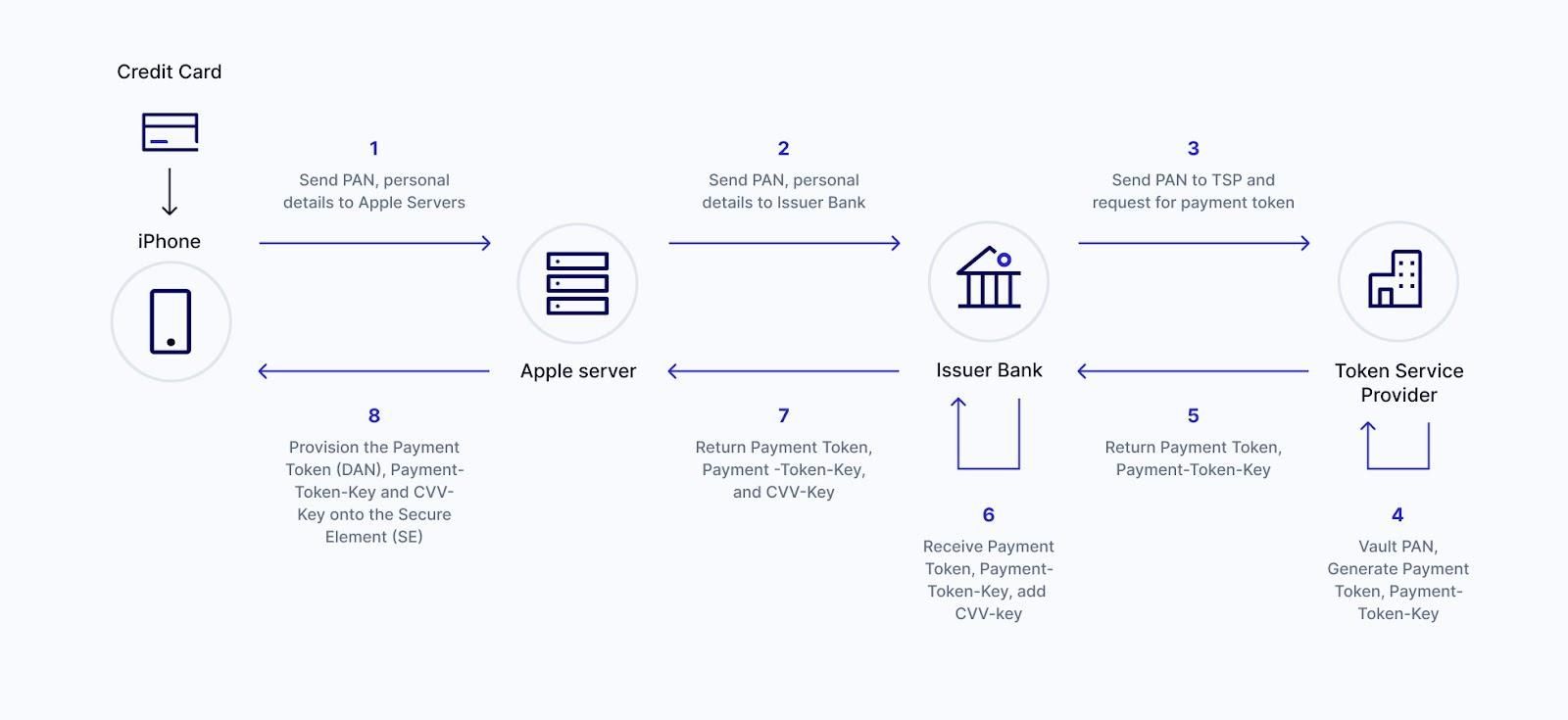
When you add a credit or debit card to Apple Pay, the Apple Pay System uses a Token Service Provider (TSP) to generate a payment token based on your credit or debit card called Device Account Number (DAN).
The DAN is used to represent your card in Apple Pay transactions.
The DAN is not your card number and cannot be used to make unauthorized purchases. The same card added to another iPhone will generate a “different” DAN and hence the name “device” account number.
The DAN is created using a process called tokenization. Tokenization is a security technique that replaces sensitive data with a unique identifier that cannot be used to recreate the original data. In the case of Apple Pay, the DAN is created by encrypting your card number with a unique key. This key is stored on your device in the Secure Element and cannot be accessed by anyone else.
4 Apple Pay Fraud Patterns
4.1 Non-Specific to Apple Pay
While Apple Pay is generally considered to be a secure payment method, there are some risks associated with using it for online transactions.
These risks include
- Fraudulent websites: There are several fraudulent websites that claim to accept Apple Pay. These websites may look legitimate, but they are designed to steal your personal information.
- Data breaches: If a merchant's website is hacked, your Apple Pay data could be compromised. This could allow criminals to make unauthorized purchases using your account.
- Malware: If you download a malicious app, it could potentially steal your Apple Pay data.
4.2 Apple Pay Specific Risk
Apple made the landscape more complex by bringing another actor into the payment ecosystem.
