The industrialization of fraud: How operations have matured and where they’re going next
Fraudsters aren't running attacks anymore. They're running operations.
For years, fraud teams built their defenses around a familiar model: catch the bad transaction, flag the suspicious account, investigate the alert. This approach relied on the assumption that fraud occurred as a discrete event at a single point in time, easily identified by searching for well-known anomalies.
That assumption no longer holds.
What we saw across 2025 revealed a fundamental shift in how fraud operates. Gone are the days of a single bad actor trying their luck. Modern attacks involve continuous, coordinated operations that frequently appear legitimate while they are happening. Here's the part that should keep fraud leaders up at night: when identity checks pass and transactions make sense, the behavior remains invisible until the money is gone.
AI now enables adaptive fraud workflows
The biggest accelerant? AI-powered fraud workflows that learn and adapt in real-time.
Consider what Matt Vega, Chief Fraud Strategist at Sardine, described during our Fraud and AML Trends webinar about this velocity recently. Sardine recently spoke to a company that was attacked using Google reCAPTCHA v3, the frictionless bot-detection layer which relies on confidence thresholds to block sessions. When the company lowered its blocking threshold to stop the attack, the AI agents behind it responded instantly.
[Callout quote] [7:27 - 8:30]
“The agent attack would completely pivot in real-time…it would drop their score to get around that new threshold. Then they [the company] would drop it again and it would pivot within 400 to 500 milliseconds…the speed and velocity is just brutal.”
— Matt Vega, Chief Fraud Strategist, Sardine
These polymorphic attacks represent a brand new category of threat as they shape shift based on the defenses they encounter. This capability is happening now and is no longer just some theoretical risk.
The barrier to entry has collapsed. What used to require deep cybersecurity expertise, such as man-in-the-middle attacks, credential stuffing, or OTP interception, can now be assembled and launched in under five minutes by someone with no technical background. Fraud-as-a-service packages are sold on dark web marketplaces for as little as $150, often bundled with specific institutional targets. As Chen Zamir, Sardine's Head of Fraud Strategy, put it:
[Callout quote] [10:16 - 11:10]
“Buyers don't need to have technical knowledge, they just need a Tor VPN.”
Scams are the new dominant vector
Scams surpassed traditional fraud in both volume and losses in 2025, largely due to how effectively they scale with AI. Better scripts, deepfake-powered KYC bypass, and precision victim targeting have made scam operations faster, more convincing, and harder to distinguish from legitimate activity.
The impact of scams extends well beyond the initial victim because every successful operation creates a money laundering problem. As the proceeds move, we are seeing the rise of AI orchestrated “dusting.”
[Callout quote] [32:58 - 33:41]
“You could see these money laundering networks where you have one originating account and one exit account, but in the middle there can be dozens, maybe even hundreds of accounts that route the money, sometimes even just pennies. This obviously slows down fraud-fighting teams.”
— Chen Zamir, Head of Fraud Strategy, Sardine
Chen noted that while money laundering networks once required significant human labor, AI agents now automate the process. These intermediary accounts route tiny increments to obscure the trail. This layering has also become a cross platform challenge where fraudsters exit through different organizations entirely, making settlement reconciliation exponentially harder.
