Bot Detection
Bot Detection
Block bots and malicious AI agents without user friction
Identify human behavior vs. automation across web, mobile, and APIs to protect onboarding, login, checkout, payments, and account changes.
Invisibly protect conversion
Distinguish humans from bots and agents using device and behavior signals, without CAPTCHAs or challenges for legitimate users.
Stop automated abuse
Block credential stuffing, carding, fake accounts, and agentic browser attacks before they reach downstream systems.
Defend the entire customer journey
Protect onboarding, login, account changes, and transactions with one adaptive risk layer across mobile and web experiences.
Stop automated attacks at every critical touchpoint
Login protection
Credential stuffing and account takeover
Stop credential stuffing, AI-driven login automation, and bot-assisted account takeover, even when credentials are valid and infrastructure appears legitimate.
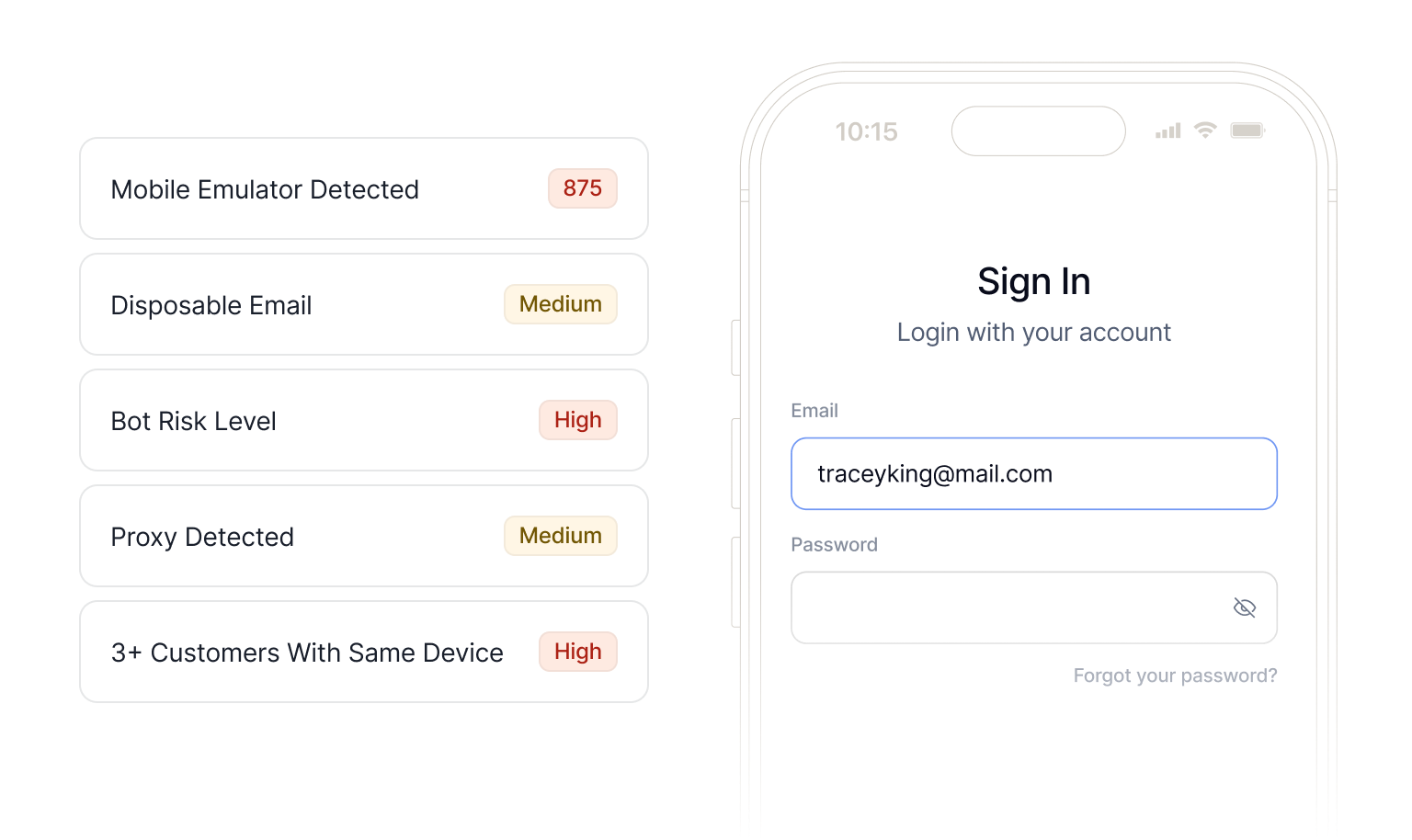
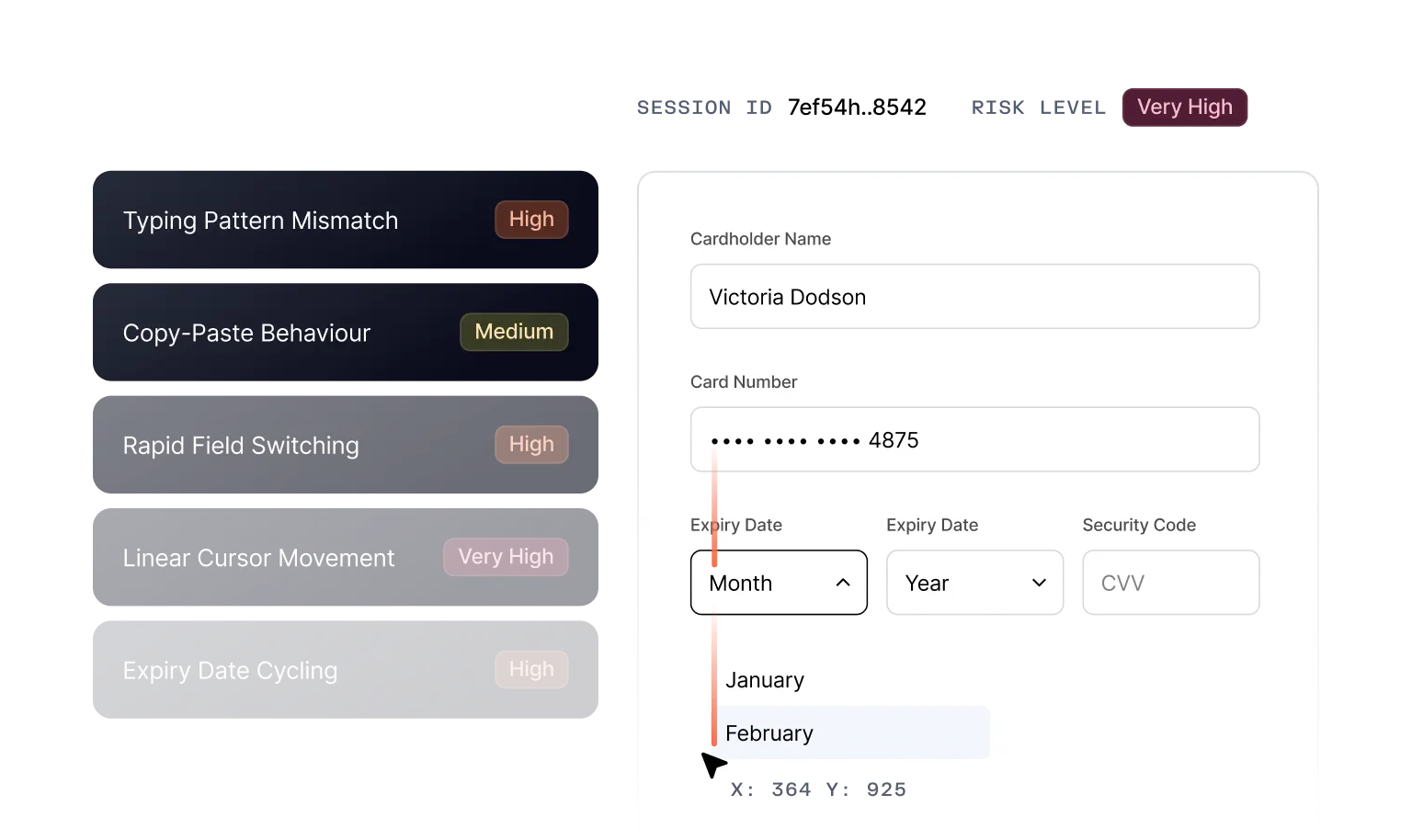
Identify scripted typing cadence, expert mouse movement, and unnatural navigation timing.
