Candidate Fraud
Candidate Fraud
Stop fake job applicants across the hiring lifecycle
Prevent fraudulent candidates from submitting fake job applications and using deepfakes during interviews
Detect fraudulent applicants early
Identify when applicants use stolen or synthetic identities, throwaway phone numbers or emails, or deepfakes.
Integrates directly into your ATS
Ensure the person interviewing is the same one who applied, across devices, sessions, and locations.
Reduce enterprise security risk
Prevent fraudulent hires from accessing systems, data, and workflows without slowing legitimate candidates.
Stop fraudulent job applicants before they get through screening and interviews
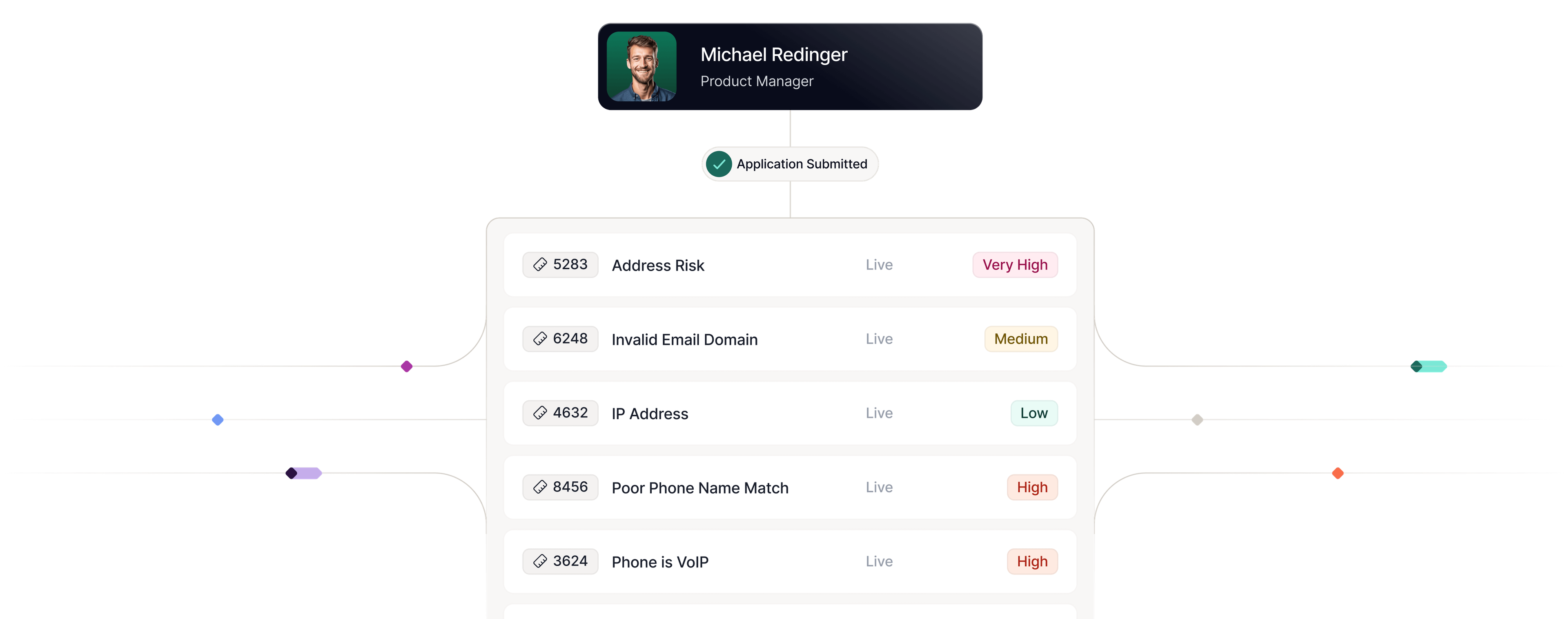
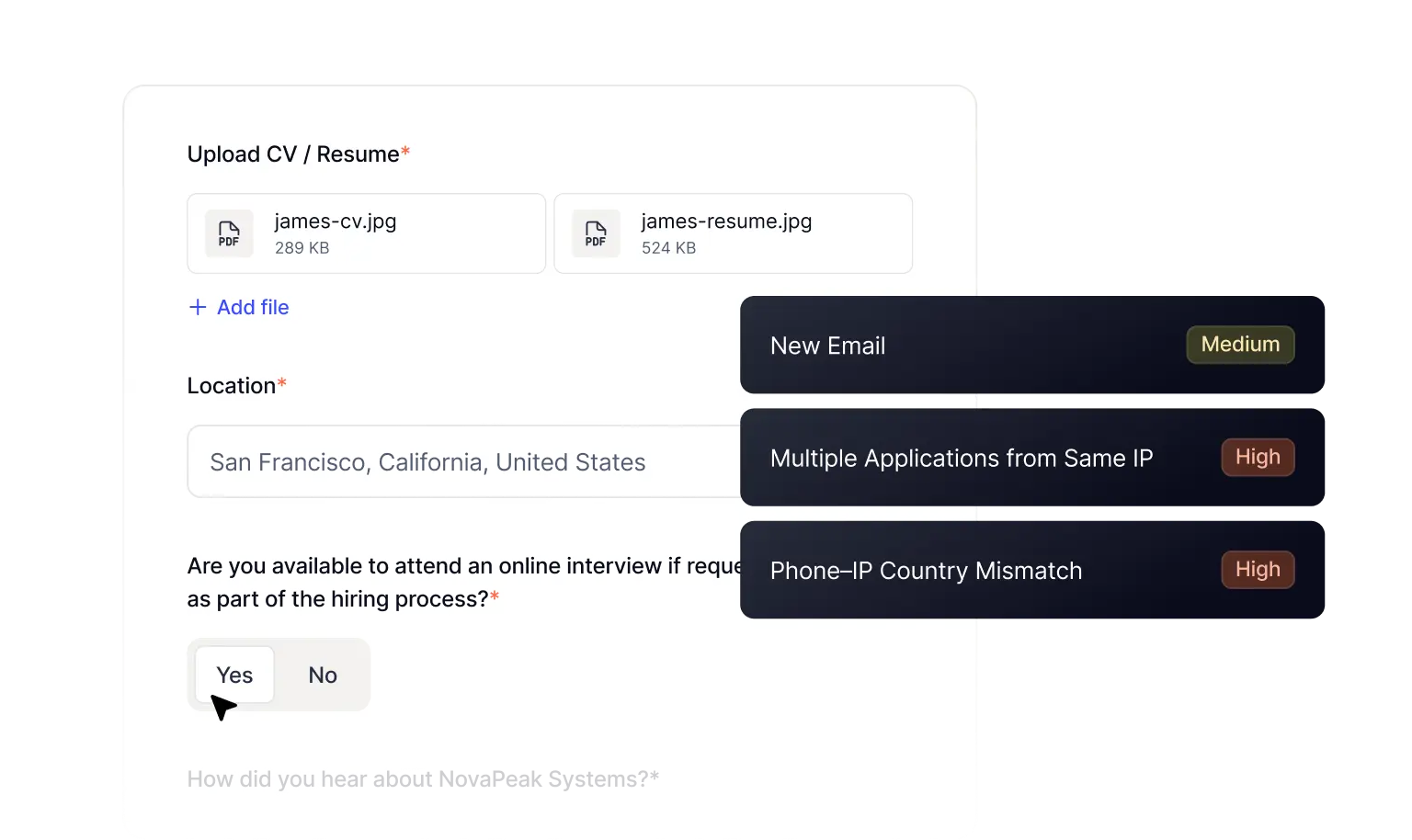
Identity Fraud
Applications with synthetic identities
Weed out fake identities in your applicant pool.
