Cross-Industry Fraud Intelligence
Cross-Industry Fraud Intelligence
Stop more financial crime with shared intelligence
Use shared signals from Sardine’s network and Sonar’s cross-industry consortium to spot first-party fraud, counterparty risk, and AML exposure earlier.
Tap into the fastest growing consortium for global fraud data

Assess counterparty risk beyond your own data
Connect signals on users and businesses across financial institutions and merchants to uncover hidden risks.

Learn from fraud patterns across the network
See how fraud is showing up at other institutions to identify new attack patterns earlier and proactively stop them.
Uncover users with a previous history of fraud
Know when a user has been tied to suspicious or confirmed activity beyond your own portfolio, so your team can make better informed risk decisions.
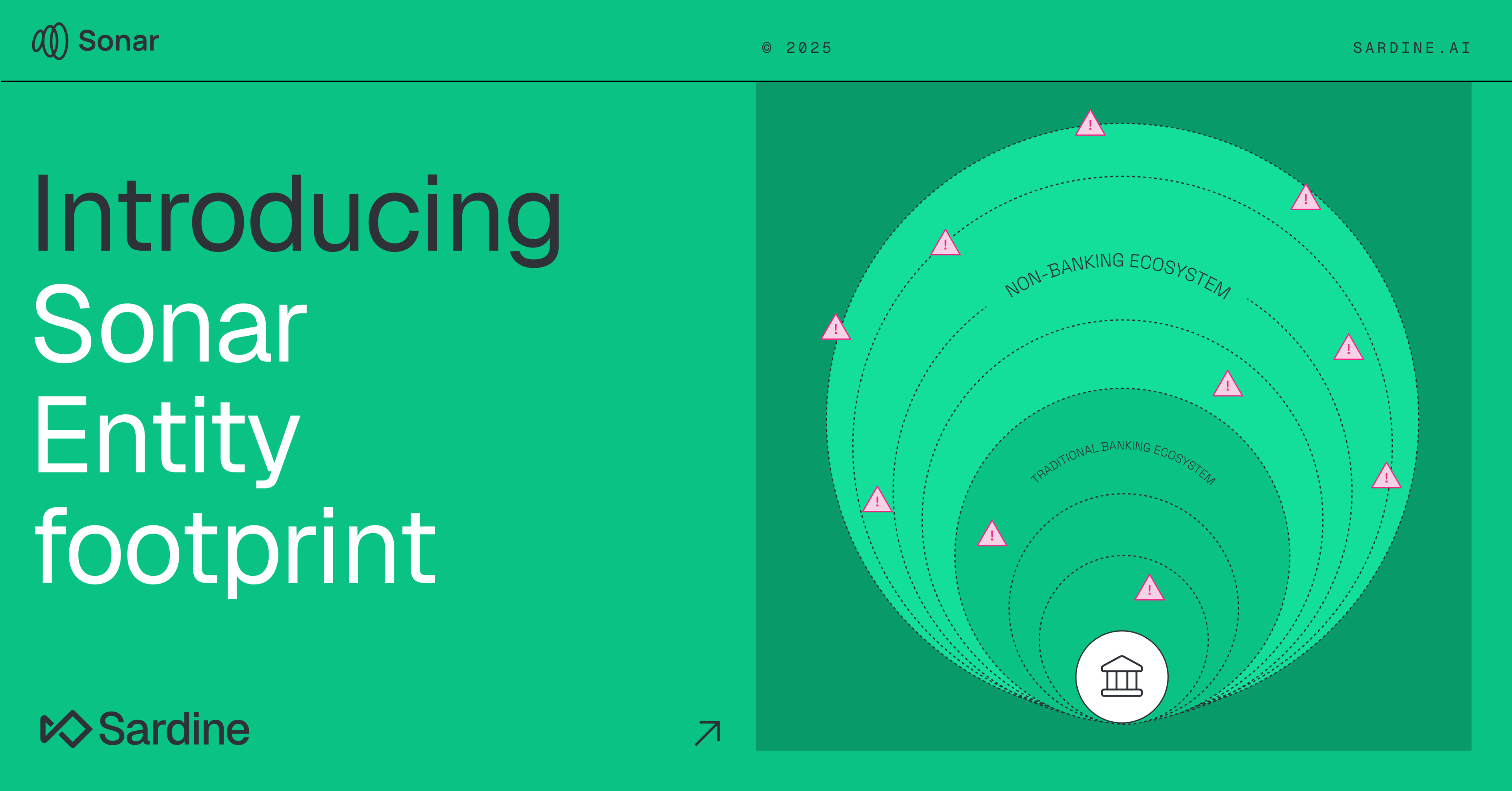
A live data consortium powering fraud and AML decisions across financial services.