Detect Selenium, Playwright, Stagehand, OpenAI Operator, and other automation tools across browsers and frameworks.
Stop automated access attempts before account changes or downstream fraud.
Fake Account Creation
Fake account creation and onboarding abuse
Root out mule networks and scripted account farming at scale.
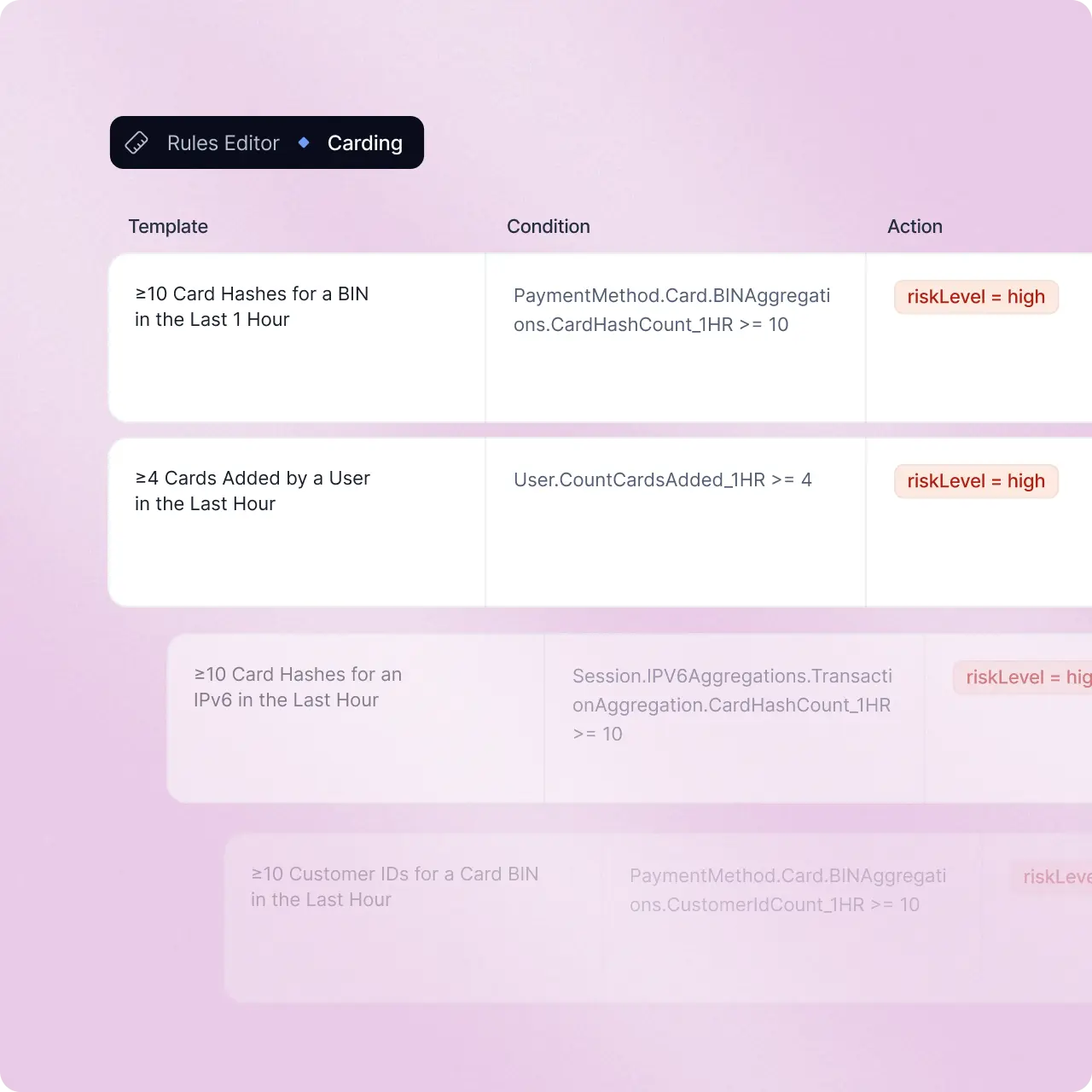
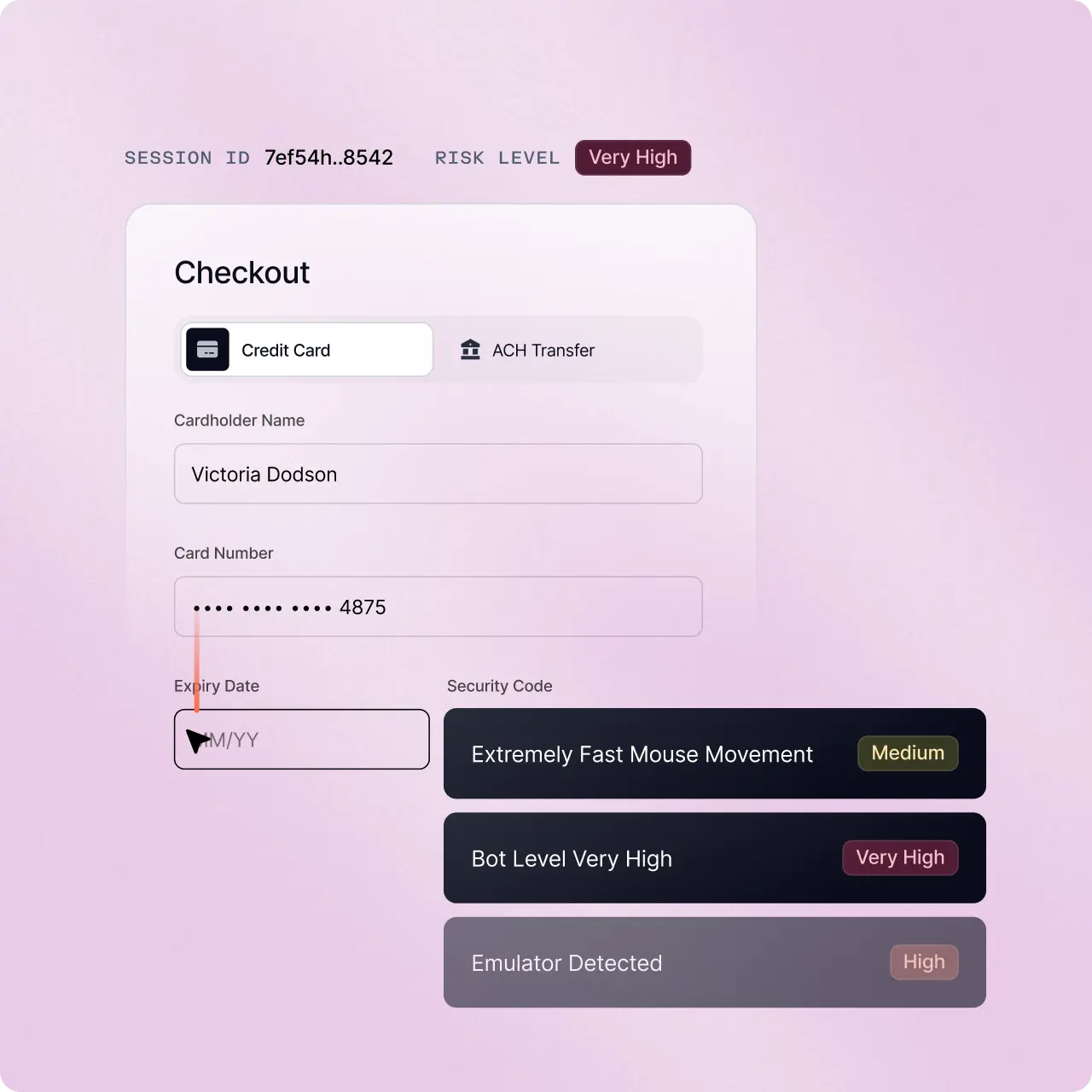
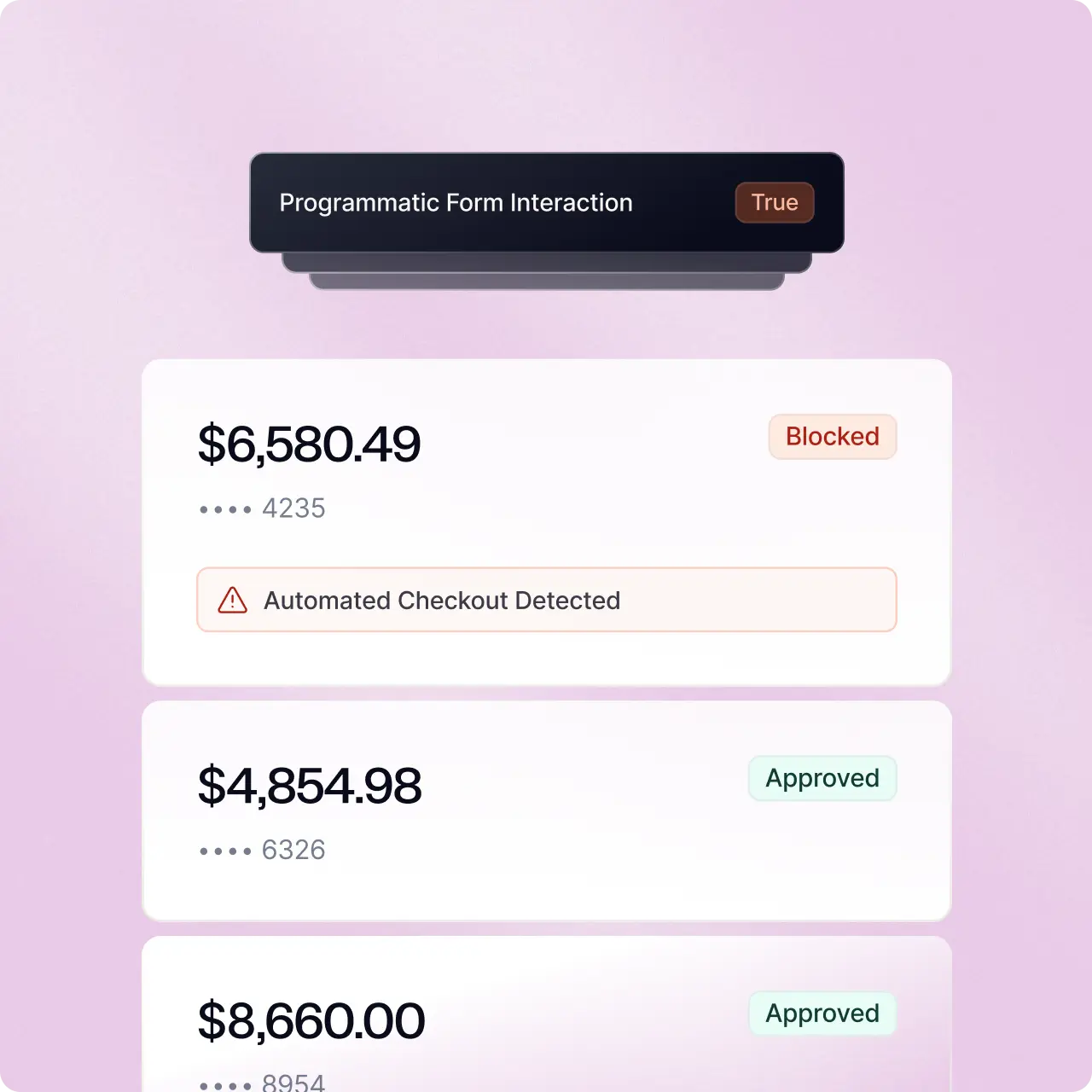
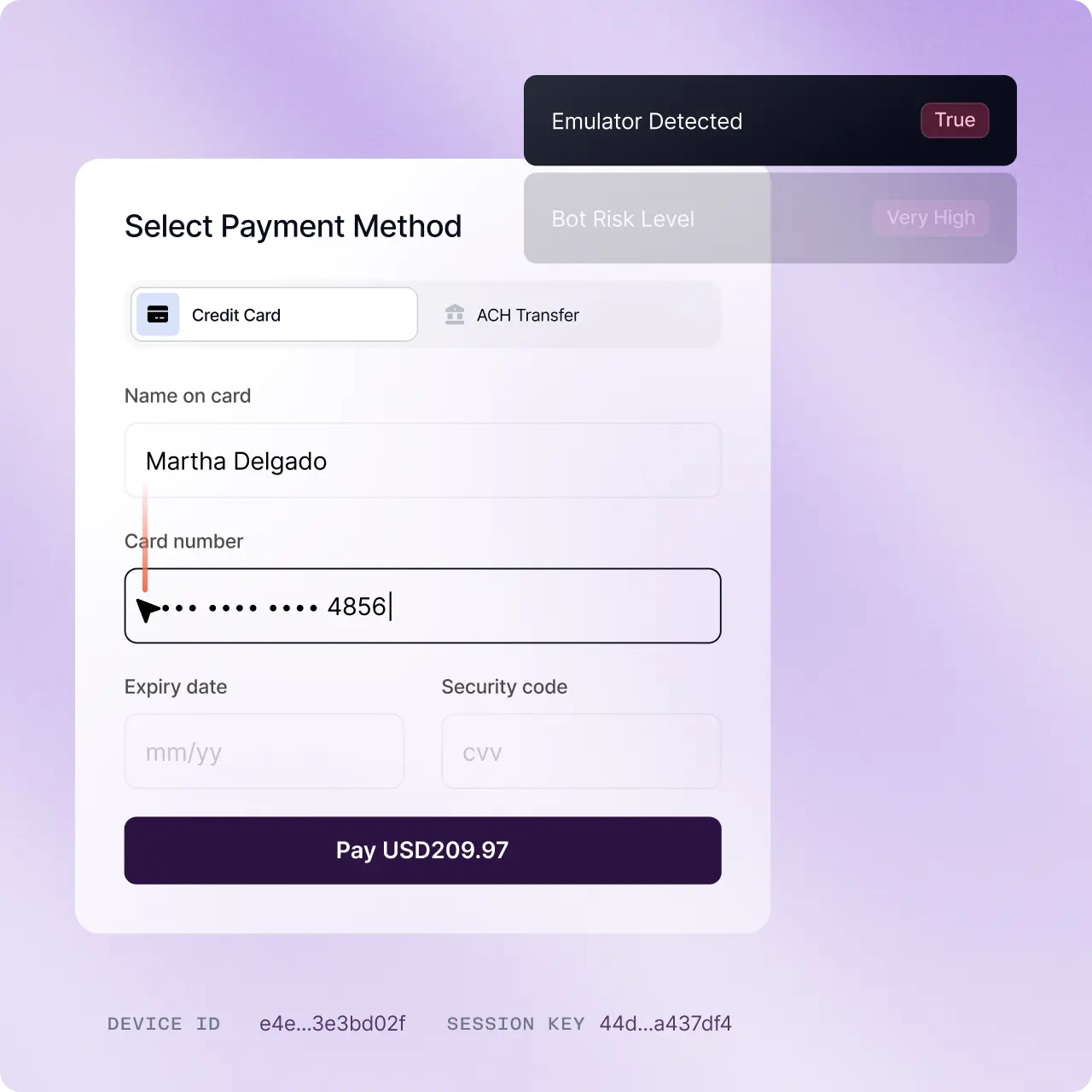
Carding Attacks
Carding and checkout automation
Stop payment page bots before authorization and processor impact.
