Did you know that 26% of companies report being targeted by account takeover attempts every single week? Account breaches are widespread among businesses, affecting nearly 80% of Fortune 1000 organizations. Stolen credentials inflict significant damage, with the average cost of a breach reaching $4.62 million, according to Abnormal Security. What’s more, this crime is on the uptick, with global costs due to account takeover fraud projected to balloon to $16.8 billion by 2025.
Fortune 1000 Companies | Average Cost of ATO Breach | Global Cost of ATOs |
Nearly 80% Impacted | $4.62 million | $16.8bn by 2025 |
Remember the Robinhood security breach in 2021? Social engineering tactics allowed attackers to access millions of customer email addresses, dates of birth, and personal details. Then the fraudsters demanded an extortion payment. This incident demonstrates the potential damage of a successful ATO attack.
While cybercriminals are constantly developing new tactics for account takeovers (ATOs), businesses don't have to be passive targets. By implementing proactive security solutions and educating users about ATO risks, businesses can effectively tackle these attacks and safeguard their valuable data.
Here’s the fundamental issue: detection is often siloed between cybersecurity and fraud teams when in reality the ATO threat spans the entire enterprise. Solving this requires a holistic approach to data collection.
Tackling Account Takeovers TL:DR
- Account takeovers are a major threat, affecting nearly 80% of Fortune 1000 companies at an average cost of $4.62 million per breach.
- Phishing emails, credential stuffing, and social engineering are common methods used by attackers to steal login credentials.
- Unusual login activity, account changes, and anomalous user behavior can all indicate an ATO attempt.
- Businesses can prevent ATOs by implementing data breach monitoring, multi-factor authentication, user education, endpoint security, and suspicious activity monitoring.
- After an ATO, attackers may engage in unauthorized purchases, transfers, and attempt to cover their tracks.
- The impact of ATOs varies across industries, but can include fake listings, payment hijacking, loyalty point theft, unauthorized financial activity, and crypto wallet draining.
- A comprehensive security strategy to combat ATOs involves additional authentication measures, threat intelligence, user behavior analysis, third-party data integration, SIM swap monitoring, and proactive data breach checks.
What are Account Takeovers (ATOs) in a Business Context?
An account takeover (ATO) is a cybercrime where a malicious actor gains unauthorized access to a business's online account credentials. These targeted attacks can compromise any online account, but financial platforms, e-commerce portals, marketplaces, cryptocurrency, iGaming, and systems with access to sensitive data are especially attractive targets for attackers. Once a compromise occurs, attackers can steal critical business information, initiate fraudulent transactions that drain financial resources, and damage your brand reputation through unauthorized actions. Understanding the risks and implementing robust security measures are essential to safeguarding your business from the growing threat of ATOs.
Common Account Takeover Methods
Here are the three most common methods ATO attackers employ:
- Phishing: Deceptive emails or text messages disguised as legitimate communications trick employees into clicking malicious links or entering login credentials on fake websites.
- Credential Stuffing: Bots that leverage stolen usernames and passwords from previous data breaches are used to attempt unauthorized access to business accounts across various platforms.
- Social Engineering: Sophisticated scams manipulate employees into revealing login details. Attackers may impersonate customer service representatives, IT support personnel, or even trusted colleagues.
Detecting ATO Red Flags
Be proactive in safeguarding your business by staying vigilant for the red flags that might indicate an account takeover (ATO) within your organization. By recognizing these signs and taking swift action, you can effectively prevent or minimize damage caused by ATO attempts.
Unusual Login Activity:
- Identify unrecognized login attempts originating from unexpected locations (e.g., different country) or occurring at odd times (e.g., 3 AM), potentially signaling unauthorized access.
- Implement custom honeypots (invisible fields) to trap automated scripts and bots used for ATO attempts.
- Use direct bot detection tools to identify logins originating from automated programs like Selenium or emulators like BlueStacks.
- Leverage network-based detection to monitor for suspicious login attempts originating from known proxies, VPNs, or IPs with a poor reputation.
Account Compromise Indicators:
- Monitor for unauthorized changes to account details, such as passwords, email addresses, or security settings associated with critical business accounts.
- Be wary of disabled security features like two-factor authentication (2FA), as attackers might try to remove these safeguards to prevent detection and recovery efforts.
Advanced Detection Techniques:
- Employ device-based detection to analyze browser versions, operating systems, and device fingerprints. This can help identify suspicious logins from rooted devices, tampered apps, or mobile emulators.