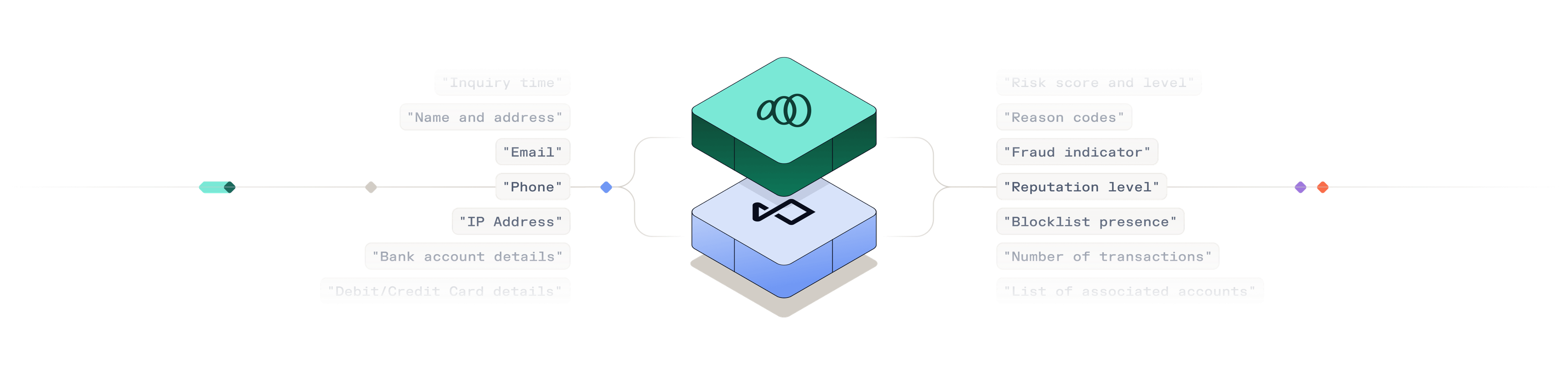
Inquire counterparty risk before funds move
Send requests using identifiable inputs such as name, email, phone, IP, address, bank account details, or wallet data. Receive structured responses including fraud indicators, risk levels, behavioral signals, watchlist details, and counterparty associations, before accepting or sending funds
Tap into fraud, AML, and credit signals
Access configurable data packs that deliver fraud, AML, and credit intelligence through a single integration. Evaluate device and behavioral risk, ACH and card exposure, sanctions and PEP risk, adverse media, and chargeback history in one structured response for faster decisions across onboarding, payments, and ongoing monitoring.