Automated Activity
Bot-assisted ATO and social engineering
Detect malware-driven sessions and remote access manipulation.
Detect RATs, accessibility abuse, and malicious session control.
Surface abnormal device posture, overlays, and suspicious signals.
Escalate sessions before password resets, payouts, or profile modifications.
Agents that continuously adapt your defense
Spot complex fraud patterns earlier, reduce investigation time, and give teams clearer signals for faster, more accurate decisions.
Detect AI-driven browsers and automation frameworks
Identify agentic tooling, non-human typing, navigation patterns, and anomalous device posture.
Accurately spot AI traffic
Distinguish between trusted agents and malicious automated traffic.
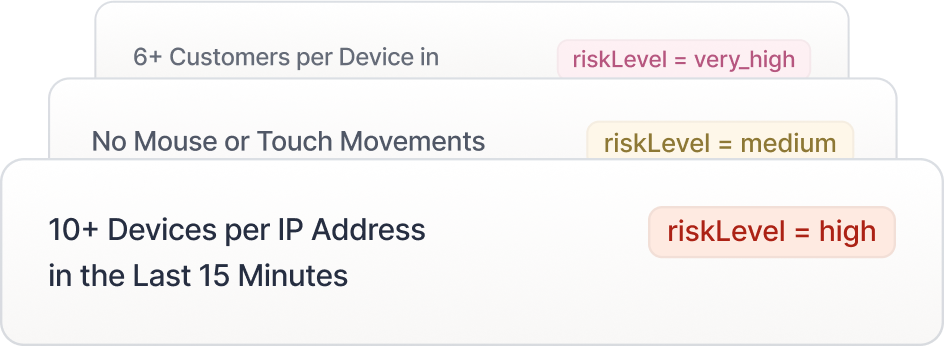
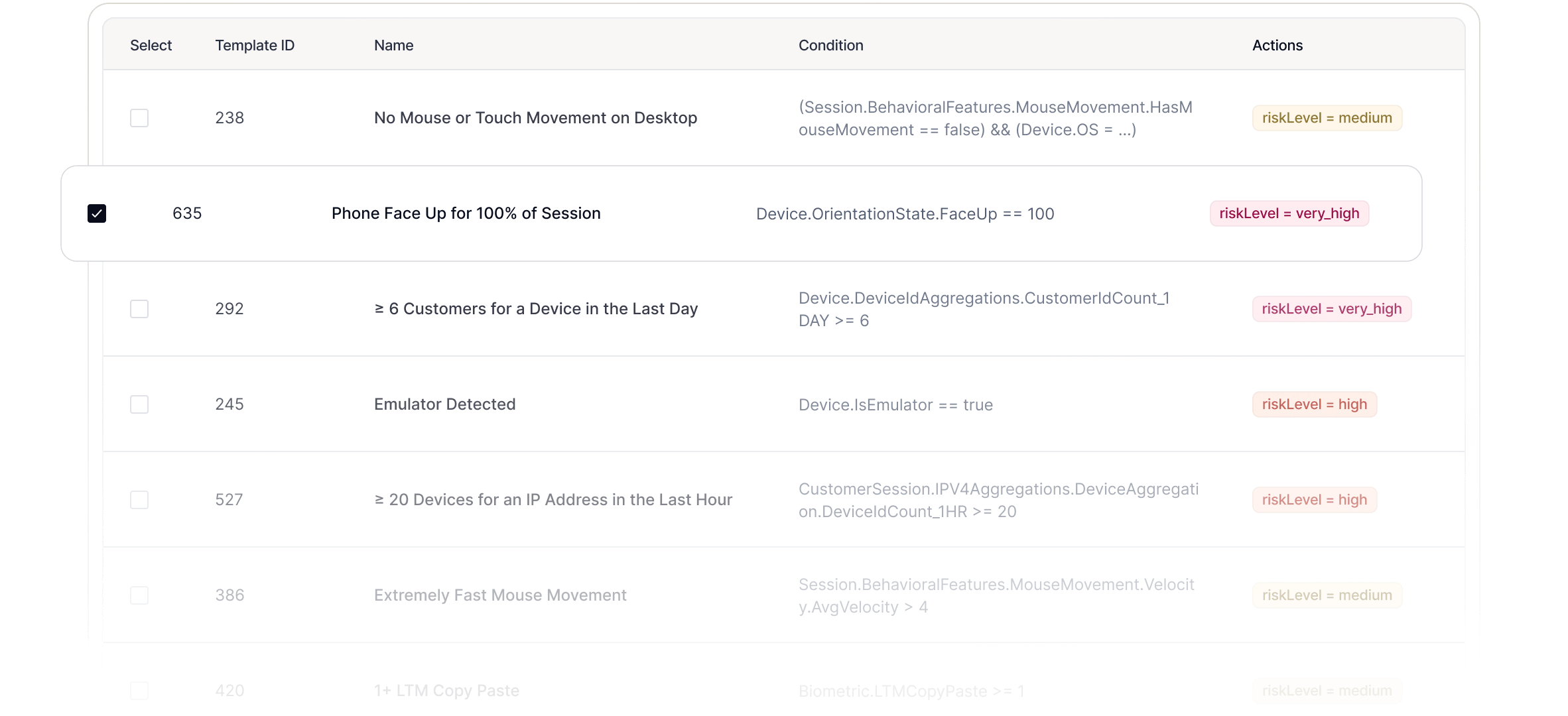
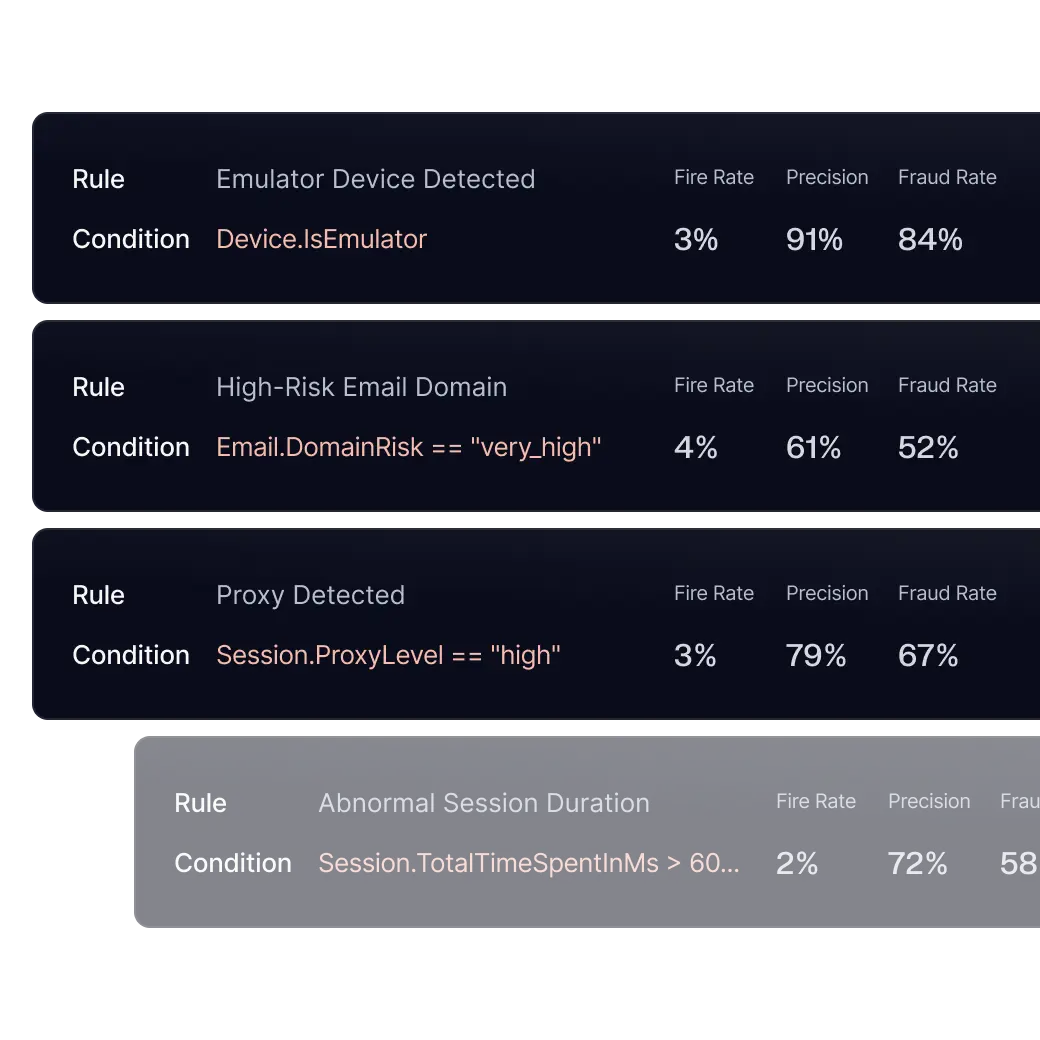