- Monitor for anomalous usage patterns such as unusual mouse movements, unexpected phone sensor activity (e.g., constant gyroscope movement), or rapid copy-pasting of login credentials, which can be indicative of automated scripts.
- Scrutinize login attempts with risky referrers (websites known for distributing malware or stolen credentials).
Multi-factor Authentication Breaches:
- Be alert to situations where multiple users are logging in from the same device or IP address, which could suggest stolen login credentials being used across accounts.
Changes in User Behavior:
- Monitor for sudden changes in user behavior, such as a significant increase or decrease in activity levels, or purchases from unusual locations.
New Device Attributes:
- Identify logins with new device attributes like unrecognized ISPs, operating systems, or timestamps suggesting impossible travel times (e.g., logging in from two different continents within minutes).
Device Obfuscation and Muling Activities:
- Be wary of login attempts associated with device obfuscation techniques, remote access software, or mule behaviors like creating distractions during logins, quick handoffs of accounts, suspicious money transfers, or goods consistently shipped to the same location.
By promptly addressing these warning signs and implementing these detection methods, businesses can significantly improve their ability to identify and prevent ATO attacks.
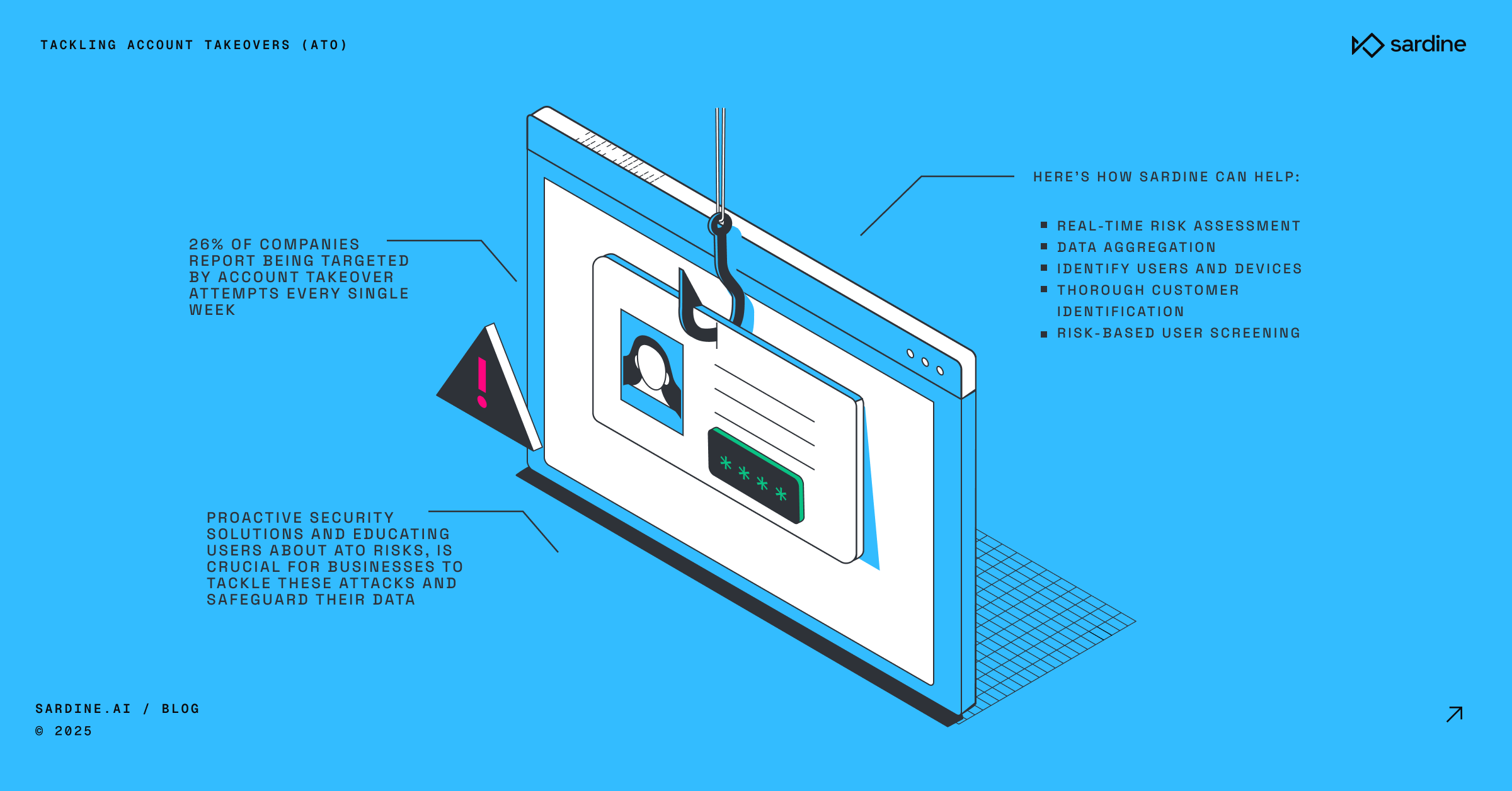
Stopping ATOs At Every Stage
Like a thief casing a joint, ATO perpetrators follow a distinct path, meticulously gathering information, exploiting weaknesses, and ultimately breaching their target's defenses. Understanding how attackers breach accounts empowers you to implement effective safeguards. Here's a breakdown of the typical Account Takeover (ATO) stages, along with actionable tips to stop them at each stage:
1. Information Gathering: Attackers first gather intel on their target. They might use social engineering tactics, tricking the victim into revealing personal details (emails, phone numbers) by posing as a trusted source like a company or friend. Alternatively, they exploit leaks from data breaches to steal credentials for later ATO attempts on other platforms.