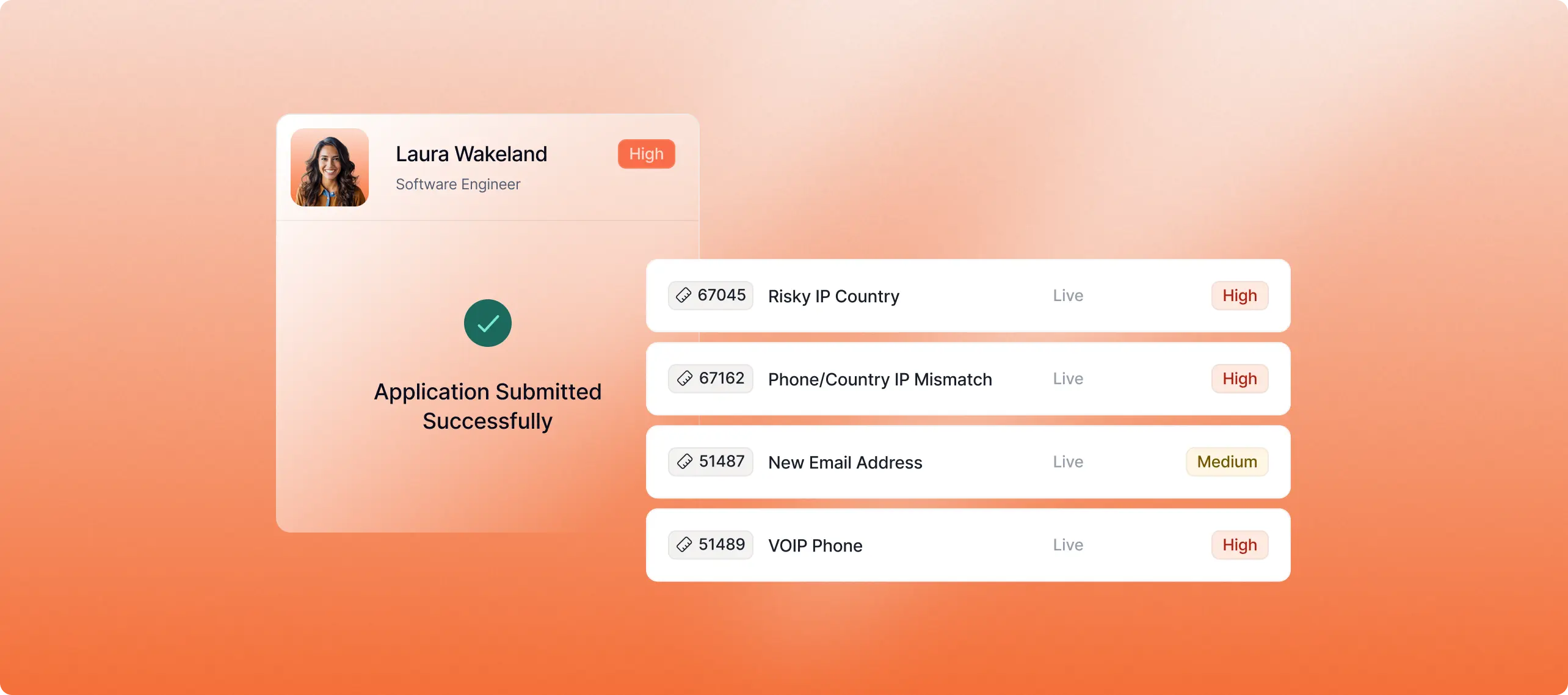
Flag throwaway emails, VoIP phones, and identity mismatches before recruiters review applications.
Identify when devices, identity, or contact information is reused across multiple applications.
Score applicants as low, medium, or high risk with explainable signals recruiters can trust.
AI-Generated Resumes
Fake resumes and application farms
Block automated, AI-written applications before they overwhelm recruiters and applicant tracking systems.