Adapt automatically with anomaly-driven detection
Continuously monitor traffic patterns and surface emerging automation behaviors before campaigns scale.
Detect automation without slowing legitimate users
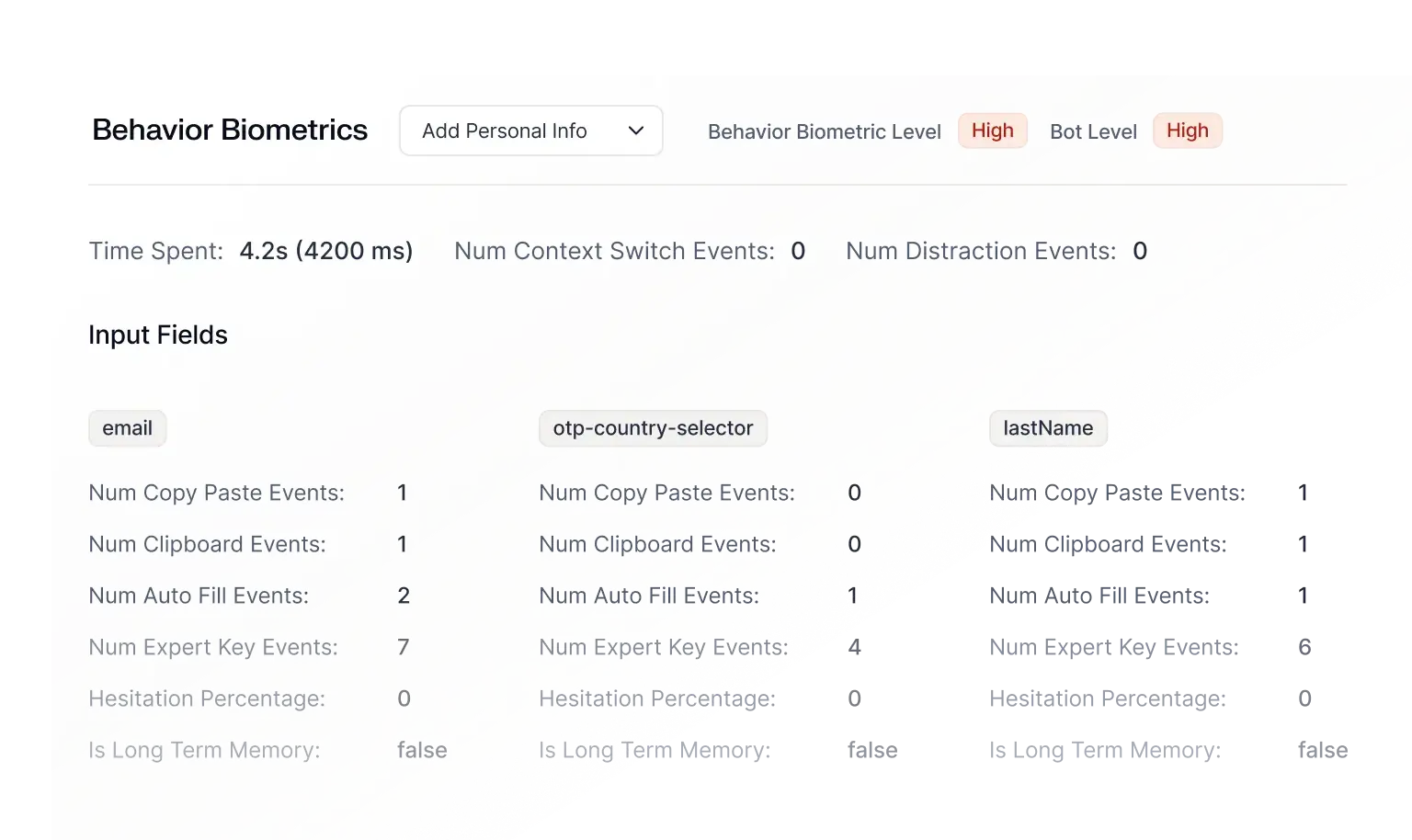
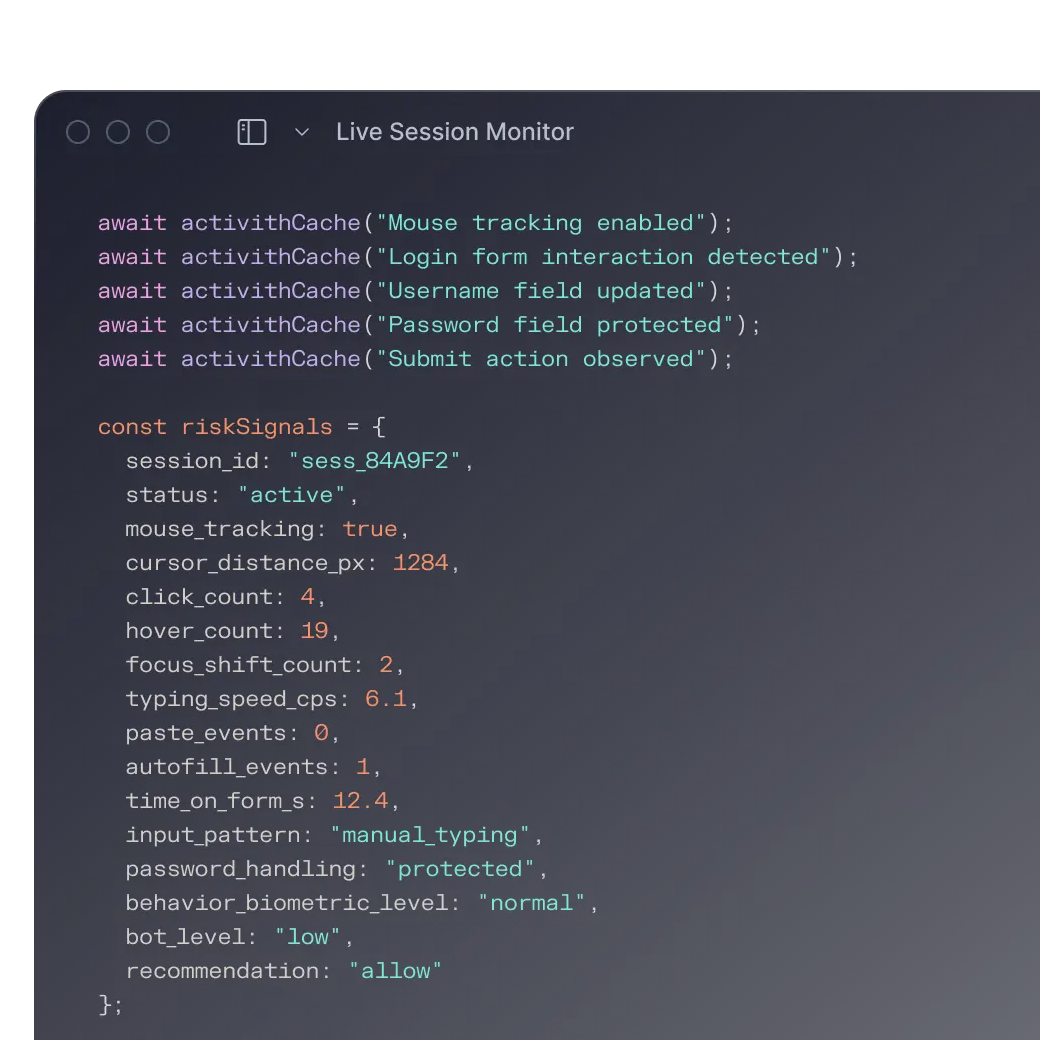
Device & Behavior
Session-level intelligence across every digital touchpoint
Proprietary fingerprinting and behavioral biometrics analyze thousands of device, sensor, and behavioral