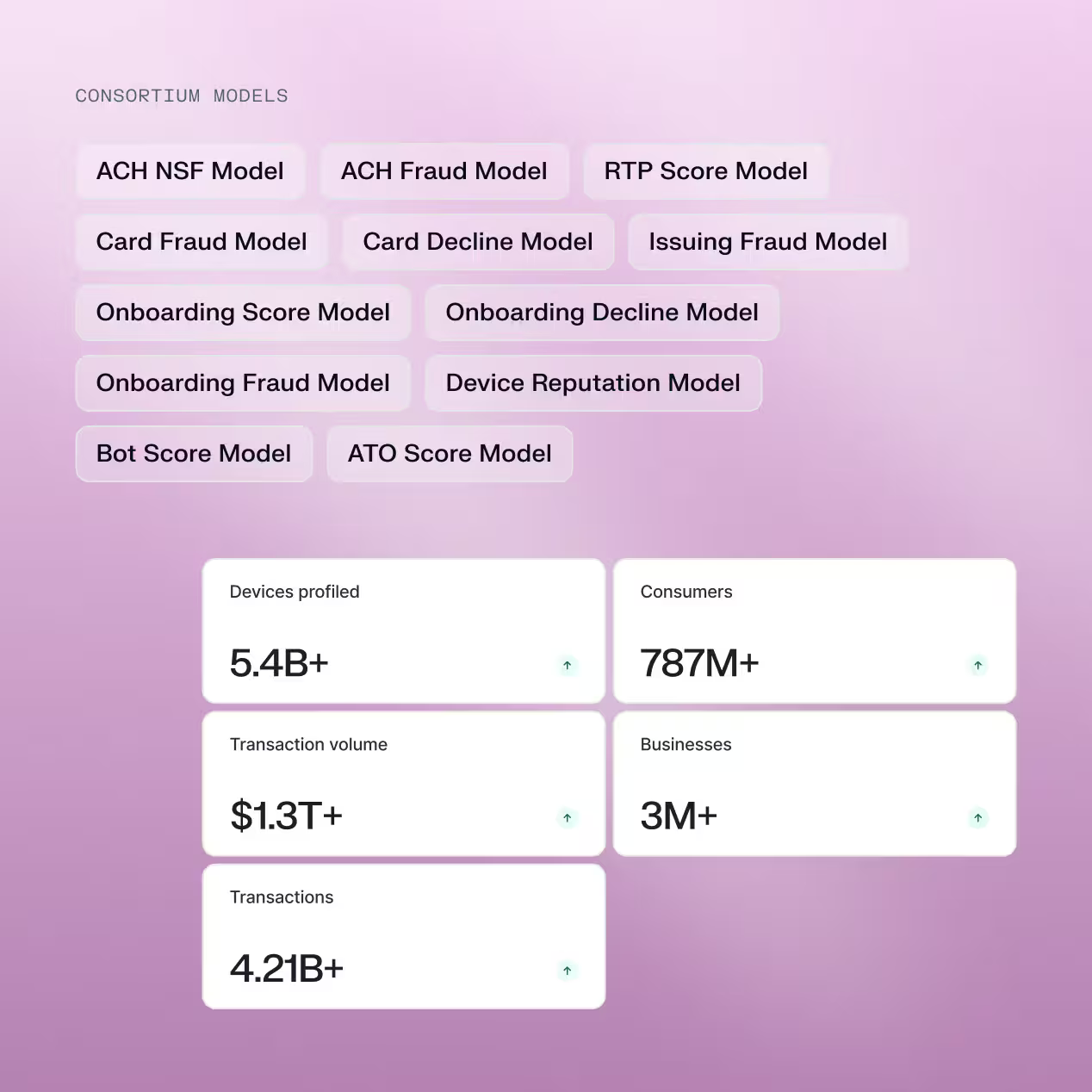
Leverage cross-industry fraud intelligence spanning billions of devices and consumers
Strengthen decisions with intelligence drawn from a fast-growing global fraud consortium that spans 5.4B devices, 787M consumers, 3M small businesses, and over $1.13T in transaction volume. Use consortium-derived signals such as device reputation, time since first seen, network associations, and identity aggregation to uncover coordinated fraud patterns across institutions.
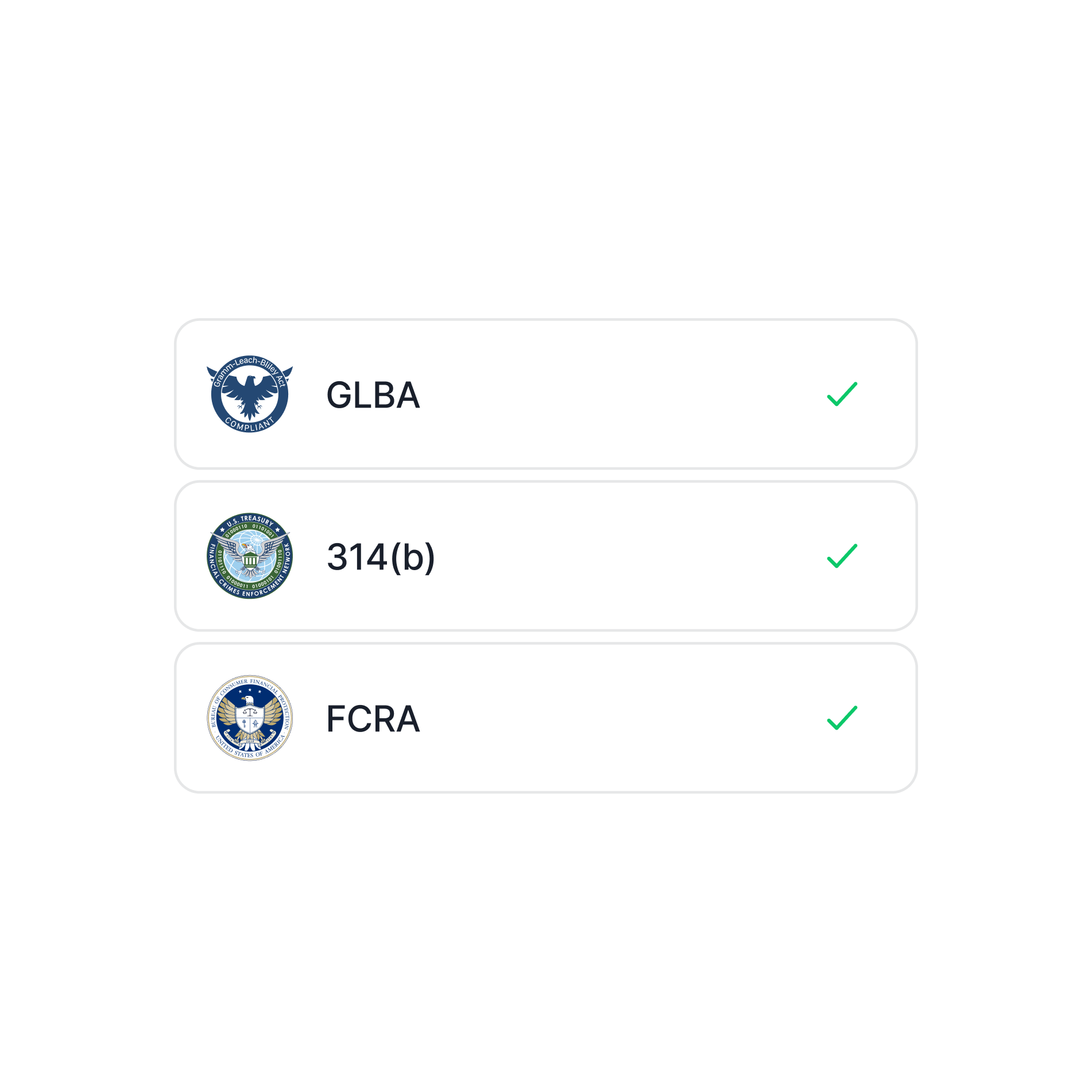
Share intelligence responsibly
Sardine’s consortium operates under a structured governance model with clearly defined operating rules, data contribution standards, and usage guardrails. Data sharing occurs within