Account Takeover (ATO)
Account Takeover (ATO)
Protect your users from scams and social engineering
Detect unauthorized access during logins and live sessions before financial loss occurs.
Correlate device, behavior, and session activity to identify account compromise early.
Login Protection
Credential stuffing and bot-driven takeover
Shut down automated login attacks without adding unnecessary friction for legitimate users.
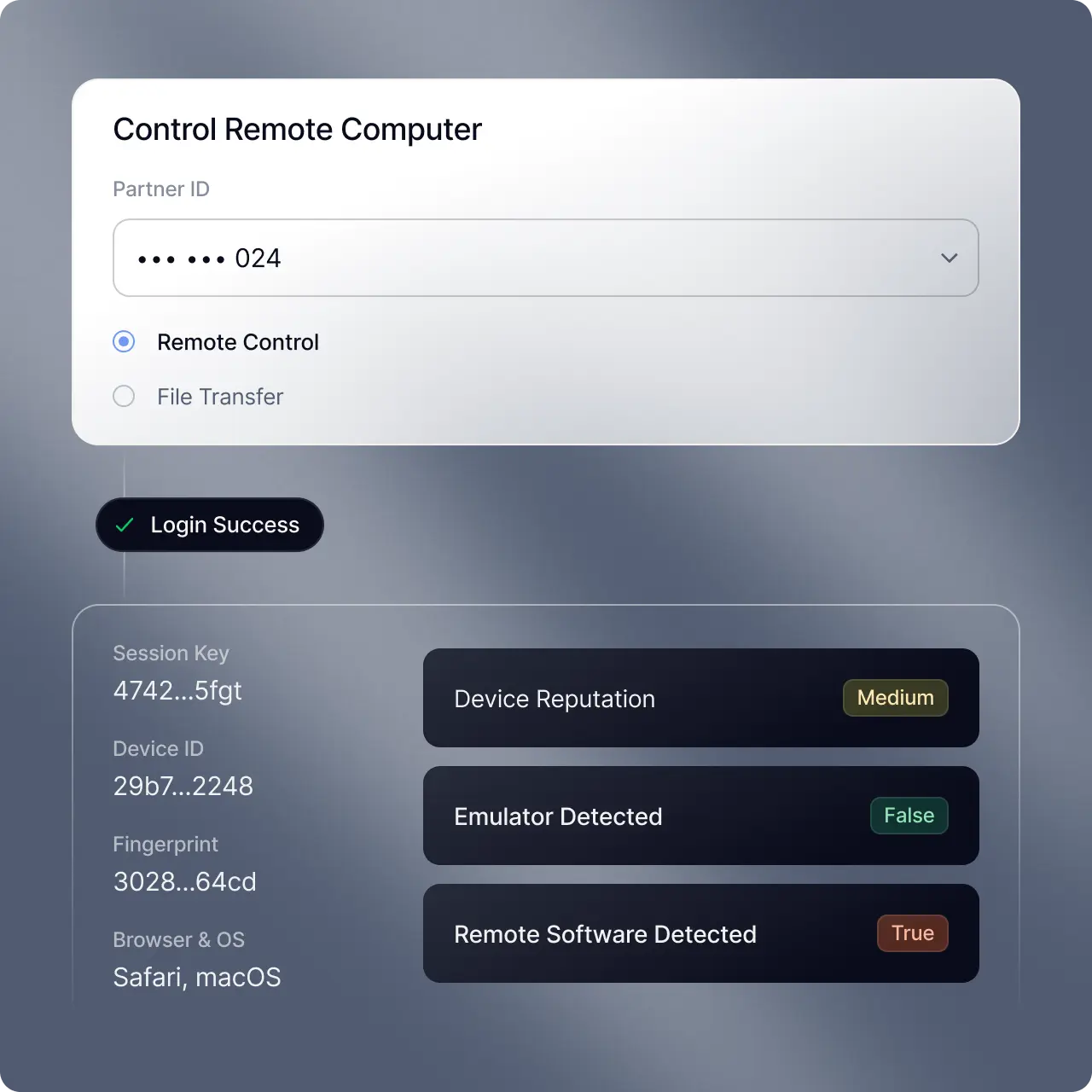
Identify when headless browsers, residential proxies, emulators, and virtual machines are active during a session.
