"Every fraud that takes place passes KYC."
Steve Lenderman, Head of Fraud Prevention at iSolved, put it plainly on a recent Fraud Forward episode: KYC isn't broken. We just keep asking it to do the wrong job. It's the kind of observation that lands because most fraud teams already know it's true. Off-the-shelf deepfake kits go for $150 now. They're institution-specific, require no technical skill, and attackers have already built identity verification into their cost model. For them, your onboarding checks are a known friction point, not a barrier.
That puts the pressure back on us. The real question isn't whether KYC works, it's whether we've built the surrounding controls that let it work. That means assessing risk before a document ever gets submitted, layering in behavioral biometric signals alongside identity checks, and maintaining visibility throughout the full customer lifecycle, not just at the front door. One-time verification, no matter how rigorous, leaves most of that lifecycle dark.
The $150 fraud problem
Fraud-as-a-service has effectively turned identity verification into a commodity exploit. During our recent Fraud and AML Trends webinar, Chen Zamir, Head of Fraud Strategy at Sardine, detailed exactly how easily KYC can be defeated today. At this very moment, pre-packaged bypass kits are sold on dark web marketplaces, often targeted at specific financial institutions or vendors. Because these kits require zero technical skill to deploy, even low-level attackers can defeat traditional KYC layers at scale.
Fraud kits for bypassing specific KYC flows sell for as little as $150. These prices continue to drop as AI increases the supply of synthetic media and speeds up the development of new exploits, lowering the barrier to entry even further.
Deepfakes, synthetic identities, and liveness-check spoofing have made identity document verification increasingly unreliable as a standalone control. And this isn't limited to financial services. E-commerce platforms are seeing the same vulnerability exploited across their onboarding flows.
The result is a growing trust gap: institutions verify an identity at onboarding, assume that verification holds, and then are caught off guard when fraud materializes downstream from an account that "passed" every check.
Rethinking KYC as a three-layer system
Chen proposed a useful framework for how to think about this: KYC should be understood as three distinct layers, not one.
Pre-KYC is the risk-based detection layer that sits before identity verification even begins. This stage analyzes device fingerprints, behavioral biometrics, and the velocity of email or physical addresses to predict risk before a customer ever submits a document. These signals are relatively cheap to collect and act on, and they tend to catch a disproportionate share of fraud volume, which means fewer high-risk sessions ever reach the more expensive verification gate. For fintechs and smaller banks still skipping them this layer in favor of verification alone, that represents both a fraud exposure and an inefficiency in how KYC budget gets spent.
KYC itself functions as the active verification gate, incorporating document forensic analysis, biometric liveness telemetry, and authoritative data source matching. Because this layer is currently the primary target for industrialized fraud, it naturally commands the majority of institutional defense budgets.
Post-KYC is the layer most often neglected. Passing verification at onboarding does not guarantee a customer remains safe indefinitely, and yet most institutions still treat onboarding and transaction monitoring as separate disciplines with separate teams, separate vendors, and separate data. That separation is exactly the gap that sophisticated fraud exploits, and it's the clearest argument for why onboarding and transaction monitoring need to be managed as a unified discipline, not handed off between separate teams with separate vendors and separate data. Continuous monitoring of behavior, session patterns, and account activity is only meaningful when it's informed by what onboarding signals establish about that customer from day one.
The critical mindset shift here is moving away from binary decisions toward a continuous, risk-based assessment that evolves and adapts with the customer relationship.
The reality of continuous validation
Effective anomaly detection requires a deep understanding of what normal looks like for each customer. That means continuously building a behavioral baseline so that when something genuinely unusual occurs, it stands out against the pattern of that specific individual, not just against a generic rule.
The signals gathered during pre-KYC and KYC should feed directly into a risk classification for each customer (low, medium, or high) at the moment of onboarding. That classification then gets streamed through different risk strategies throughout the customer lifecycle. This is fundamentally different from traditional monitoring, which tends to look for behavior that matches a predetermined risk typology. A more effective approach uses those onboarding signals to build a baseline for each customer: low-risk customers get less friction and more latitude as the relationship develops, while high-risk customers get the opposite. That classification then becomes the lens through which all post-KYC monitoring is interpreted.
A customer sending a large wire may trigger an alert, but is it unusual for them? If that customer regularly sends international transfers of that size, the alert is noise. If a customer who has never sent a wire suddenly initiates one to a new payee after changing their notification settings, that's a clear signal.
The risk is evident because of the sequence, even if the transaction amount is modest.
Matt Vega, Sardine's Chief Fraud Strategist, makes a related observation: sophisticated fraud rings have learned to keep individual signals in the low-to-medium risk range, avoiding the high-risk triggers that traditional systems are designed to catch. Without a baseline risk profile anchored to that specific customer, those signals read as noise. With a baseline risk profile, the pattern becomes legible across the full user journey, connecting login behavior, account changes, payee additions, and transaction patterns into something that can actually be acted on.
Network graphs are no longer optional
One of the most emphatic recommendations from the webinar: if you don't have network graph capabilities, prioritize getting them.
Graph analysis allows teams to see how devices, identities, and data points are connected across their platform or a broader consortium. This can include anything from identifying a single phone number linked to dozens of accounts, an email address appearing across multiple institutions, or a device fingerprint shared by accounts with no legitimate relationship.