Now, when a merchant tries to debug what went wrong in a transaction (e.g. higher declines or to ensure that the billing address in Apple is valid), they may have to debug with Visa, Apple, and the card Issuer.
In most cases, they will point out that it's the issuer's responsibility.
For some issuers, it is a new system; hence, they usually have multiple loopholes for Apple Pay.
Some of the loopholes:
- Limited protection on carding attacks to add a card to Apple Pay.
- Limited validation on the billing address in Apple Pay.
We will now discuss some of the Apple Pay issues.
Accepting payments is where the fraud liability is the biggest issue for Apple Pay. The merchants have fraud liability and don't have the underlying card numbers. Issuers do have the card number but don't carry liability for fraud losses, so they're not motivated to stop the fraud. For them, a transaction is the merchant takes revenue, and a fraud loss hit.
4.2.1 Apple Pay DAN to Issuer Mapping
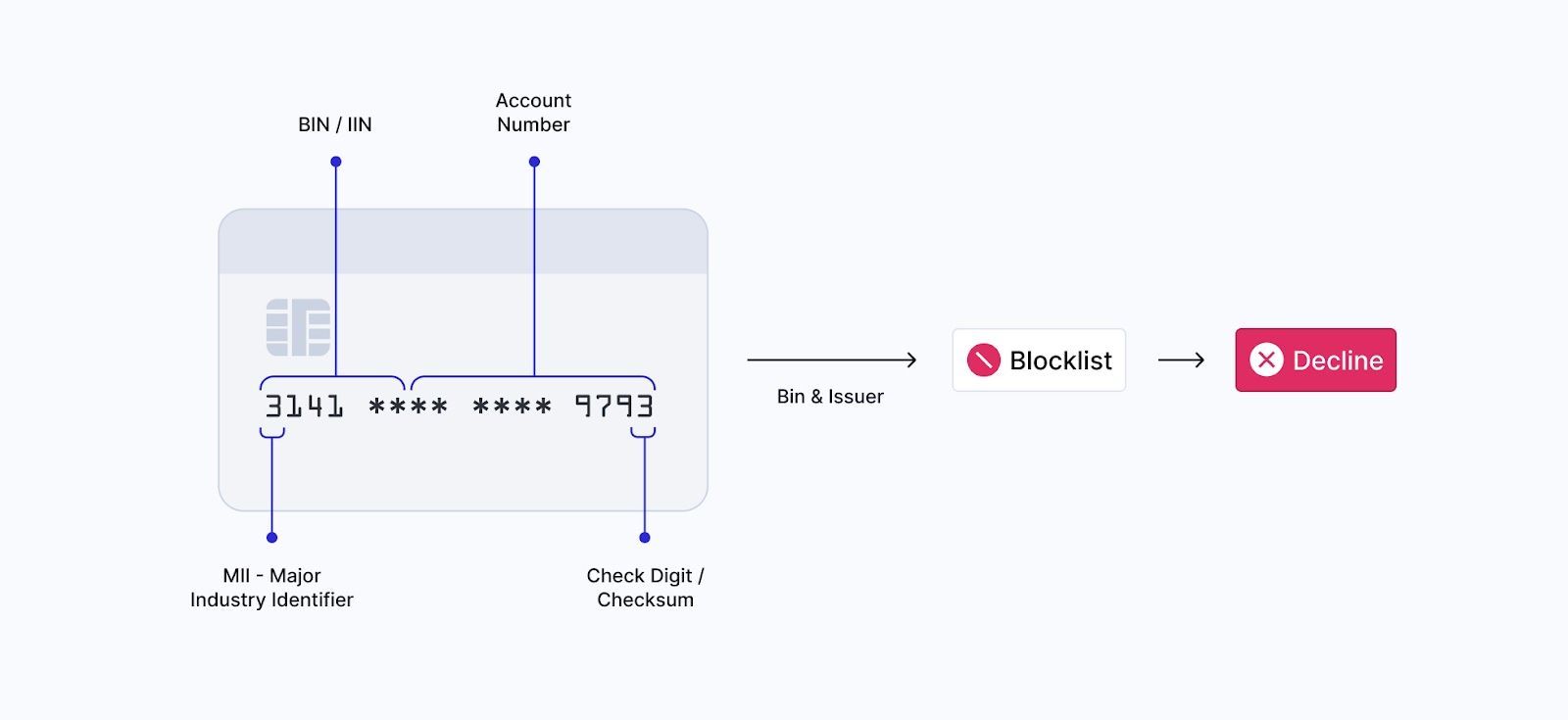
One classic way to detect fraud was “BIN mapping.” Matching a card issuer to the card number using the first 6 digits on the card (The Bank Identification Number or “BIN”).
Apple Pay changed the effectiveness of bin mapping, as many internal and external bin database vendors did not support the Apple Pay DAN. Apple Pay BINs differed, so the features like “risky issuer” or “is a NeoBank” would not work.