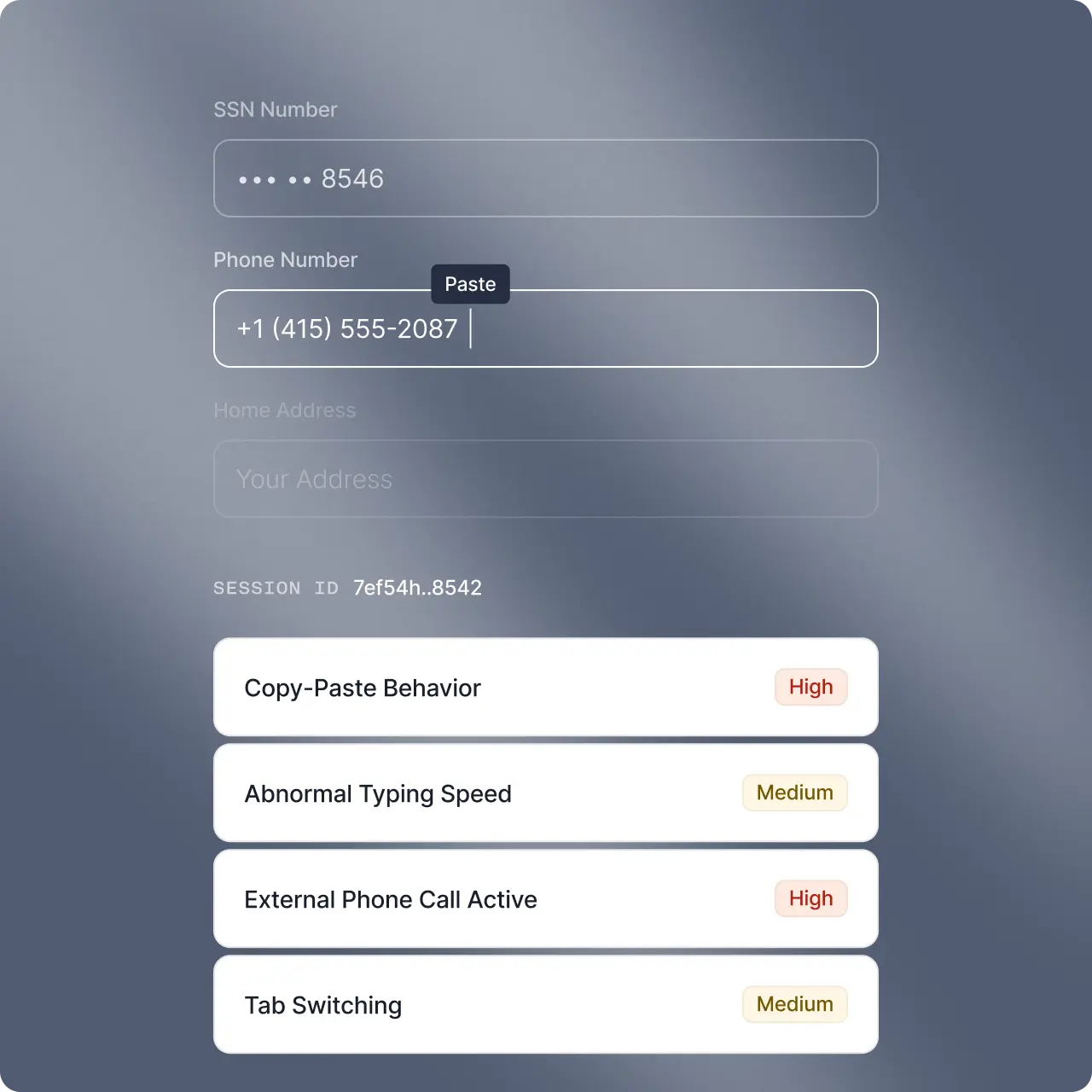
Identify scripted typing cadence, expert mouse movement, and unnatural navigation timing.
Analyze login bursts, password spraying, shared device IDs, and IP clustering to detect coordinated activity.
Account Monitoring
Unauthorized account changes and profile manipulation
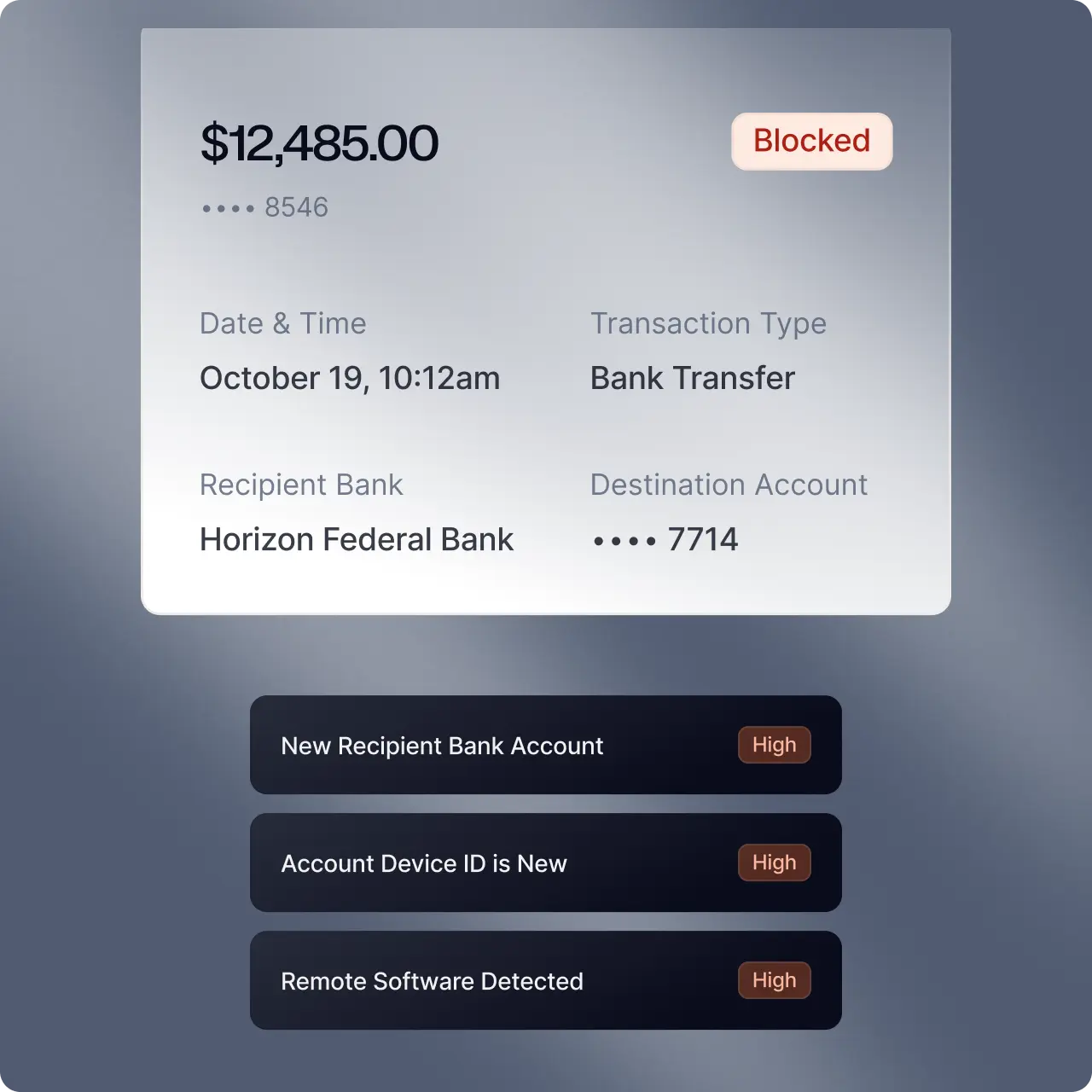
Stop account takeover attempts before they turn into downstream fraud.