appropriate legal frameworks, including GLBA, 314(b), and FCRA, ensuring compliant collaboration across institutions. Sonar members help shape governance standards and network policies, while Sardine provides the infrastructure, security, and controls to support responsible data exchange.

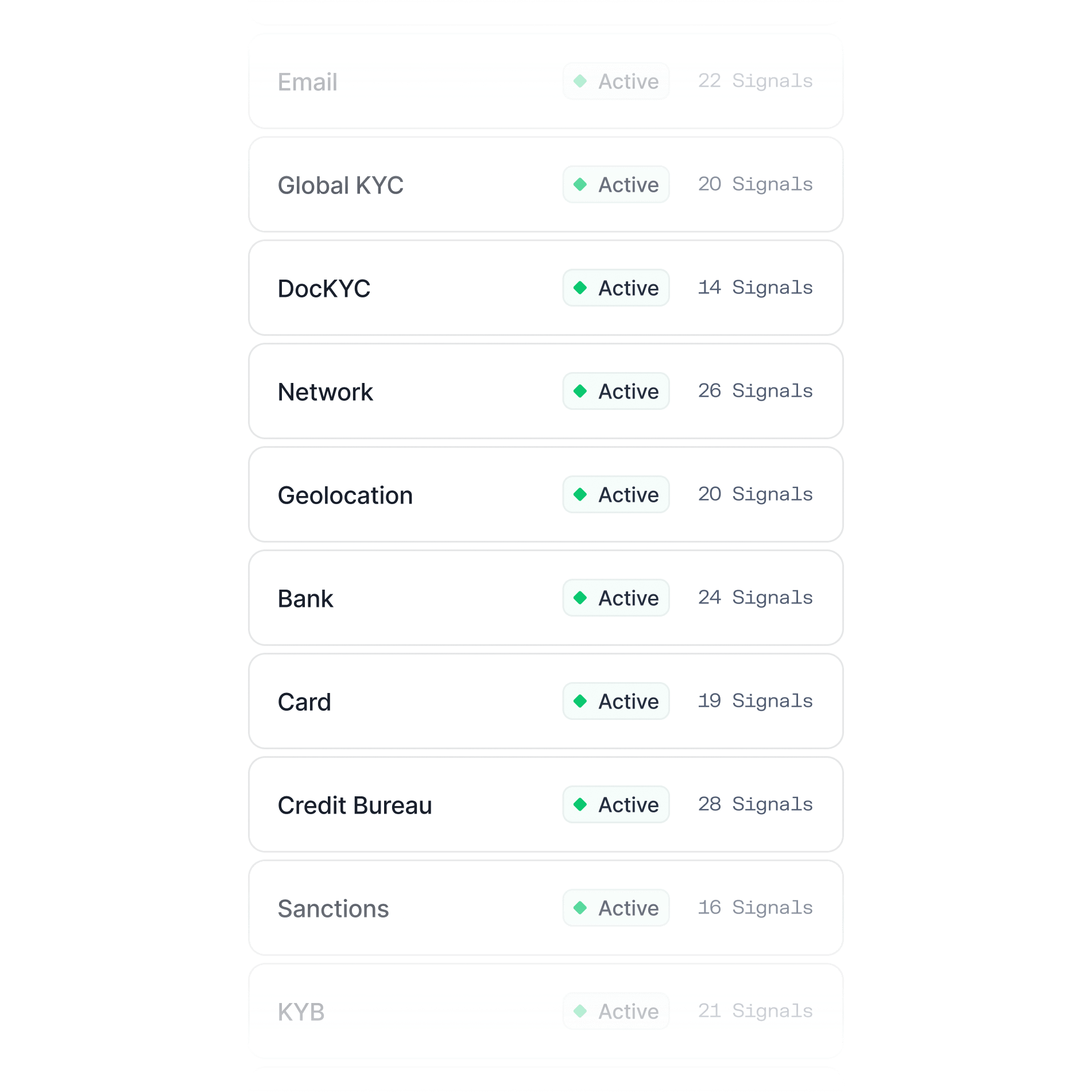
Tap into a live network of data providers
Extend consortium insights with a curated ecosystem of integrated data partners across phone and email intelligence, bank account and ACH verification, sanctions and adverse media screening, crypto monitoring, identity verification, and KYB. Access signals for onboarding, ACH and wire risk, crypto transactions, and AML monitoring, all delivered through a single integration layer.
