SMS verifications are everywhere these days — whether you’re an online bank, a food delivery service, or even a dating app, chances are that you use SMS verification to validate customer identities. But while SMS verifies that a customer has access to the code that was sent, it doesn’t necessarily mean that user actually owns or is associated with that phone number.
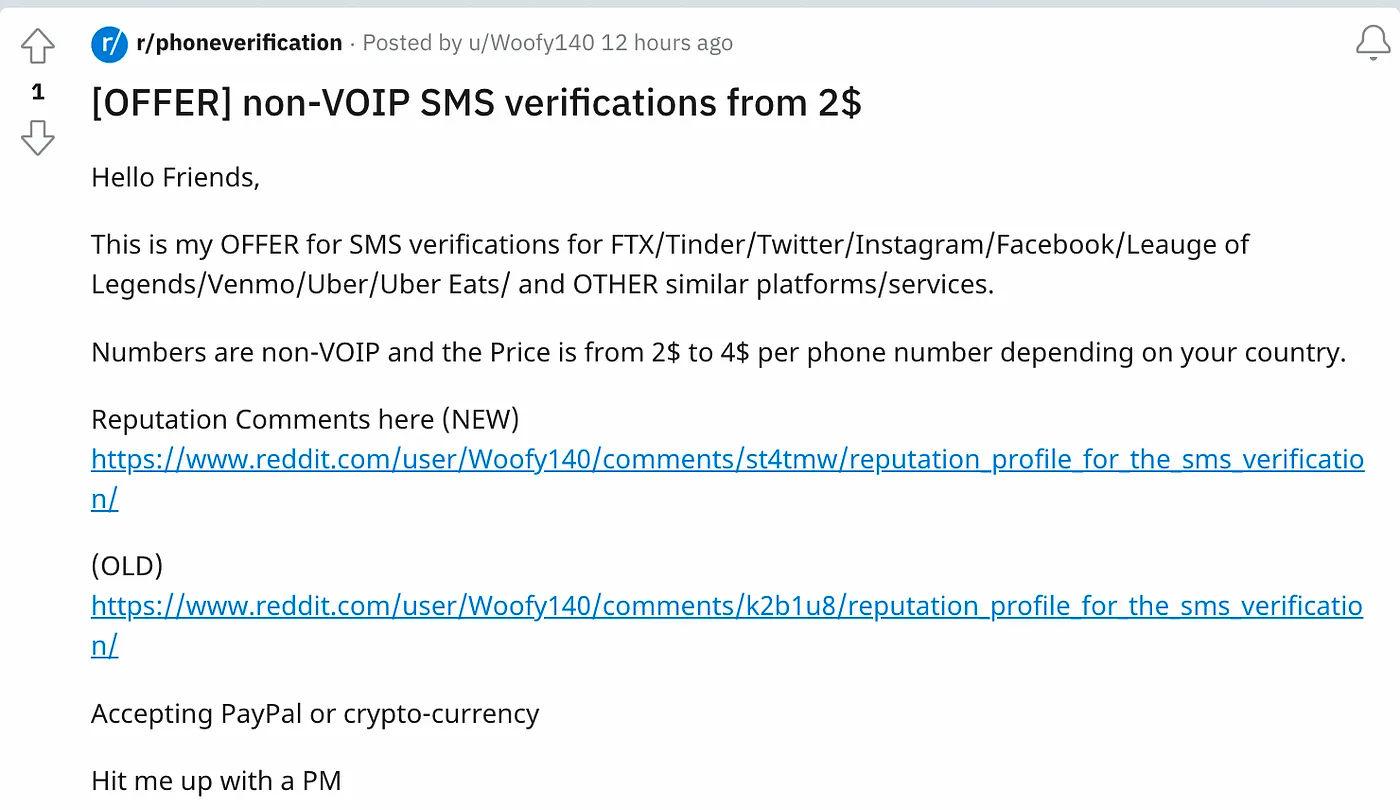
Fraudsters take advantage of this loophole all the time — it’s easy to buy 3rd-party SMS verification on sites like https://smsreceivefree.com. There’s even a crowdsourced marketplace for 3rd party SMS verification on reddit — r/phoneverification. Say you’re a fraudster looking to create an account using a synthetic identity from Mexico — you can find someone in this group who owns a Mexican number and they’ll help you complete SMS verification for a fee.
While this behavior can diminish the effectiveness of phone number verification in fraud and compliance programs, there are ways to fight back. At Sardine we help FinTech’s and crypto companies do just that — here are 3 mechanisms we use to help our customers curb fraud by maximizing the value of phone authentication at sign-up:
1. Compare Telco data associated with the phone number with user information
Sardine provides our customers with an orchestration platform that synthesizes and enriches customer data and then uses machine learning and rules to identify risky signals. Sardine utilizes several enrichment providers that together give us global coverage of Telco data. This gives us the power to determine if a phone number is actually associated with the identity provided at onboarding and for how long.
2. Use device and behavioral signals to your advantage
Let’s imagine a scenario where you are a digital good merchant and you require customers to complete SMS verification at onboarding. Let’s also say that your mobile app is designed to directly retrieve the SMS code from mobile devices (using Android/iOS APIs) and autofill it in the app.
In this case, an autofill event is a positive user signal because it means the user owns the phone/number they signed up with. On the other hand, a fraudster who purchased SMS verification from a 3rd party would have to briefly exit your app to retrieve the code during onboarding and would have no autofill event. Leaving and coming back to the app would also be a bad signal.
One of the most powerful anti-fraud tools Sardine provides our customers with is the ability to collect device and behavior biometrics data. Among the signals collected are 1) autofill events and 2) what we call a ‘context switches’, which is when a user changes windows like the fraudster did in the scenario above. Behavioral signals like these are a first line of defense to detect aberrant behavior and catch bad actors.
3. Build a dynamic KYC/user onboarding program
No one likes a long account sign-up process. At Sardine, we take this to heart and help our customers create dynamic onboarding/KYC programs. Start by onboarding users with their basic information and if no risk signals are flagged (phone number matches email/name identity, etc.) then let them onboard, however if initial checks display risky signals, require steps-ups like SSN, Document/Liveness checks and more. Sardine allows you to easily orchestrate all of this in real-time.
Wrap-Up
Fraudsters are constantly getting more sophisticated, requiring that digital goods and services providers do the same. By working with a partner that’s built to evolve alongside fraud you can sleep soundly knowing that you have the tools to fight back.
btw if you find solving problems like this as exciting as we do check out our job board!