Monitor email, phone, password, MFA, and trusted device updates using session-level device integrity and behavioral risk signals.
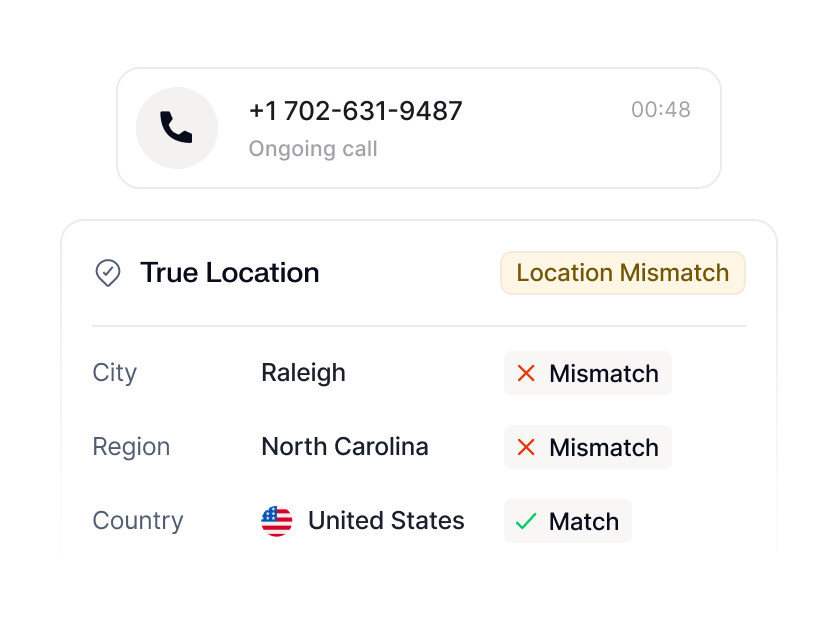
Connect VPN use, IP mismatch, timezone anomalies, and behavioral shifts to detect takeover attempts.
Dynamically restrict sessions before new payees, wires, ACH, or card activity occur.
Cross-Channel Risk
Cross-channel account takeover protection
Eliminate blind spots between digital, mobile, and call center systems.