The old model is broken
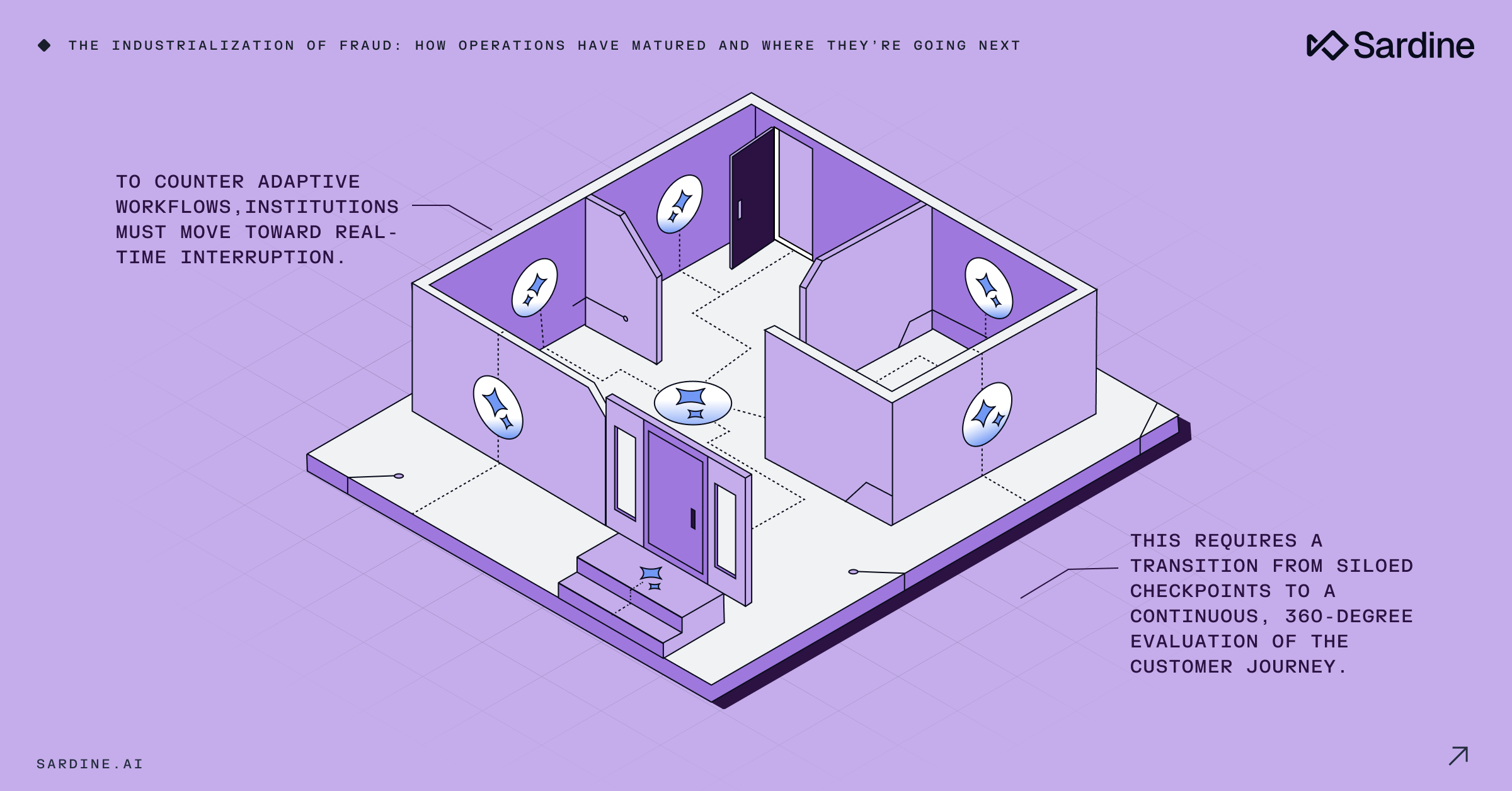
The traditional fraud prevention approach simply can't keep up. The common approach involves heavy controls at account creation and again at checkout, yet it leaves a significant visibility gap between those two points.
Matt Vega argues that this “perimeter” focus fails to account for how modern attackers actually move.
[callout quote] [15:33 - 16:17]
“You put a bunch of security cameras at your front door, which is account creation, and a bunch of security cameras at your back door, which is checkout. The problem is, once fraudsters get into your house, you don’t know what drawers they’re accessing, you don’t know what they actually stole, and you don’t know what routes they took.”
— Matt Vega
Understanding that internal journey is now essential to identifying risk before a fraudster ever reaches the checkout stage. The institutions pulling ahead are reorganizing around the principal that trust must be evaluated continuously. It should not be assumed after a single verification event.
This shift requires a 360-degree holistic view that tracks risk signals across the entire customer journey, from onboarding through every session and account change. By analyzing the nuances of behavior, teams can distinguish between good journeys and automated attacks. This strategy requires that insights stay visible across fusion teams, uniting fraud, AML, and operations to break the chain of an attack before the money is gone.
What this means for 2026
If your fraud strategy still treats detection as the primary goal, you have some catching up to do.
In a landscape defined by sub second AI pivots, detection without the ability to act in real-time is just expensive documentation. The shift that matters in 2026 is moving from detection to interruption. This requires systems that can identify coordinated activity and break the chain before cash outs occur.
Bridging this gap requires three things most institutions still lack:
- Unified visibility: A single view where identity and payment signals are evaluated together rather than in silos.
- Persistent intelligence: Behavioral analysis tat continues throughout the entire customer lifecycle well beyond the initial onboarding event.
- Operational velocity: Defensive speed that matches the 400 millisecond response times of modern AI agents.
The fraudsters are already operating as systems. The question for 2026 is whether your defenses can do the same. You can dive deeper into these topics by catching up on our 2026 Fraud and AML trends webinar here.