How to Stop Them:
- Use data breach monitoring services: Tools like Have I Been Pwned, LifeLock, or IdentityForce can proactively alert users if their credentials appear in leaks. Encourage users to update passwords immediately.
- Monitor for risky referral URLs: These could lead to phishing sites designed to steal login information. Invest in device intelligence solutions that can detect and block such attempts.
- Be vigilant in chat environments (marketplaces, e-commerce): Look for signs of social engineering, like suspicious activity in user chats.
2. Credential Theft: Armed with some personal info, attackers launch the next phase: stealing login credentials. This often involves phishing scams. Deceptive emails or texts, disguised as legitimate messages, lure the victim into clicking malicious links leading to fake websites designed to steal login credentials. Malware can also infiltrate a victim's computer, capturing keystrokes or screenshots as they type in real login information.
How to Stop Them:
- Vigilance against Deceptive Links: Continuously monitor for suspicious URLs, especially those originating from unknown or untrusted sources.
- Heightened Authentication Awareness: Stay alert to unusual login attempts originating from unfamiliar or suspicious sources. Keep an eye out for logins from rooted devices, tampered applications, or instances where remote access tools are active during a session. Additionally, be cautious if there's an ongoing call during a login session, as these could be indicative of malware or compromised accounts. Enforcing multi-factor authentication (MFA) can provide an extra layer of security, making it significantly harder for attackers to gain unauthorized access even if they possess stolen credentials.
- Implement Robust Endpoint Security Measures: Deploy advanced endpoint protection solutions equipped with features such as real-time threat detection, behavioral analysis, and sandboxing capabilities. These technologies can help identify and thwart malicious activities, including attempts to capture keystrokes or screenshots for credential theft purposes. Additionally, keep all software and security patches up to date to address known vulnerabilities and minimize the risk of exploitation by malware or other malicious entities.
3. Account Access: With stolen credentials in hand, attackers attempt to infiltrate the target's account. This might involve simply logging in or changing login details to block the victim's access. They may even add their own contact information to solidify control.
How to Stop Them:
- Monitor for Unauthorized Access: Be on high alert for login attempts from unrecognized devices or IP addresses and locations that deviate from the user's usual pattern.
- Identify Suspicious Behavior: Look for red flags in user activity, such as:some textManually entering personal information instead of autofill (suggests potential malware).Excessive tab switching (may indicate attempts to bypass security measures).Rapid changes to account settings, especially linking new payment methods (potential attempt to gain control).
- Implement Layered Security: Don't rely solely on monitoring. Here's how to add extra layers of protection:some textAccount Flagging: Mark suspicious accounts for closer monitoring and potential intervention.Friction: Introduce challenges like one-time passwords (OTPs) to slow down attackers and verify login attempts.Payment Holds: Temporarily hold suspicious transactions until verification with the user is complete.
4. Fraudulent Activity: Once in, the attacker can engage in various fraudulent activities. This might involve unauthorized purchases using stored payment information or transferring funds to attacker-controlled accounts. In some cases, they might lurk undetected, monitoring the account for a period before initiating larger thefts.
How to Stop Them:
- Monitor for unusual transaction patterns: some textHigher than average order values.Changes in billing addresses.Rapid succession of high-value transactions.