Flag automation, scripted inputs, and behavior inconsistent with genuine human form completion.
Surface unusually fast submissions, copy-paste behavior, and repetitive resume structures.
Link identities, devices, and networks to uncover organized application farms.


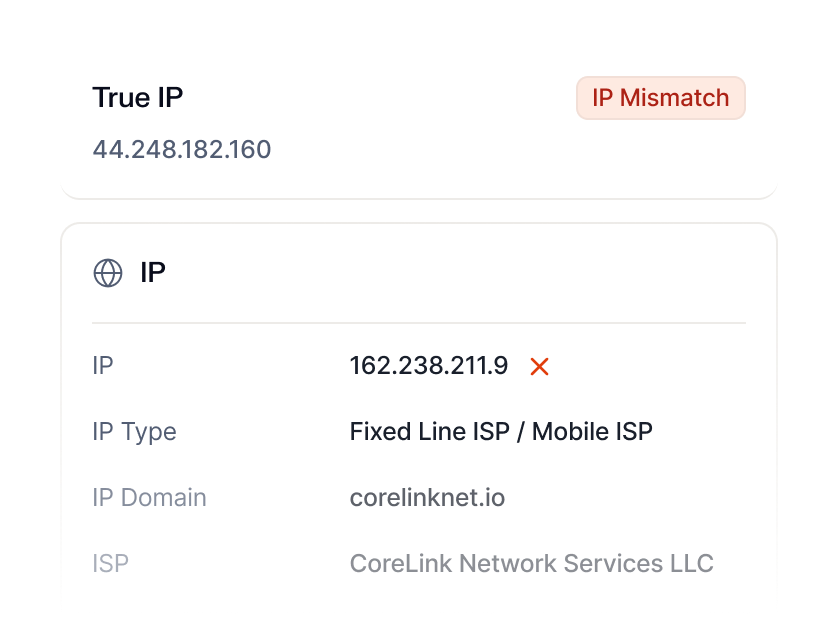
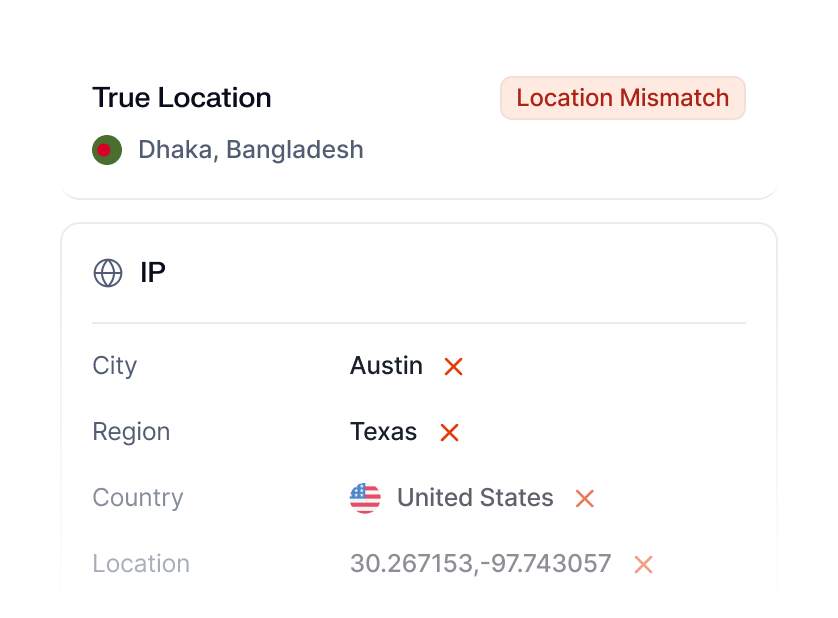
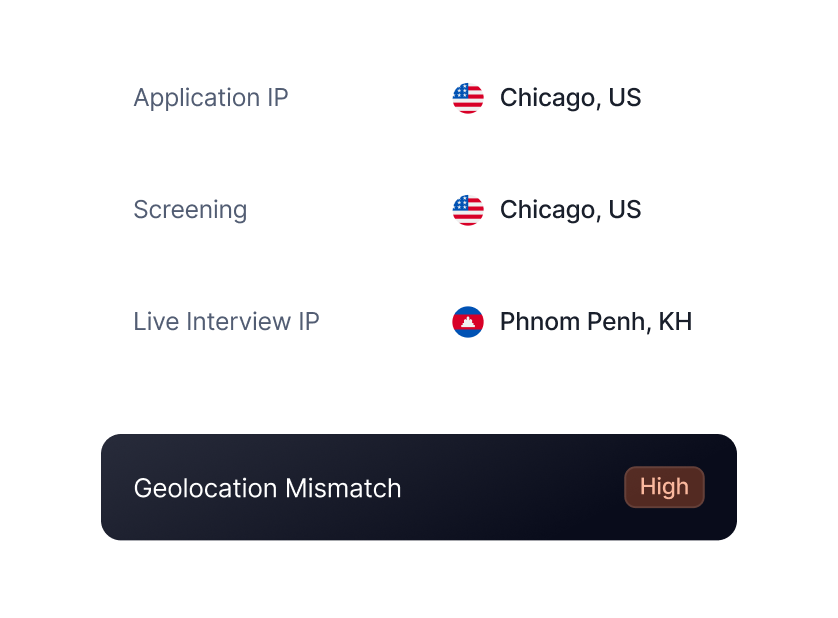
Location Spoofing
Candidates that use a fake or incorrect location in applications
Deepfake Impersonation
Interview impersonation and deepfake fraud
Protect hiring integrity without disrupting legitimate candidates.
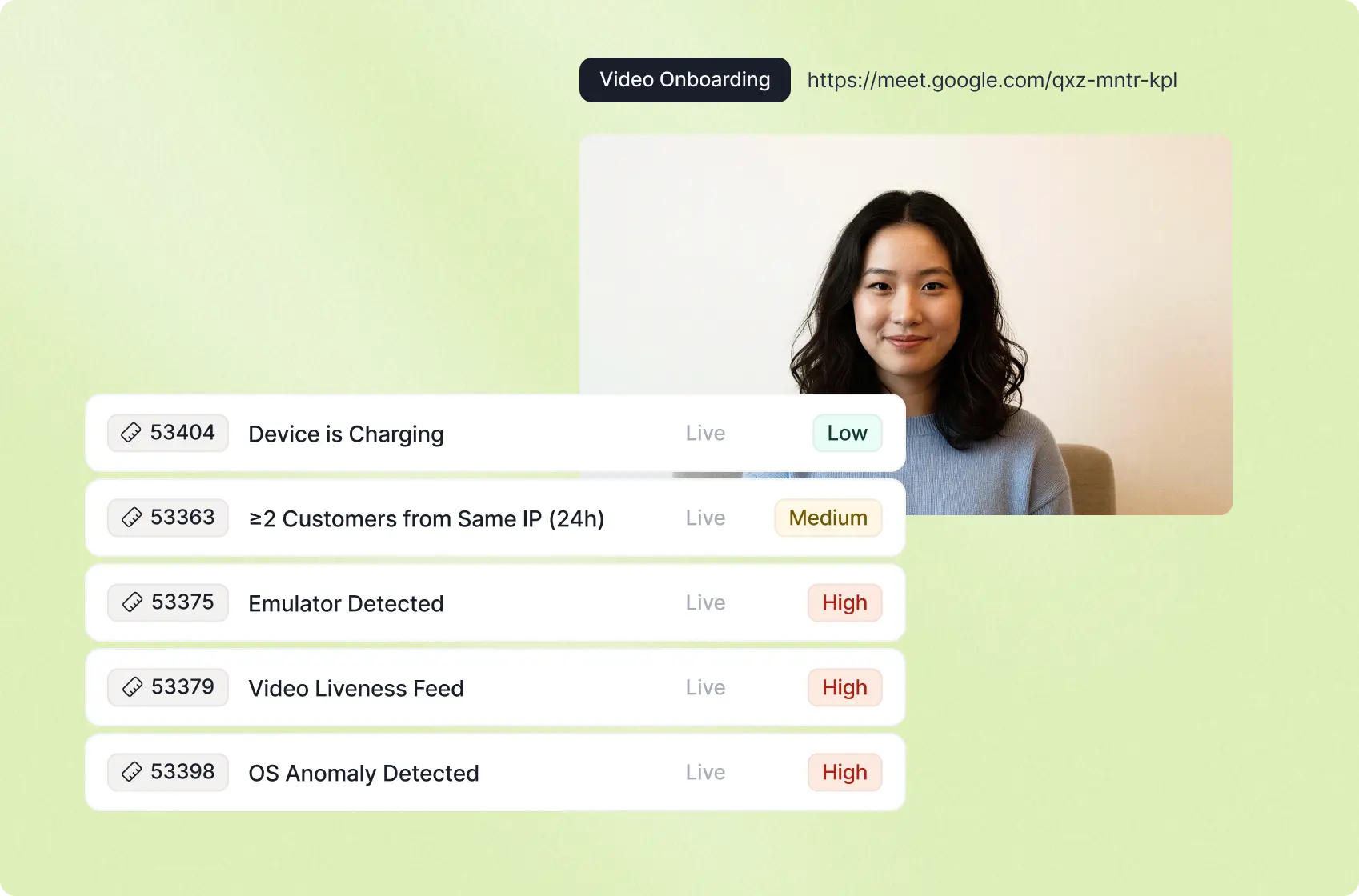
Identify injected video feeds, virtual cameras, and manipulated interview environments.
Flag emulated devices, headless browsers, and screen sharing software used for deception.
Detect automated, scripted interactions and unusual multitasking that suggests assistance or impersonation.
Stop fake applicants and protect your workforce
Frequently
asked questions

How is this different from traditional background checks or HR screening tools?
Traditional screening focuses on applicant fit and employment verification. Candidate fraud detection focuses on identifying deception in applications and interviews, including impersonation, synthetic identities, AI generated resumes, and manipulated sessions before a fraudulent hire gains access.
Will this slow down legitimate candidates or create extra friction?
No. Detection is passive and runs in the background without requiring challenges, uploads, or workflow changes. Low risk applicants move through normally, while higher risk signals are flagged for review with clear explanations.
Will this create bias or unfairly screen out qualified candidates?
No. Sardine does not evaluate resume content, background, or personal characteristics. Risk signals are tied to fraud indicators such as device reuse, automation behavior, impersonation, and location inconsistencies, not who a candidate is or where they are from.
How does Sardine detect interview impersonation or deepfakes candidates?
Interview sessions are validated by analyzing device fingerprints, behavioral signals, location consistency, virtual cameras, emulators, and remote access tooling to confirm the person being interviewed matches the original applicant.