Turn consortium signals into decisions
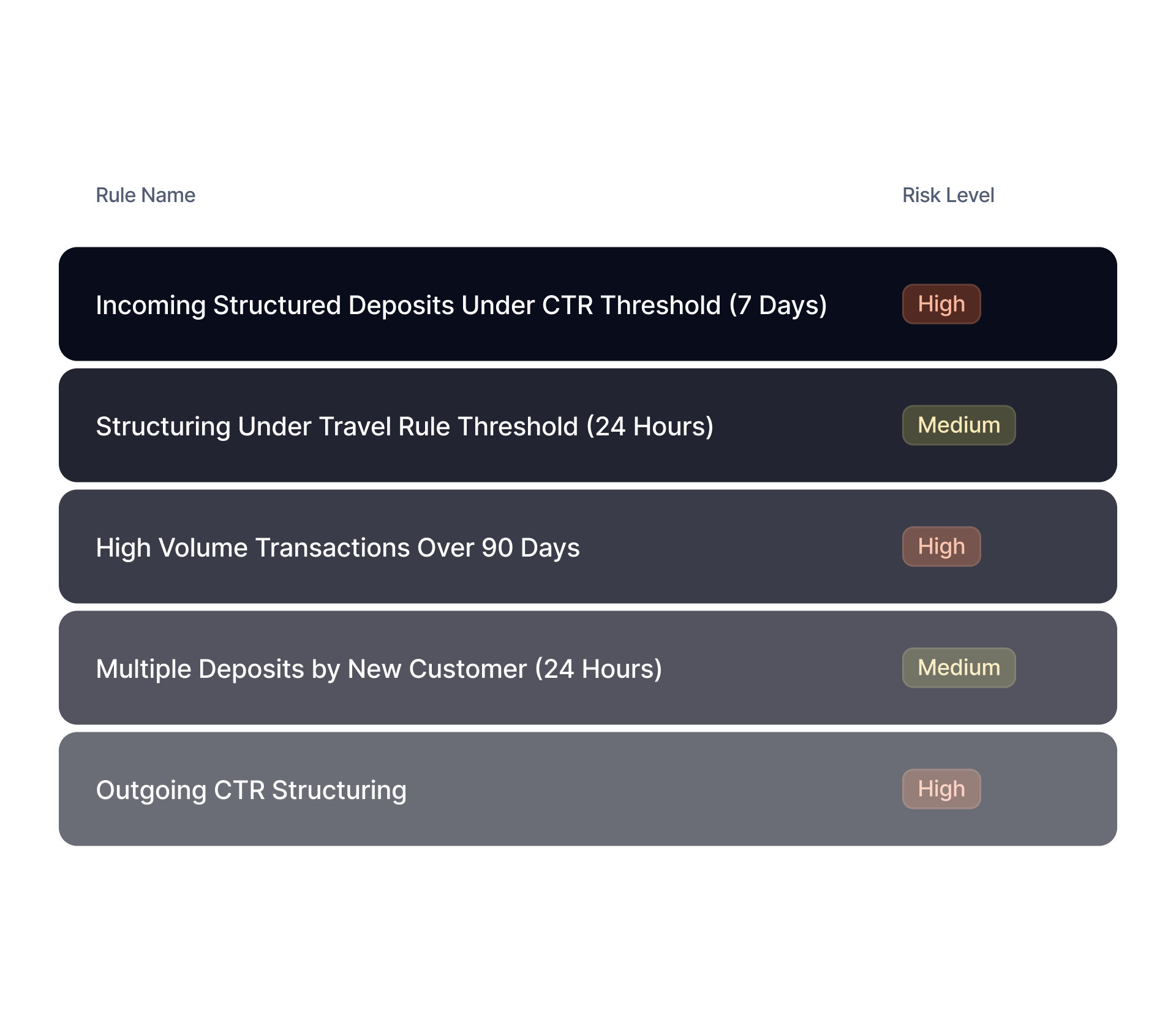
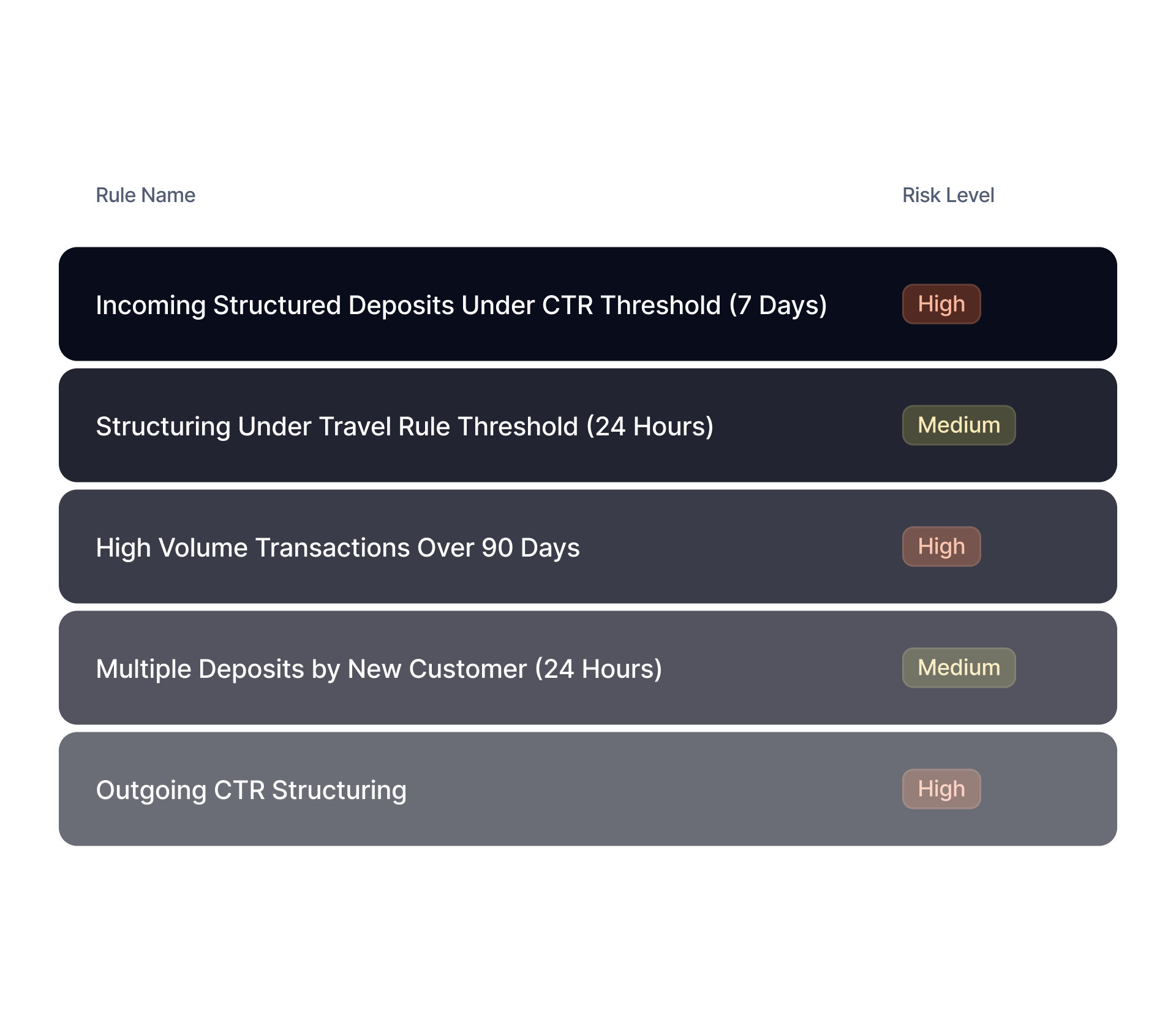
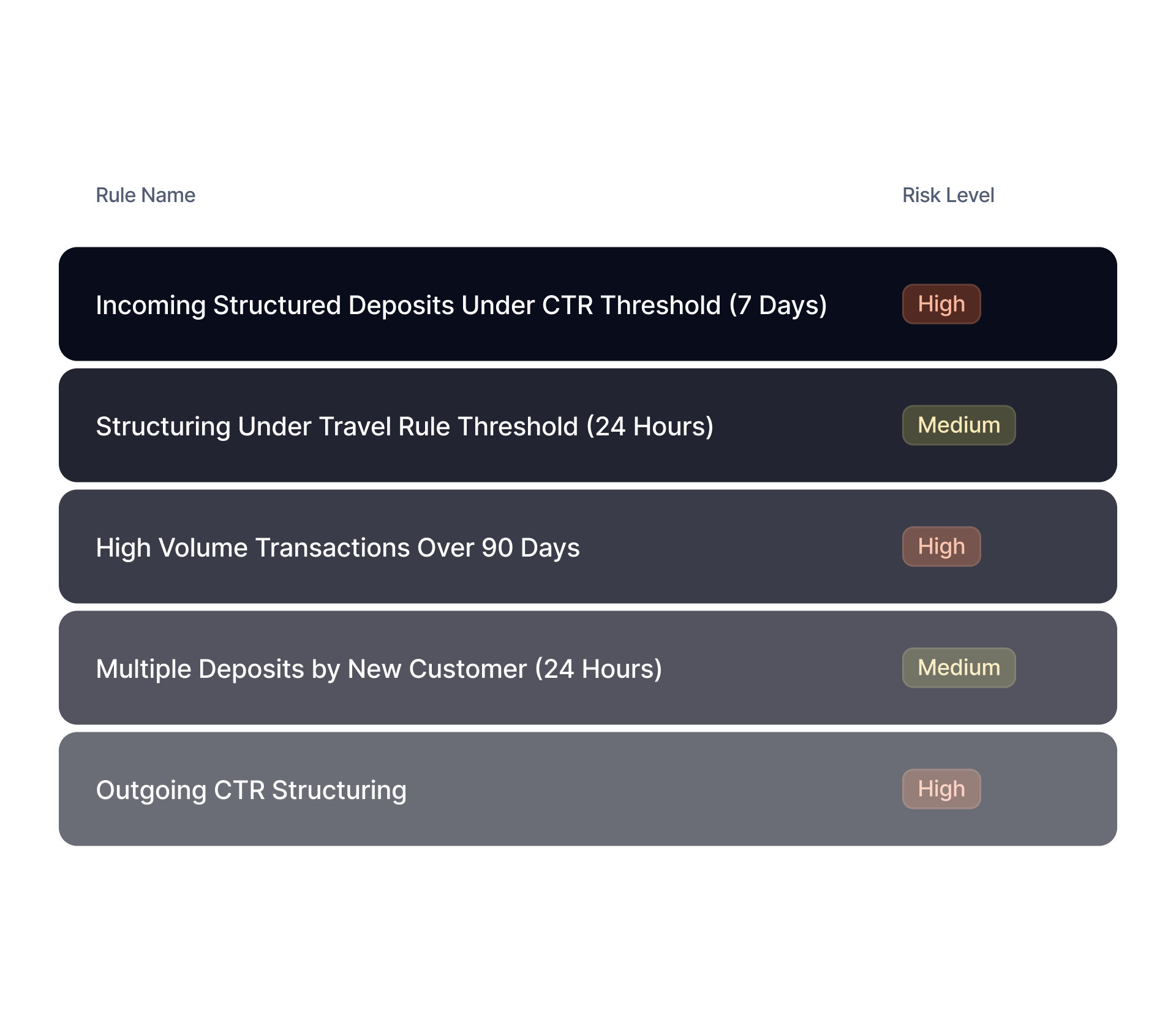
The data consortium platform integrates across Sardine solutions, including:
Incorporate consortium risk signals into AML monitoring logic, configurable thresholds, and alert routing workflows.
Built on the industry's leading agentic risk platform
Device & Behavior
Analyze every customer touchpoint to identify advanced fraud patterns, without adding friction.
Machine Learning
Trained on billions of data points to protect onboarding, login, and payment flows.
Connections Graph
Map relationships between users, devices, IP addresses, phone, email, and transactions.
AI Agents
Automate onboarding reviews, alert handling, investigations, and case management.
Rules & Workflows
Easily create rules, test performance before launch, and deploy updates without engineering
Case Management
Investigate alerts, collaborate with teams, and resolve fraud cases faster.
Frequently asked questions

How can fraud teams identify risky counterparties before a payment is approved?
Fraud teams can identify risky counterparties earlier by evaluating whether the receiving party has shown signs of unusual activity across a broader network, not just within one institution. This includes looking for patterns such as rapid reuse of contact details, links to previously suspicious entities, inconsistent identity attributes, and behavior that suggests account cycling or mule activity. That wider context helps teams decide whether to approve, delay, review, or block a payment before exposure grows.