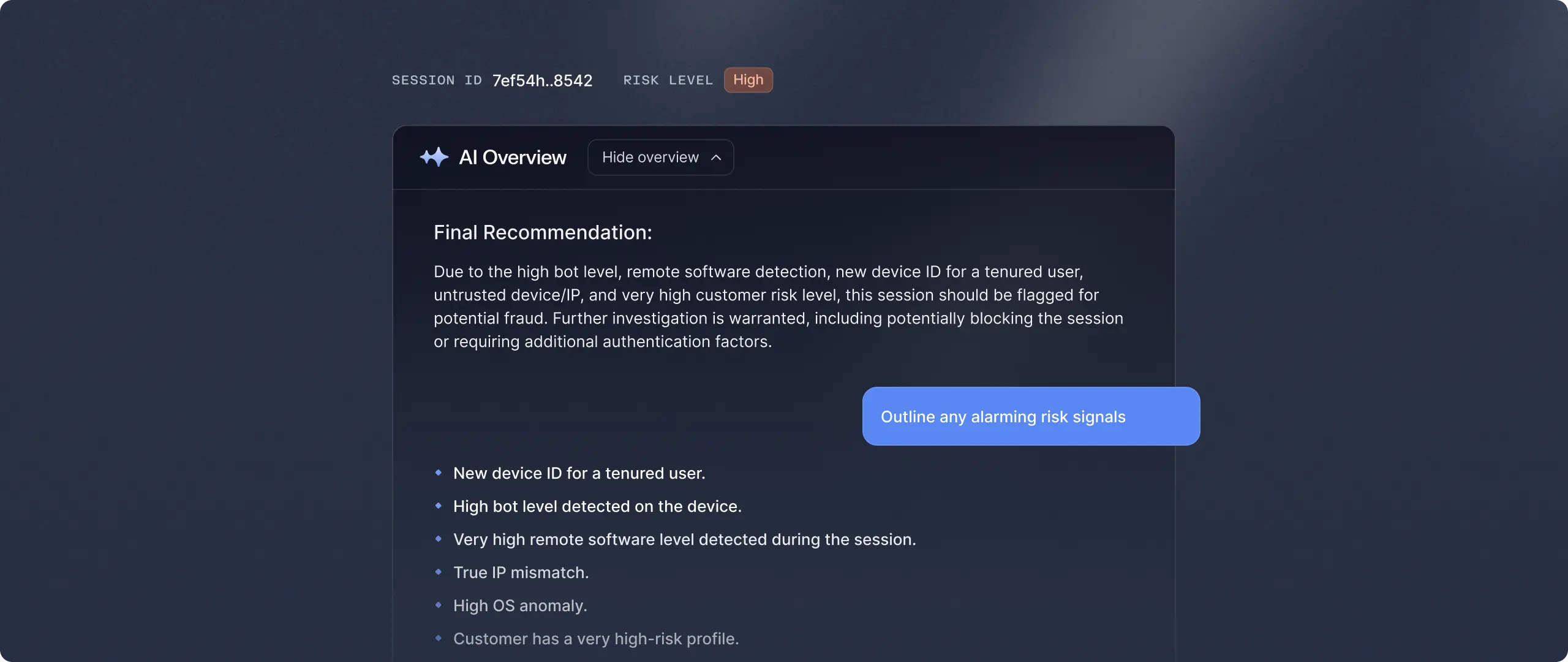
AI agents for adaptive account takeover defense
Continuously investigate, summarize, and escalate ATO risk in real-time.
ATO protection that's built for real-world attacks
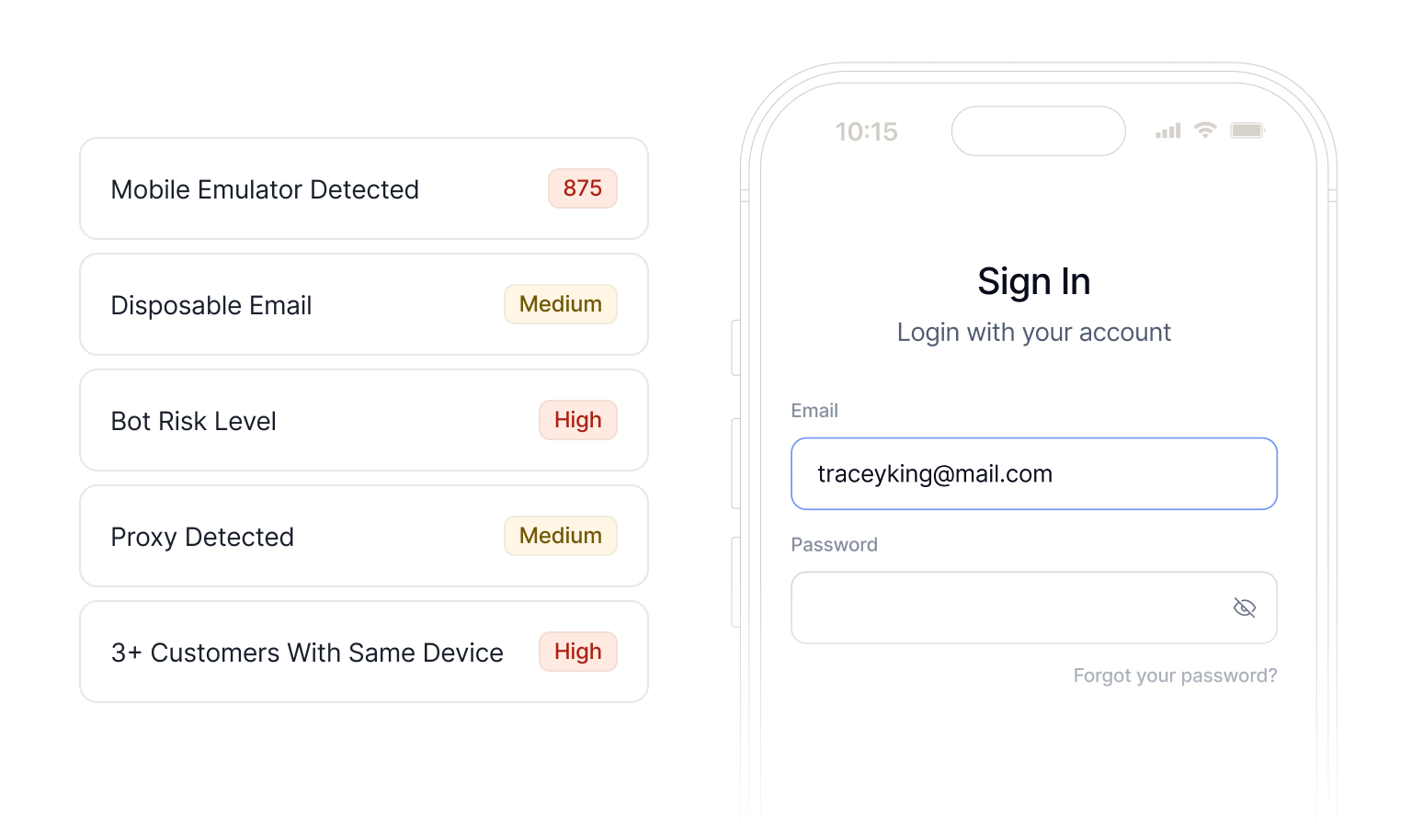
Device & Behavior
Deeply integrated device and behavior signals across the customer lifecycle
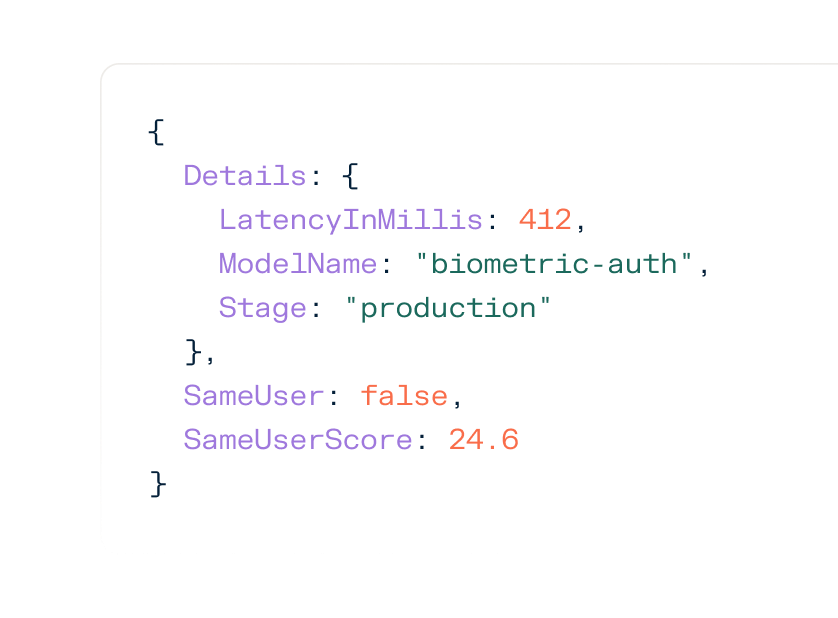
Assess real user interaction and device integrity to uncover emulators, remote access tools, obfuscation, and bot automation.

Case Management
Record, replay, and explain every takeover decision
Capture and replay full session activity across login, profile changes, and payments to understand exactly how compromise occurred. Confirm coached behavior, remote access tools, or impersonation while documenting every action with regulator-ready risk signals.