telemetry signals in milliseconds to detect automation across every digital session.
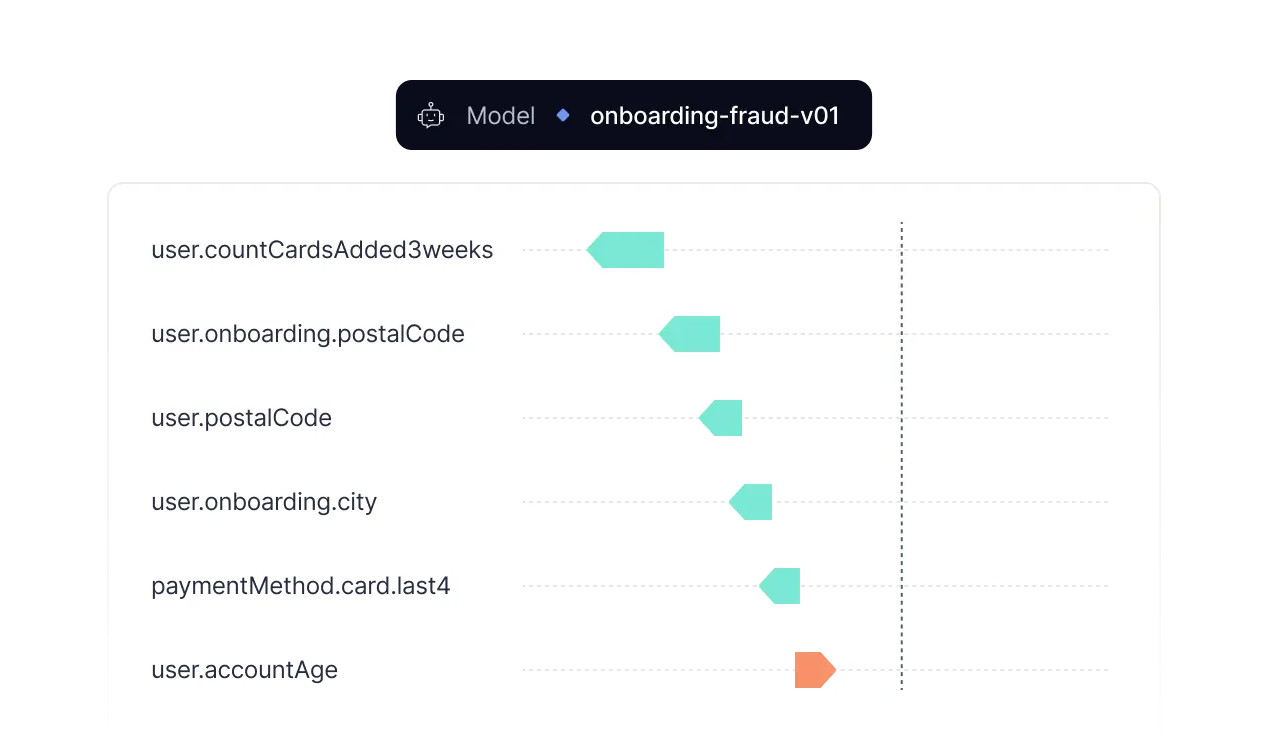
Machine Learning
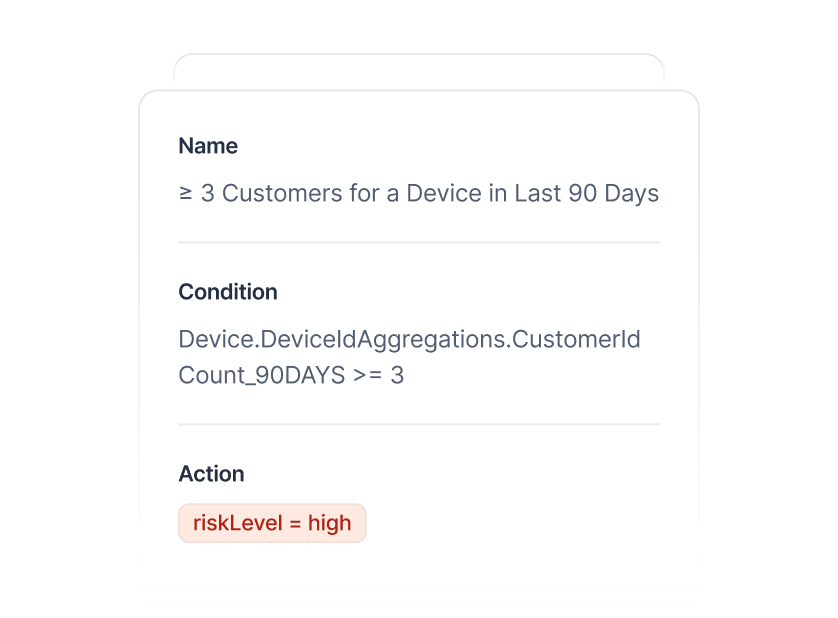
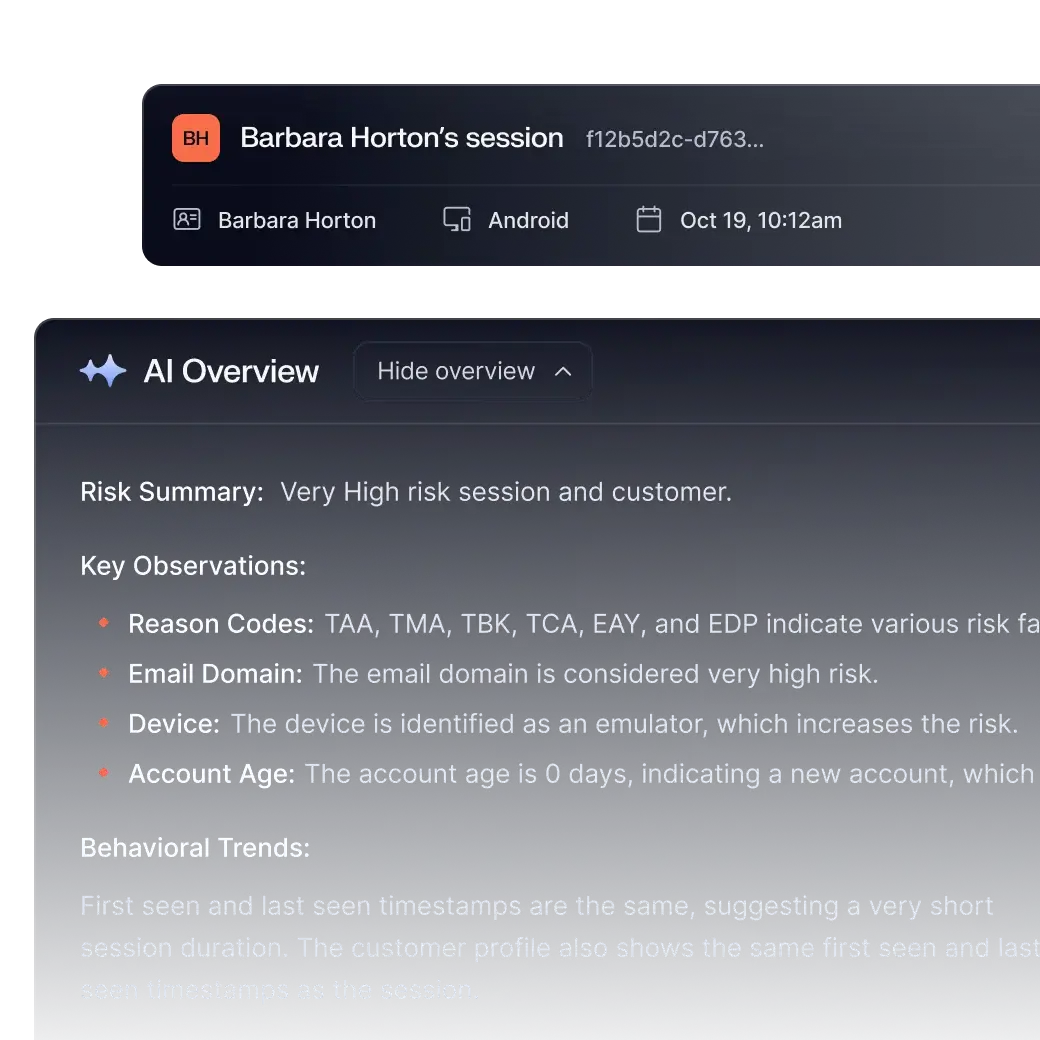
Surface emerging automation techniques
Analyze behavioral, device, and network signals in real-time, using anomaly-driven models to surface new patterns and recommend updated controls before large-scale campaigns take hold.