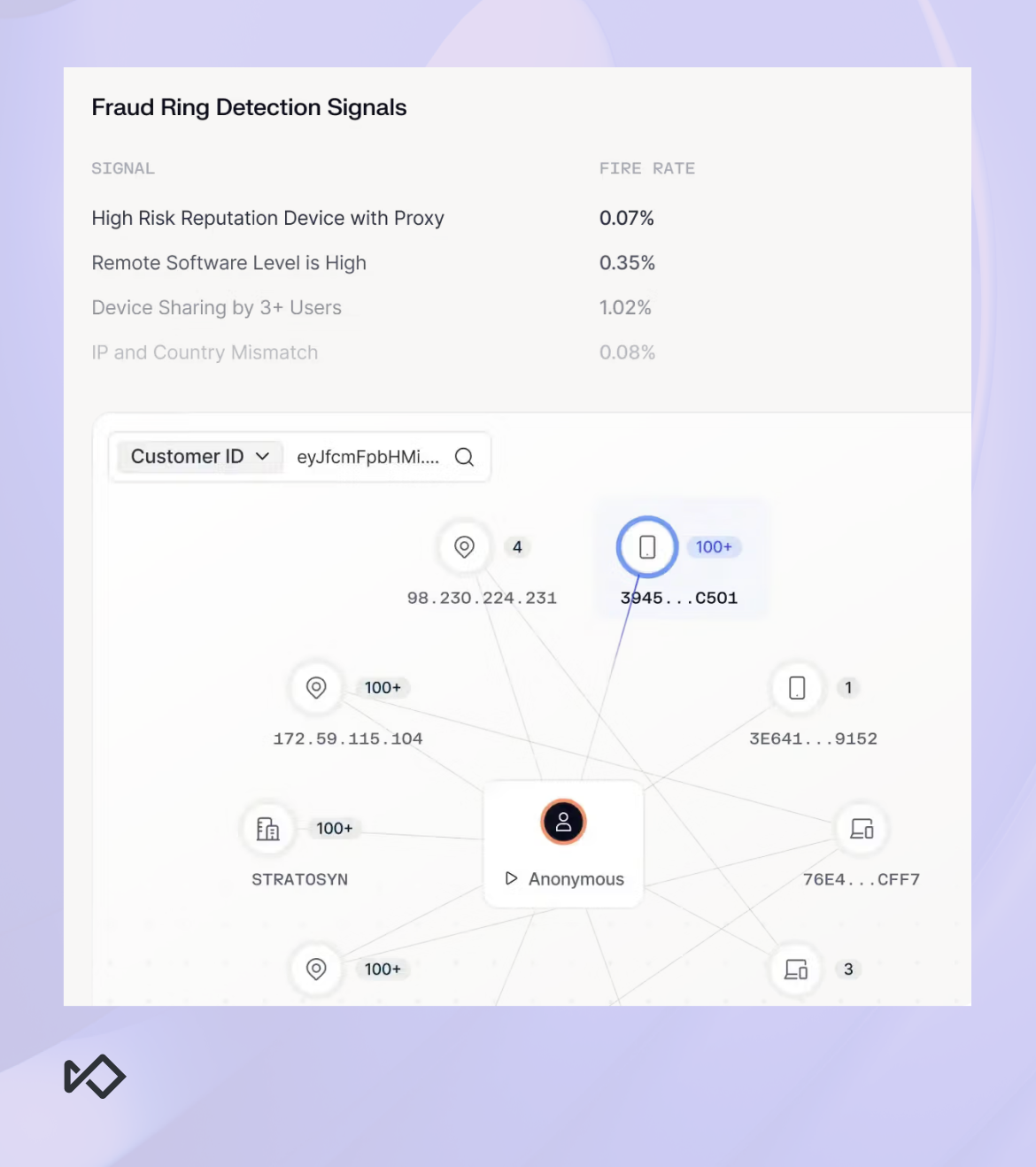
These connections are often invisible in traditional rule-based systems, yet they're exactly how coordinated fraud rings operate. Identifying these links is the only way to shut them down at scale. Vega described cases where a single link-analysis session could identify an entire ring and allow it to be shut down with one action, rather than chasing hundreds of individual alerts.
The convergence of fraud and AML
This shift also has significant implications for how fraud and AML teams work together. The U.S. Department of Treasury's National Money Laundering Risk Assessment flagged fraud as the top money laundering concern, a view echoed by regulatory bodies globally.
FinCEN reported that 42% of Suspicious Activity Reports were tied to identity-related activity, representing over $200 billion in suspicious transactions. When fraud and identity compromise are deeply intertwined with money laundering, treating them as separate disciplines creates a gap that criminals learn to exploit.
The institutions getting this right are building "fusion" models. This involves shared visibility and coordination across fraud, AML, disputes, call center, and security teams. The goal is to move away from managing each function in its own silo with its own vendors, data streams, and procedures.
What to do now
The path forward requires recognizing that KYC is a single layer within a system that must function as a unit. Improving your posture for 2026 involves three specific operational shifts:
- Filter the volume: Use pre-KYC to identify high-risk devices and behaviors before they ever reach your verification gates. This preserves your KYC budget and prevents your team from being buried in sophisticated deepfake noise.
- Establish the baseline: Maintain behavioral monitoring that persists throughout the entire customer lifecycle. If you only verify at onboarding, you are blind to account takeovers and the long-tail scams that materialize months later
- Identify the network: Deploy graph analysis to expose the hidden links between seemingly unrelated accounts. If a fraud ring is operating across your platform, link analysis is crucial to shutting down the entire operation.
Trust can no longer be a one-time decision anymore. In 2026, it has to be earned continuously.