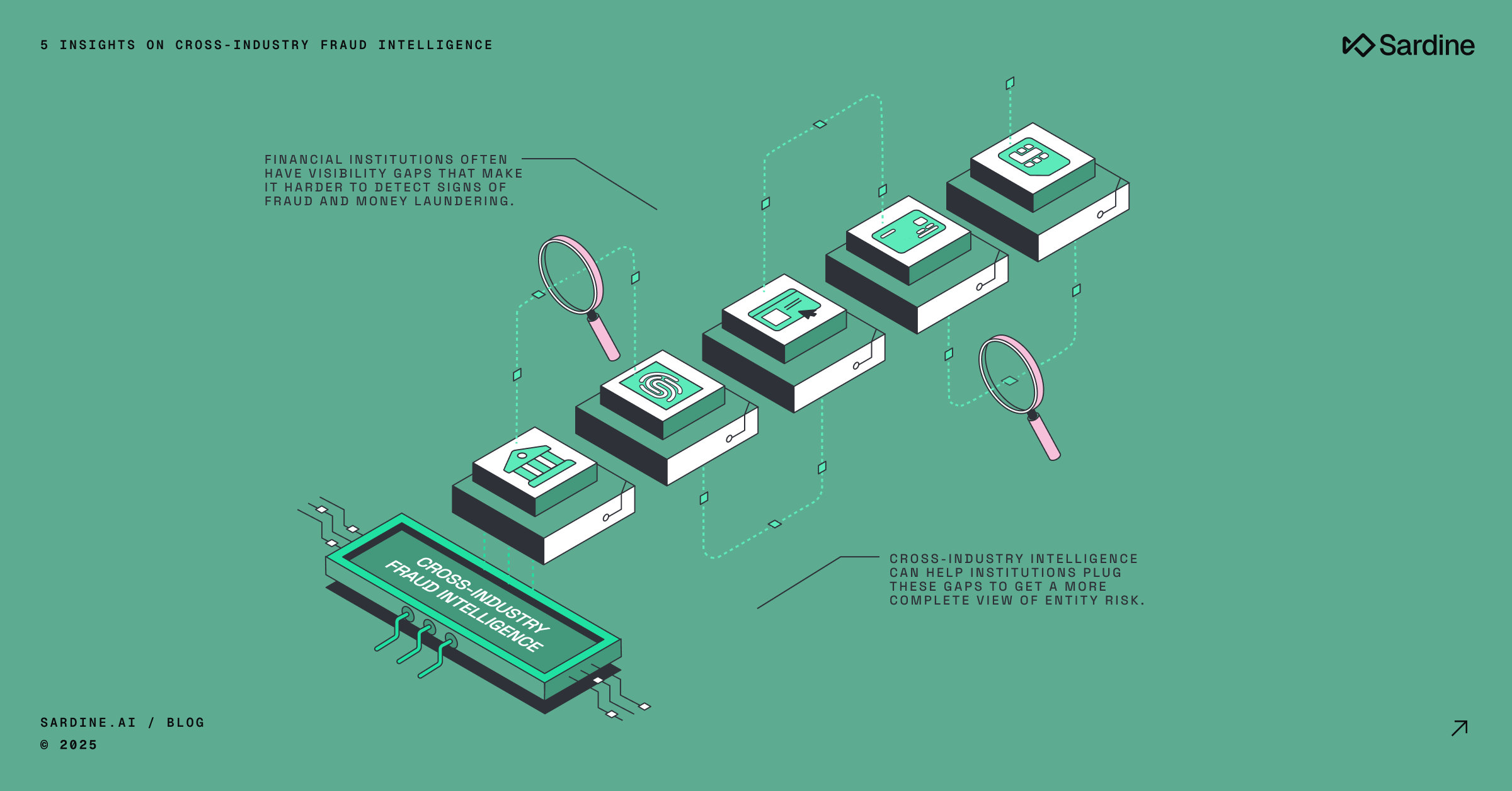
Why do isolated fraud systems miss coordinated financial crime patterns?
Isolated fraud systems usually see only one slice of a bad actor’s activity. When a fraudster spreads activity across multiple institutions, channels, or payment methods, each organization may see only a small piece that looks ordinary on its own. Shared intelligence makes it easier to connect repeated behaviors, reused infrastructure, and linked entities so coordinated abuse becomes visible sooner.
What makes network level fraud intelligence more useful than internal transaction history alone?
Internal transaction history is useful for understanding customer behavior within a single business, but it does not explain how that customer or counterparty behaves elsewhere. Network level intelligence adds external context that can reveal whether a person, device, account, or wallet has a broader pattern of risky activity. That added perspective supports stronger decisions when internal data is limited, especially for new users, new counterparties, and unfamiliar payment routes.
How should institutions evaluate external risk signals without overwhelming analysts?
Institutions should focus on signals that improve decision quality rather than simply increasing alert volume. The best approach is to use structured intelligence that can be routed into existing review logic, case workflows, and escalation.