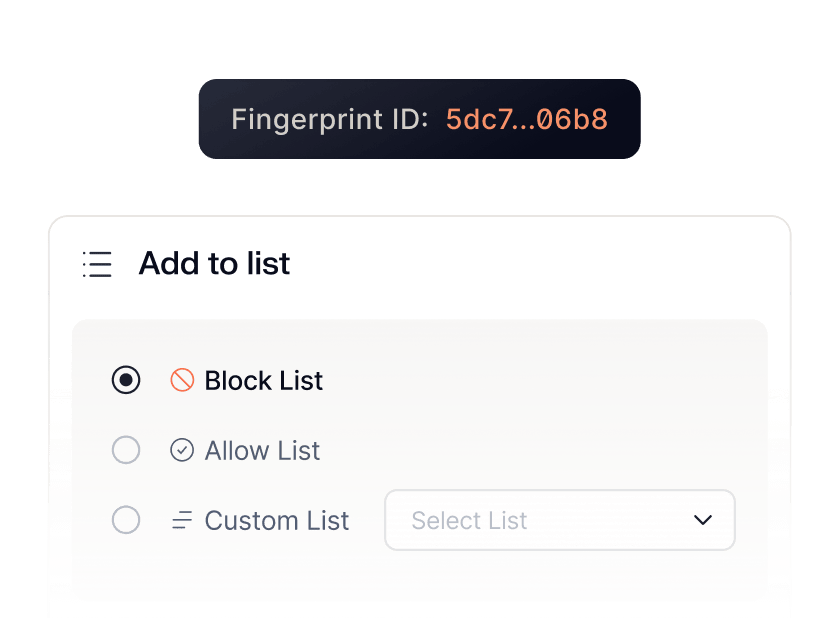
Fraud Investigations
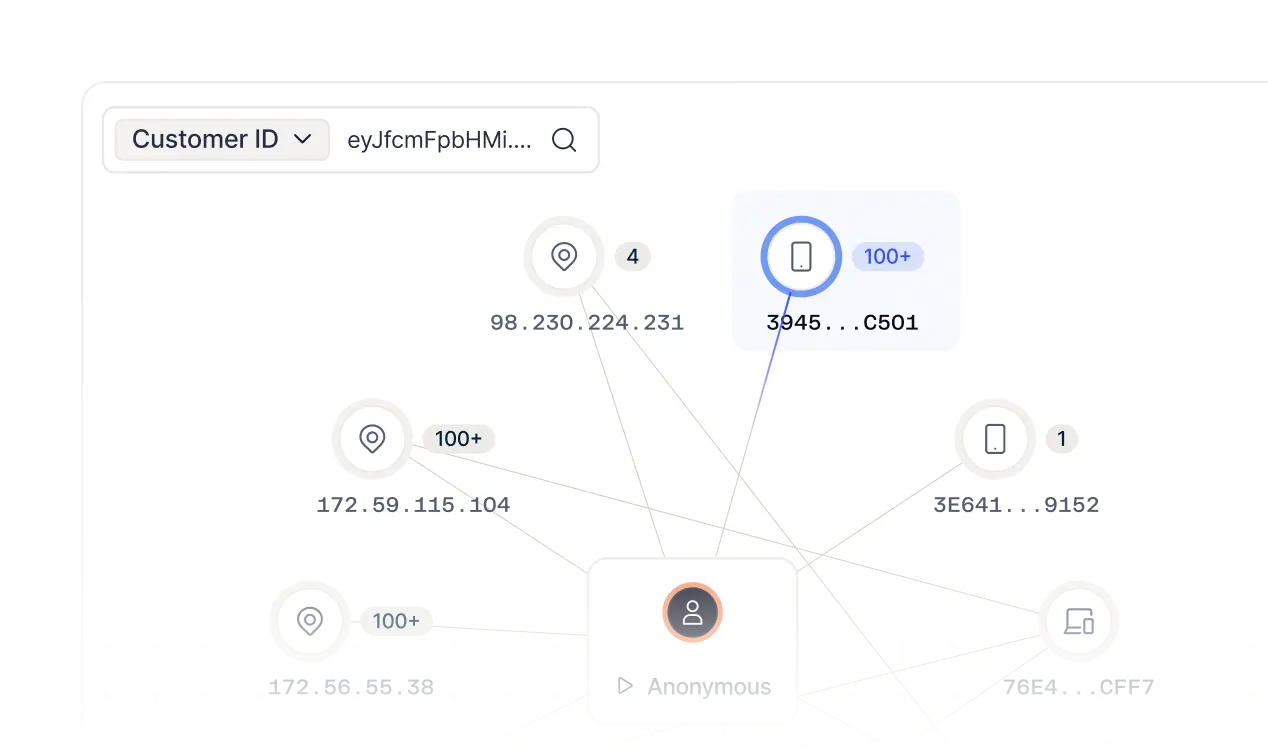
Reveal coordinated bot campaigns
Unify true IP signals, devices, fingerprints, behavioral signatures, and fraud outcomes in a single graph to expose shared infrastructure, automation reuse, and coordinated bot campaigns.
Block bots and malicious AI agents without user friction
Frequently
asked questions

How does Sardine detect advanced automation like AI browser agents or Stagehand-type tooling?
Sardine does not rely on static bot signatures. Instead, it analyzes full-session telemetry, including device fingerprint integrity, browser instrumentation artifacts, sensor data consistency, timing distributions, and behavioral entropy. AI browser automation frameworks such as headless Chromium, Selenium, Playwright, and emerging LLM-driven agents leave detectable inconsistencies in navigation cadence, DOM interaction patterns, and environment signals. Sardine correlates these low-level indicators in milliseconds to distinguish tool-driven sessions from genuine human variability, even when credentials are valid and infrastructure appears residential.
How does Sardine detect emulator farms, cloned apps, and remote access tooling?
On mobile and web, Sardine evaluates device posture and runtime integrity in real time. This includes emulator detection, virtual machine indicators, app cloning artifacts (parallel spaces), rooted or jailbroken environments, sensor mismatches (orientation, motion, tap pressure), VPN/proxy piercing, and remote access tool overlays. By combining environment signals with session behavior, Sardine differentiates legitimate edge cases from coordinated automation or device farm activity, preventing large-scale scripted abuse at onboarding, login, and checkout.
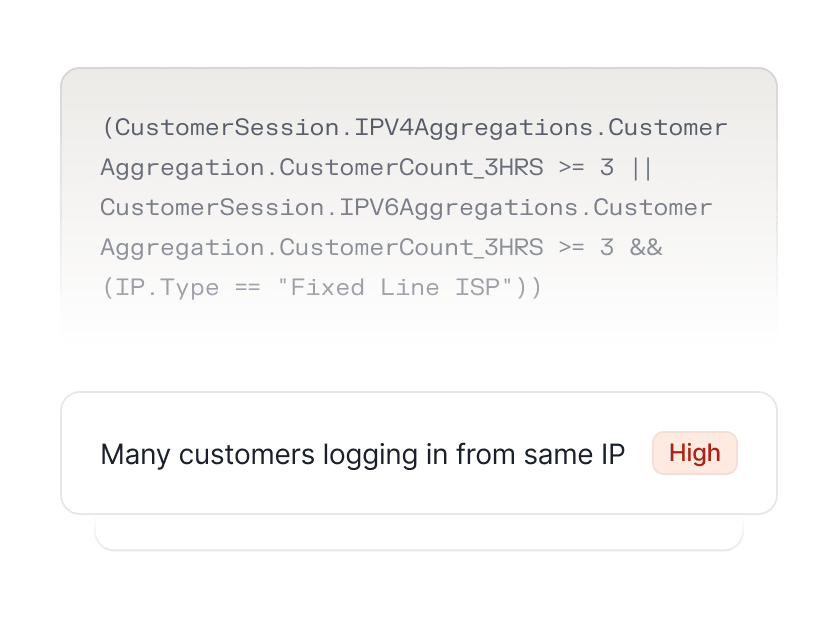
How does Sardine move beyond IP blocking to stop full bot campaigns?
Rather than treating each session in isolation, Sardine links devices, fingerprints, infrastructure, behavioral signatures, and fraud outcomes in a graph layer. This surfaces infrastructure reuse, automation pattern repetition, shared payment testing strategies, and cross-account coordination. Operators can enforce controls at the cluster level, blocking bot rings, device farms, or AI-driven campaigns in bulk, instead of reacting to rotating IP addresses or single accounts. This shifts bot defense from reactive filtering to systemic campaign disruption.
How does Sardine balance enforcement with conversion optimization?
Sardine continuously scores sessions using passive behavioral and device intelligence without introducing visible challenges by default. Enforcement actions can be tiered, from silent rate limiting, invisible honeypots, and API throttling to step-up authentication only when risk materially increases. Because decisions are made at session speed and tied directly to fraud outcomes, teams can reduce credential stuffing, card testing, and fake account creation while minimizing friction for legitimate users. Controls are measurable, testable, and adjustable in real time.
Can Sardine distinguish between human-assisted fraud and fully automated bots?
Yes. Sardine models not just binary human-versus-bot signals, but the spectrum between them. For example, malware-assisted sessions, remote-access-tool overlays, or socially engineered users being coached in real time exhibit behavioral irregularities that differ from both organic users and scripted automation. By analyzing hesitation patterns, navigation flow, environment integrity, and device control signals together, Sardine flags hybrid abuse scenarios before high-risk actions like credential changes, payout updates, or payments are executed.