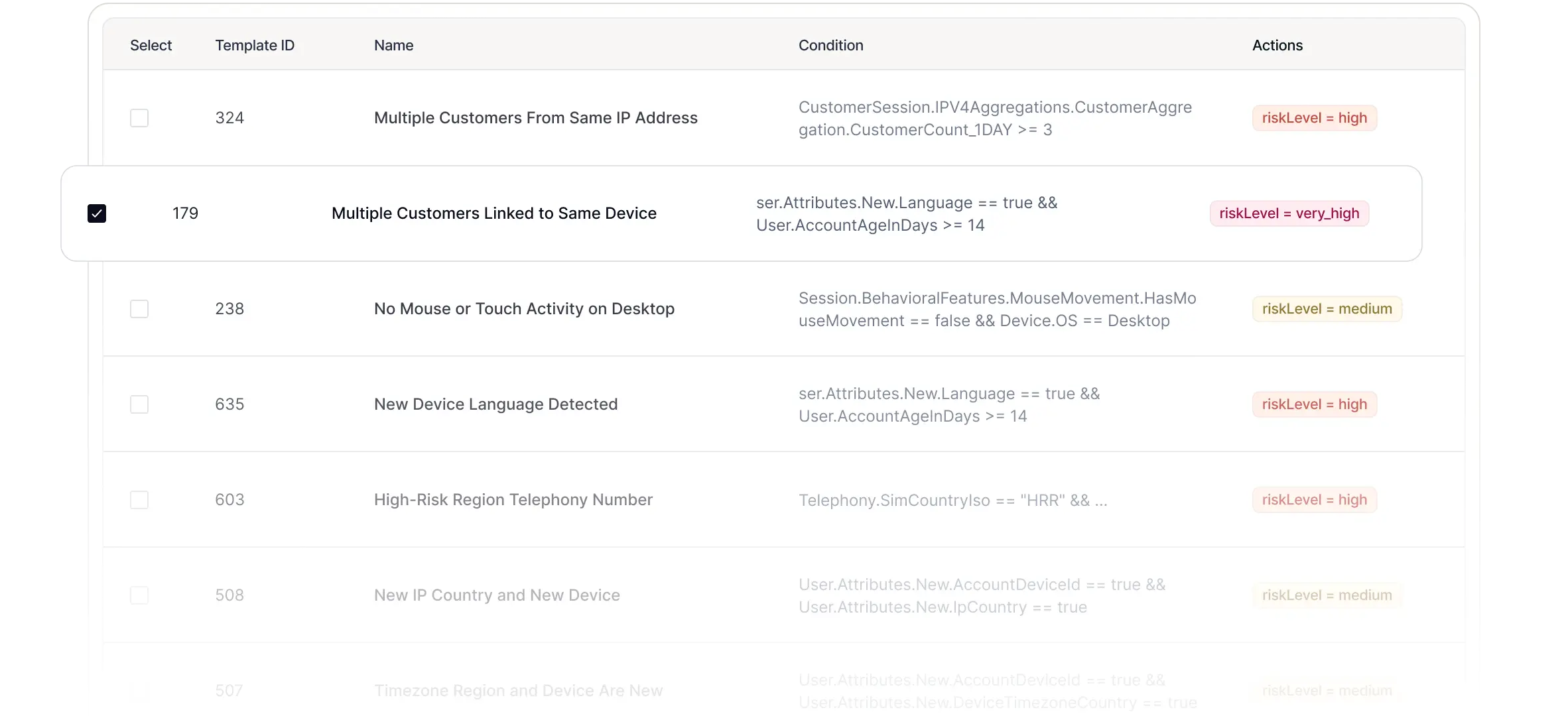
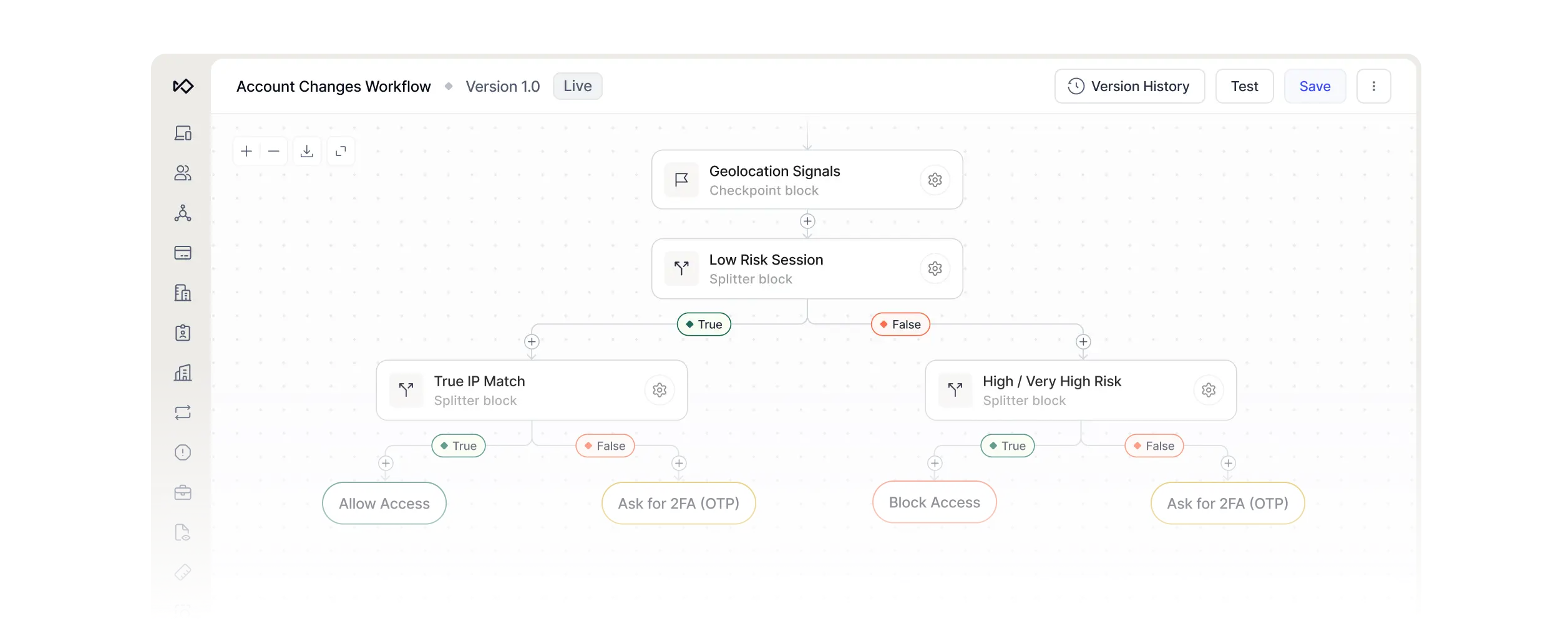
Rules & Workflows
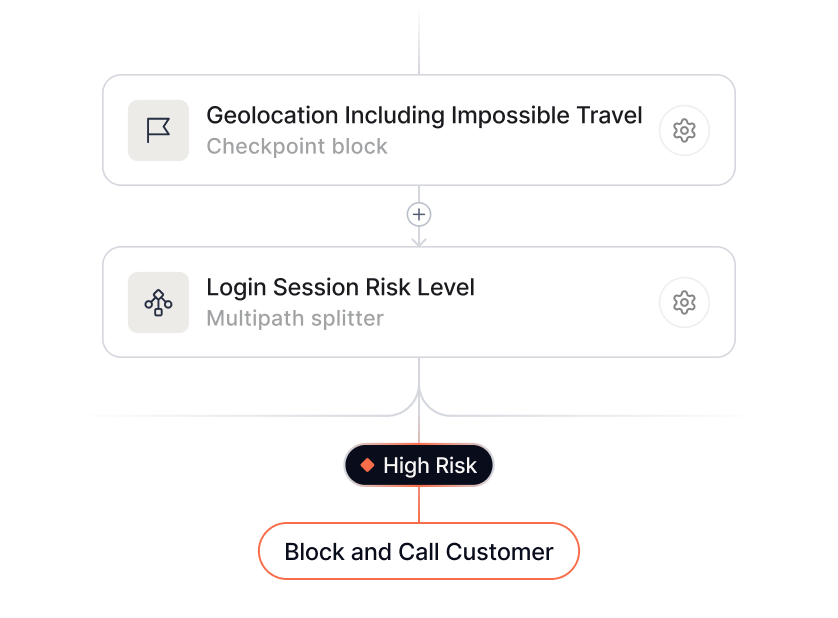
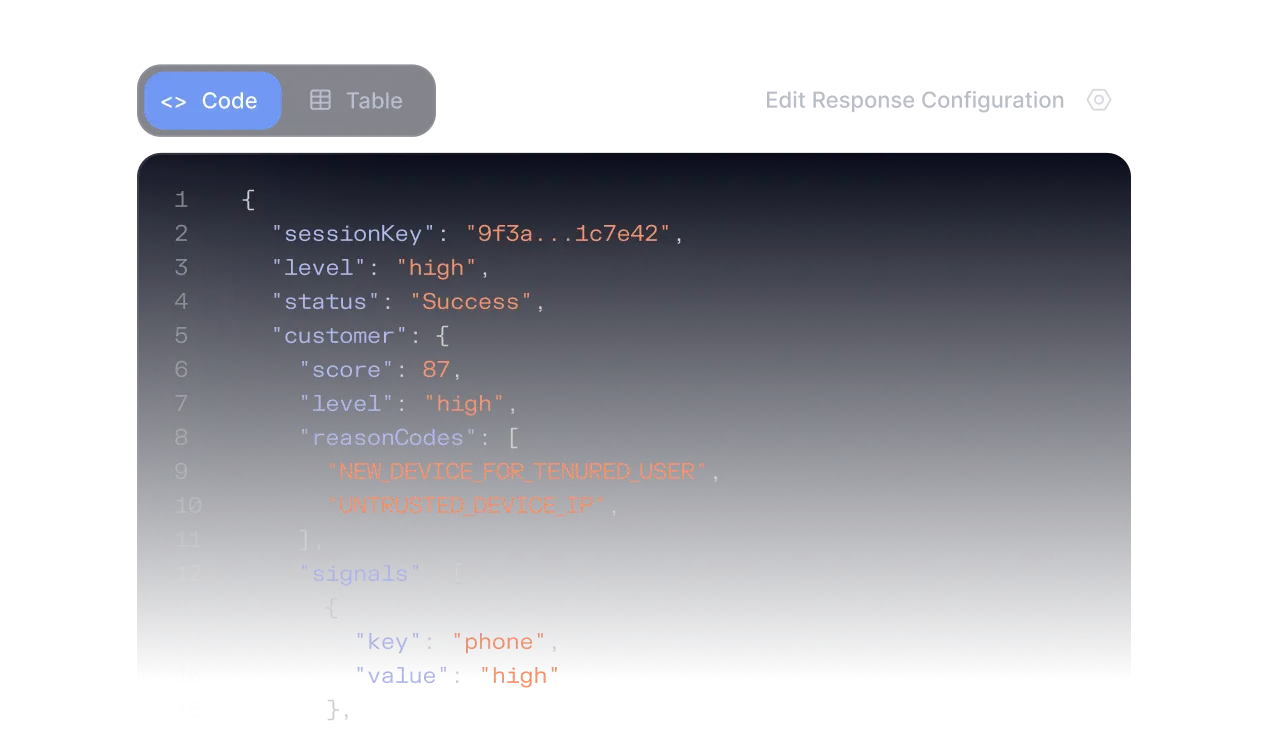
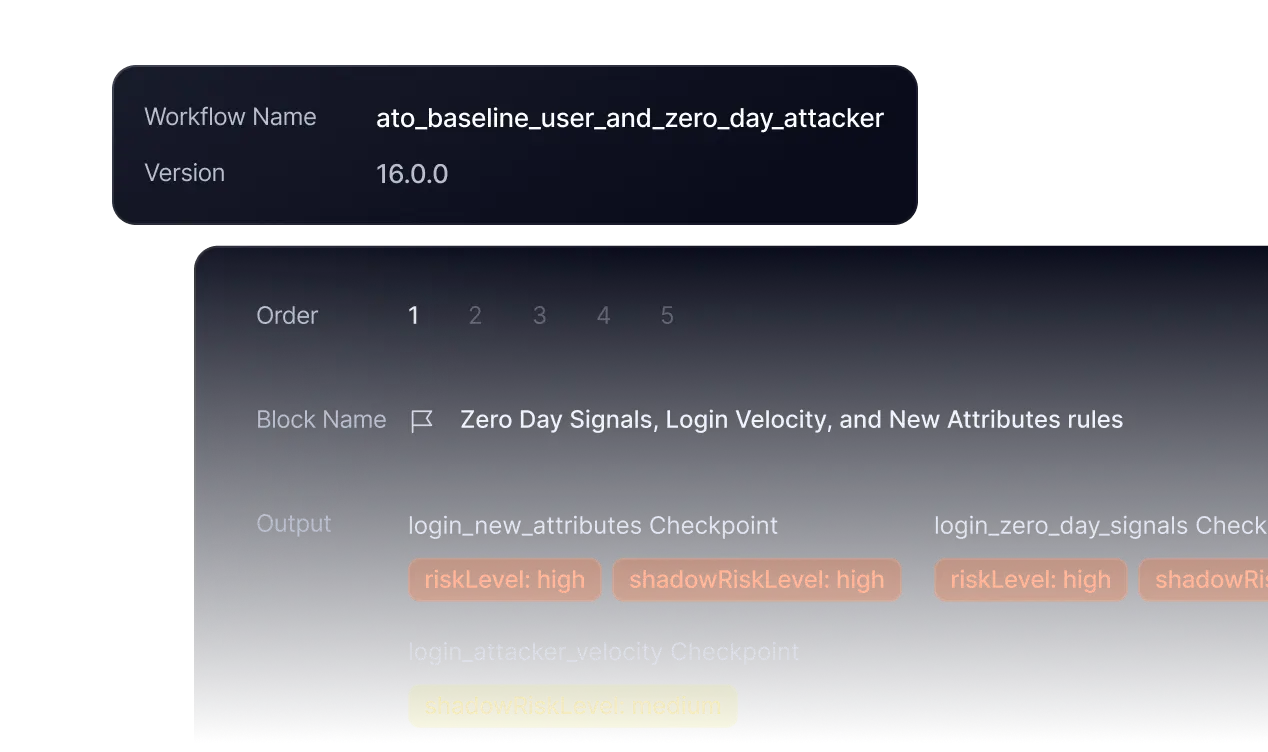
Explainable session controls across login, profile updates, and payments
Define clear, auditable controls to step up authentication, restrict actions, or block sessions instantly when risk changes across digital, mobile, and call center channels.
One platform for account takeover, fraud, and scams
Frequently
asked questions

How is Sardine’s account takeover detection different from traditional fraud systems?