- Be alert to additional suspicious activities: These can include:some textTransfers to risky accounts with known fraud history.Changes in geolocation.Tying multiple cards to an account in a short period.Unusual input of card details.Transactions conducted at odd hours.
5. Covering Tracks: To avoid getting caught, attackers might erase the victim's browsing history or disable security features like two-factor authentication, hindering recovery efforts.
How to Stop Them:
- Monitor for suspicious account management activities: Look for signs of tampering, such as:some textClearing logs or order history.Removing transaction records.Deleting chats or listings.Changing security settings (2FA, email).
By understanding these stages and implementing the recommended actions, you can significantly reduce the risk of ATOs and protect your users. Remember, a layered security approach that combines monitoring, investigation, and additional verification steps is crucial for robust account protection.
Account Takeover Impact Across Industries
While the goal of account takeovers is criminal access for malicious activity - the methods differ across industries. This section explores common ATO scenarios in key sectors, highlighting how fraudsters exploit stolen accounts. By understanding these tactics and warning signs, businesses can strengthen their defenses against ATO attacks.
Marketplaces (Seller/Buyer Accounts):
- Fake it to steal it: Fraudsters create counterfeit seller listings to trick buyers into sending money for non-existent goods.
- Payment hijacking: They alter payment details to divert funds from legitimate transactions or disappear with payments altogether, leaving buyers empty-handed.
- Buyer beware: Compromised buyer accounts become tools for unauthorized purchases, with fraudsters exploiting stored payment methods or loyalty points for personal gain. A tactic known as triangulation fraud involves swapping the payment source with a stolen card, acquiring goods with ill-gotten funds, and then reselling them elsewhere.
Ecommerce:
- Stolen swipes: Attackers leverage stolen accounts to make fraudulent purchases using the victim's saved payment card details.
- Loyalty larceny: Accumulated loyalty points become easy pickings for fraudsters who exploit compromised accounts.
- Phantom packages: Often, goods purchased with stolen credentials are shipped to undisclosed locations, making recovery difficult. Additionally, they might create fake refund requests to siphon funds from the legitimate account holder.
Fintech & Banks:
- Financial maneuvering: Fraudsters with access to fintech or bank accounts can execute unauthorized fund transfers, apply for loans in the victim's name, or even use these platforms to launder money through a series of complex, seemingly legitimate transactions.
- Identity theft in action: Similar to traditional bank accounts, stolen logins allow criminals to steal funds directly, transfer ill-gotten gains from other scams, or apply for new credit cards and loans using the victim's identity.
Cryptocurrency:
- Draining the digital vault: Account takeover in a crypto wallet grants fraudsters access to pilfer virtual currency. These stolen funds can be transferred to untraceable wallets, rapidly exchanged for other assets to avoid detection, or even used to fuel other fraudulent schemes.
iGaming:
- Playing dirty: A compromised iGaming account allows attackers to steal a player's hard-earned winnings, manipulate games for unfair advantages, or exploit referral bonuses. These compromised accounts can also serve as a launchpad for more extensive attacks, like game rigging or chip dumping.
Beyond the Basics: Building a Comprehensive Security Strategy
While basic measures provide a strong foundation, consider a more comprehensive approach to ATO prevention. Explore solutions that offer advanced threat detection and invest in security tools that leverage threat intelligence to identify and block sophisticated ATO tactics employed by attackers.
Here's how organizations can further strengthen their defenses:
- Implement Additional Authentications: Very few legitimate users log in through remote screen-sharing software. Implementing additional authentication steps for such login attempts can help prevent unauthorized access while still allowing genuine users to complete the process. Similarly, detecting logins originating from emulators (software that mimics another device) can be a red flag for potential ATOs.
- Utilizing Collective Intelligence: By analyzing login attempts across the entire user base, organizations can identify anomalies that might indicate a wider attack. For instance, a surge of login attempts with similar suspicious characteristics (unusual locations, time of day) might suggest a coordinated ATO attempt.
- Combined Behavior + Device Analysis: Fraudsters often try to manipulate device signals like location or their IP using a VPN or proxy. By combining more detailed behavior analysis with other device signals, organizations can ferret out suspicious activity.
- Advanced User Identification: Implementing a "Same User Score" allows businesses to track user behavior patterns associated with specific devices. This can help detect risky behavior on compromised devices.