Those features are missing if an issuer is compromised or the merchant wants to know if this card belongs to a risky neo-bank or card issuer with poor fraud controls.
Fraud Squad tip: To solve this, you need a fraud vendor supporting bin-to-issuer mapping for Apple Pay. (Who might that be 🐟👀). In time we're hopeful Apple will solve this with a merchant friendly solution.
4.2.2 Multiple DAN/TOKENS for the same Card
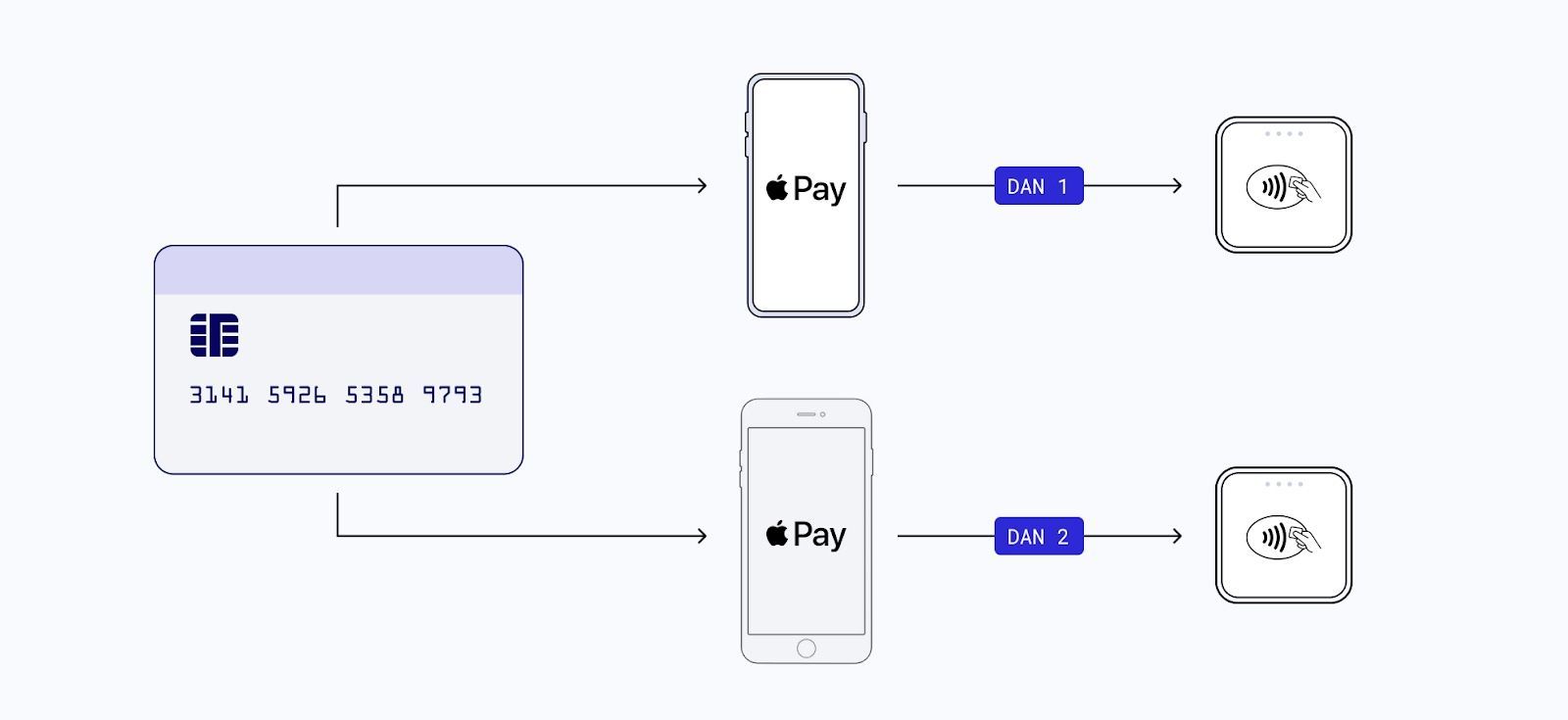
Another classic tool to detect fraud was “velocity checks.” If you saw the same card being used multiple times (10x, 20x, or 100x at the same merchant) for purchases this pattern might indicate fraud.
With Apple Pay, if a fraudster adds the same card to multiple iPhone devices they get a separate DAN.
Fraud Squad tip: Merchants check with your PSP or fraud vendor for aggregations around the internal card number, i.e., permanent account number reference number - corresponding to the DAN.
This can significantly reduce fraud attacks.
Conclusion
Apple Pay is a secure payment method, but knowing the risks associated with using it for online transactions is important.
Apple is famous for privacy (fingerprint, tokenization), but this removes some of the data merchants used to fight against fraud, in both Apple Pay and Safari Mobile Browsers. By following the tips above, you can help to protect your personal information and finances.
We’re always keen to hear about what threats you’re seeing and to help where we can. Contact us if you have a particular challenge and want to run it by our fraud squad.