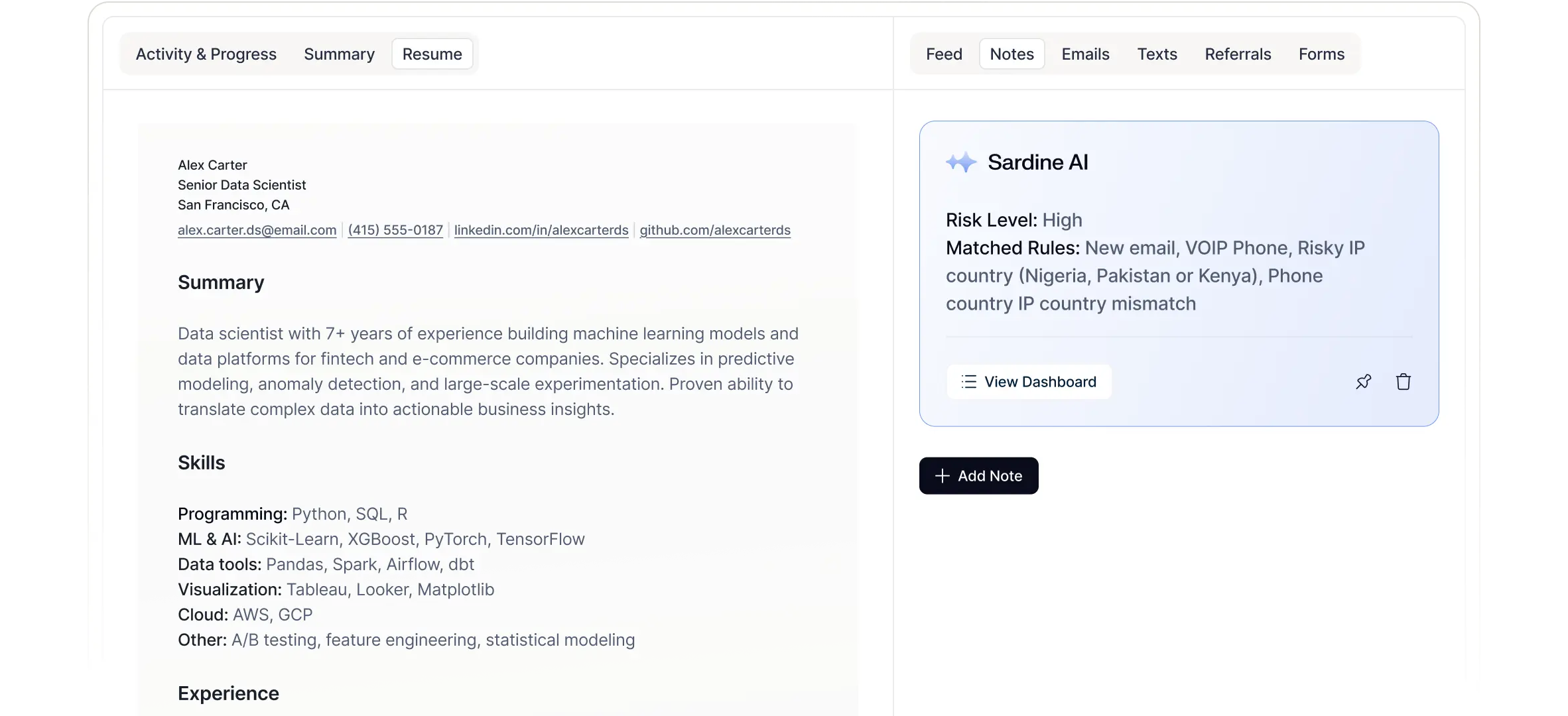
Can we see why an applicant was flagged as risky?
Yes. Every decision includes matched rules, contributing signals, and a clear low, medium, or high risk assessment, giving HR, Security, and Compliance teams defensible context for action and documentation.
How does this integrate with our existing ATS and hiring stack?
Integration is handled through webhooks or hosted application forms that deliver risk signals directly into ATS and recruiter workflows. No rip and replace is required, and controls can be configured without engineering support.
How does Sardine detect AI-generated resumes and automated job applications?
The platform analyzes behavioral biometrics, submission patterns, interaction timing, and repeated infrastructure signals to identify scripted inputs and coordinated application abuse early in the hiring process.
How does Sardine identify location spoofing during remote hiring?
Claimed candidate location is compared against IP intelligence, device telemetry, and session history to surface inconsistencies that may indicate VPN masking, proxy infrastructure, or cross-border discrepancies during screening and interviews.