- Integrating 3rd Party Data: Third-party data sources, such as compromised credential databases and historical fraud indicators, can be invaluable. Integrating this enriched data with device signals and user behavior allows organizations to create a comprehensive risk profile.
- Identify SIM Swapping: By utilizing data feeds and anomaly detection techniques, organizations can identify potential SIM swaps, where a hacker gains control of a user's phone number to facilitate unauthorized account access.
- Proactive Data Breach Monitoring: Regularly monitoring external data breaches for compromised user credentials can help identify potential targets for ATOs. Early detection allows businesses to take steps to protect these users, such as prompting them to change their passwords.
By adopting a layered security approach and staying informed about evolving threats, businesses can significantly mitigate the risk of account takeovers and protect their valuable assets.
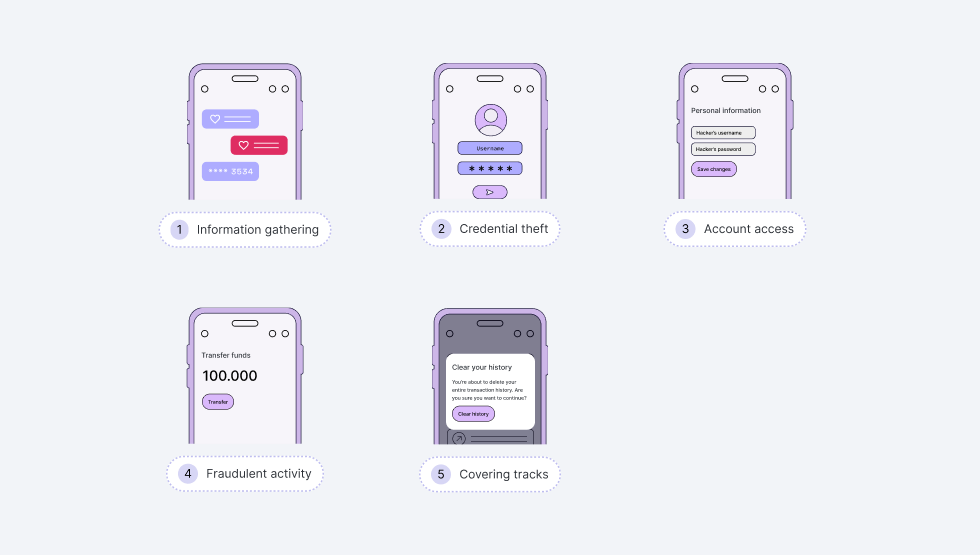
Sardine: Your Partner in Account Security
Sardine provides all the latest tools in the fight against fraud by capturing data across the customer lifecycle. It is a unified security platform that helps businesses prevent ATOs and protect their users. Here's how Sardine can help:
- Real-Time Risk Assessment: Sardine allows businesses to assess transaction risk in real time by directly querying its network of users, devices, entities, and counterparties.
- Data Aggregation: Sardine offers access to data from over 35 integrated providers, including phone, email, social security number (SSN), telecommunications (telco), and banking transaction data. This data is rigorously tested for coverage, performance, and quality.
- Identify Users and Devices: Sardine helps businesses identify who is creating accounts, logging in, and transacting on their platform at account creation and throughout the customer lifecycle. This allows companies to recognize trusted users and provide a smooth experience while protecting them from fraud.
- Thorough Customer Identification: Sardine provides comprehensive customer due diligence (CDD) and enhanced due diligence (EDD) services, including Know Your Customer (KYC), Know Your Business (KYB), document verification, and behavior biometrics.
- Risk-Based User Screening: Sardine helps businesses screen and monitor users against global watchlists for sanctions, Politically Exposed Persons (PEP), Specially Designated Nationals (SDN), and Adverse Media.
This translates to faster approvals, quicker sign-ups, and happier customers who aren't discouraged by overly restrictive measures. With trust established, you can offer higher funding and purchase limits, potentially boosting their average order value and overall loyalty to your platform.
The Ongoing Battle Against Account Takeovers
ATOs don't have to be a fact of life. By combining all available tactics and data, we can dramatically reduce the risk of account takeovers. By employing a strategy that combines preventive tactics with advanced threat detection and security tools leveraging threat intelligence, you can effectively identify and block sophisticated attacks. A proactive and comprehensive approach will make all the difference when safeguarding your business.
Sardine has supported more than 250 businesses and stopped $21.3 billion in fraud attempts. If you’re interested in learning more about Sardine’s security platform and our easy, low-lift integration, contact us.