Most systems focus on transaction monitoring after money moves. Sardine evaluates risk during login and live session activity by combining device integrity, behavioral signals, infrastructure reuse, and account history.
This allows teams to detect phishing, social engineering, credential stuffing, and remote access tools before profile changes or payments occur, reducing downstream fraud and remediation workload.
How does Sardine detect coordinated credential stuffing or bot campaigns?
Sardine generates a visitor fingerprint from device and environment signals during authentication flows and analyzes velocity patterns, shared infrastructure, and behavioral anomalies to detect coordinated credential stuffing and bot campaigns.
By identifying patterns such as shared IP infrastructure, proxy and VPN networks, visitor fingerprint similarities, and reused automation frameworks, Sardine can surface coordinated campaigns rather than isolated login attempts.
Can Sardine automatically suggest new rules when attack patterns change?
Yes. Sardine’s anomaly engine continuously monitors login and session traffic for deviations in behavior, velocity, and infrastructure patterns.
When new attack tactics emerge, the platform recommends rules and thresholds based on live data. Teams can deploy these in copilot mode or fully autonomous workflows, with audit-ready documentation of every change.
How does Sardine support investigation and regulatory review?
Sardine captures and replays full customer sessions across login, profile changes, and payments. Fraud teams can confirm coached behavior, impersonation, or remote access tools visually, not just through risk scores.
The platform generates explainable risk signals and regulator-ready case summaries, with documented step-ups, restrictions, and overrides suitable for internal audit, examiners, and board reporting.
Can AI agents operate autonomously without losing control?
Yes. Sardine agents can run in copilot or autonomous mode.
Through the Agentic Oversight Framework, teams sample and review agent decisions for ongoing calibration. This ensures governance, transparency, and above-line or below-line validation while still automating alert resolution and investigation workflows.